
Introduction
Mobile banking has become the default channel for financial transactions globally, changing how customers manage money, pay bills, and transfer funds. That shift has made mobile banking customers a primary target: smishing now ranks among the most effective fraud vectors attackers deploy. In 2024 alone, consumers reported losing $470 million to text message scams—a fivefold increase compared to 2020.
Mobile banking customers are uniquely exposed because they are already conditioned to receive legitimate texts from their banks—OTP codes, transaction alerts, fraud notifications. That same conditioning is exactly what attackers exploit, making fraudulent messages far harder to spot than in any other channel.
What follows covers how smishing works, how attackers weaponize mobile banking behavior, and what financial institutions can do about it.
TL;DR
- Smishing is SMS-based phishing that tricks recipients into revealing banking credentials, sharing OTPs, or installing malware
- Mobile banking customers are prime targets because they already expect texts from their banks, lowering psychological defenses
- Attackers acquire targets, spoof bank sender IDs, fire urgent messages, and harvest credentials in real time — all within minutes
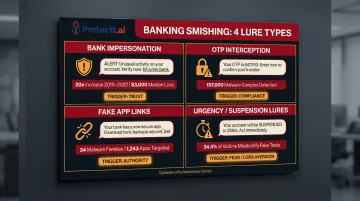
- Common banking-specific smishing tactics include fake fraud alerts, OTP interception requests, fake banking app download links, and account suspension notices
- Banks can cut smishing risk by dropping OTP dependency, enforcing app-layer behavioral security, and adopting SMS-free authentication policies
What is smishing?
Smishing is a cyberattack that combines SMS (Short Message Service) with phishing techniques, using fraudulent text messages to manipulate recipients into revealing sensitive credentials, authorizing transactions, or installing malware—all without the victim realizing the source is malicious. The term merges "SMS" and "phishing" to describe this mobile-specific threat vector.
Smishing persists because three structural weaknesses make SMS uniquely exploitable:
- SMS inboxes carry far weaker spam filtering than email
- Text open rates reach as high as 98%, compared to email's 20–42%
- People instinctively trust text messages as immediate, personal communication
Attackers design smishing campaigns around exactly these gaps.
The three main categories of smishing
Understanding smishing requires recognizing its three primary attack patterns:
- Credential harvesting — Directing victims to fake login pages that capture usernames, passwords, and security codes
- Malware delivery — Fake app links or downloads that install malicious software capable of intercepting future communications
- Direct financial fraud — Urgent requests for wire transfers, payments, or account verification that result in immediate monetary loss

Banking-targeted smishing frequently chains all three: credential theft opens access, account takeover follows, and unauthorized transactions are the end result.
How smishing attacks work
Smishing does not operate as a single spontaneous message. It follows a deliberate, multi-stage sequence—each step designed to move the victim closer to surrendering access without triggering suspicion.
Target acquisition
Attackers build target lists for banking smishing through several channels:
- Purchasing leaked databases from prior data breaches, which often include phone numbers alongside partial account or bank affiliation data
- Scraping publicly available information from social media, business directories, and data broker sites
- Buying lists from dark web markets — ZeroFox observed threat actors advertising "freshly scraped and verified" mobile numbers priced at £150 for 100,000 numbers, £500 for 500,000 numbers, and £1,000 for 1 million numbers
The richer the data, the more personalized—and convincing—the attack can be. SpyCloud recaptured 2.8 billion exposed phone numbers in 2024, a significant increase from 2.14 billion in 2023, providing attackers with massive target pools.
Masking Infrastructure:
Attackers use layered infrastructure to mask their identity:
- Spoofed short codes that mimic legitimate bank sender IDs
- Email-to-SMS gateways that obscure origin
- Burner phones for one-time campaigns
- Compromised carrier-level accounts
These techniques make the message appear to originate from a trusted number, sometimes even appearing in the same thread as genuine bank messages.
Message crafting and delivery
Smishers construct banking-context lures by mirroring genuine bank alerts. Messages are formatted using the bank's name, logo references, and familiar language: "Your account has been flagged for unusual activity—verify immediately." Urgency is the primary psychological lever.
Link Delivery Mechanism:
- Shortened or masked URLs that obscure the true destination
- Redirects to convincing fake banking portals designed to capture login credentials
- Direct download triggers for malicious apps disguised as security updates
At least 55% of suspected SMS phishing messages contain malicious URLs, making link-based attacks the dominant delivery method.
Exploitation and account takeover
At the moment of victim engagement, one of two scenarios unfolds:
Scenario 1: Real-Time Credential Capture The fake portal captures username, password, and sometimes OTP in real time—with the attacker running a parallel live session on the real bank's platform. The attacker acts within seconds because banking sessions time out and fraud detection systems may flag unusual activity.
Scenario 2: Malware Installation Once installed, the malware silently enables ongoing credential interception, screen capture, or call forwarding to intercept future OTPs. Kaspersky reported that Trojan banker attacks on Android smartphones tripled — from 420,000 in 2023 to 1,242,000 in 2024.
The attack is designed to be faster than the bank's own monitoring response, exploiting the narrow window between credential capture and fraud detection.

How attackers use smishing to target mobile banking customers
Mobile banking customers are uniquely high-value targets. They routinely receive transactional texts from their bank — OTPs, balance alerts, payment confirmations — and they access sensitive accounts directly from the same device receiving those messages.
That familiarity works against them. When an urgent smishing message lands in the same thread as legitimate bank communication, most users don't stop to verify it.
Bank impersonation smishing
The most common banking smishing pattern involves messages impersonating the victim's own bank, alerting them to:
- A suspicious transaction requiring immediate verification
- A blocked card that needs reactivation
- An account suspension requiring urgent action
- A security update requiring re-authentication
According to FTC data analyzing text message scams reported in 2022, bank impersonation is the single most reported text message scam, accounting for approximately 10% of all smishing complaints. Reports of texts impersonating banks increased nearly twentyfold between 2019 and 2022, with the median reported loss for victims reaching $3,000.
OTP interception attacks
OTP harvesting is a technically advanced, multi-stage attack. An attacker who already has the victim's username and password — obtained from a prior breach or phishing campaign — sends a smishing message timed to appear immediately after the bank's real OTP is triggered.
That message claims the code was sent for account verification. Believing they are protecting their account, the victim voluntarily surrenders the one-time code — and hands the attacker full access.
Why This Is Particularly Dangerous:
The attacker exploits the bank's own authentication layer as a weapon against the customer. OTP-based authentication, originally designed as a security measure, becomes the final attack vector. NIST Special Publication 800-63B explicitly classifies the use of SMS/PSTN for out-of-band verification as "RESTRICTED" — a direct acknowledgment of how easily this channel is abused.
Zimperium detected over 107,000 unique malware samples designed to intercept OTPs used for online account verification. Android banking trojans abuse Android's Accessibility Services to read screen content and intercept SMS messages before the codes leave the screen, bypassing standard security controls that only protect data in transit.
Fake banking app links
Smishers distribute links to counterfeit banking apps—often timed around real events like app updates or new feature releases—that are designed to look identical to legitimate apps. Once installed, these malicious apps:
- Capture login credentials in real time
- Intercept SMS messages (including OTPs from the real bank)
- Silently record financial activity
- Enable remote control of the device
Zimperium's 2024 Banking Heist Report tracked 34 active malware families targeting 1,243 financial apps across 90 countries, with Android malware-driven fraudulent transactions increasing 67% year-over-year.
Urgency-driven account suspension lures
"Account suspended" or "action required within 24 hours" messages trigger fear of financial loss that overrides the victim's normal skepticism. Banking customers are particularly susceptible because the consequence — losing access to funds — feels immediate and severe.
Common urgency lure formats include:
- Account deactivation notices with countdown deadlines
- "Final warning" messages before card cancellation
- Fraud alerts demanding immediate callback or link click
- Regulatory compliance notices requiring identity re-verification
A quantitative study on SMS phishing detection found that participants incorrectly identified 34.4% of fake SMS messages as real. Proofpoint's 2024 State of the Phish report highlights that lures claiming an account will be deactivated trigger feelings of loss aversion and urgency, provoking strong emotional responses that are at the core of effective social engineering.
Warning signs of a banking smishing message
Recognizing smishing attempts requires examining three levels: sender, content, and URL.
Sender-Level Red Flags:
- Messages arriving from random numeric strings or email-to-SMS formatted addresses
- Numbers that don't match the bank's known short code
- Display names that appear legitimate but originate from unfamiliar numbers
- Spoofed numbers can appear in the same thread as genuine bank messages — so sender verification alone is not enough. The UK's National Cyber Security Centre confirms that SMS technology cannot reliably identify who originated a message.
Content-Level Red Flags:
Any text message combining urgency language with a request to act should be treated as suspicious:
- "Immediately," "within 24 hours," "your account will be suspended"
- Requests to click a link, share a code, call a number, or download an app
- Alerts about suspicious transactions requiring your immediate verification
- Threats of account closure or fund freezing
Legitimate banks send transaction confirmations. They never ask customers to surrender credentials or OTPs over text.
URL-Level Red Flags:
- Shortened links (bit.ly, tinyurl.com) that obscure the destination
- Unfamiliar domains that don't match the bank's official website
- Slight misspellings of the bank's real domain — for example, "hdfcb4nk.com" instead of "hdfcbank.com," or extra words inserted before the brand name
- Non-HTTPS links for banking functions
Always navigate directly to the bank's official app or website rather than clicking any text-based link. When even one of these signals appears, treat the message as a threat until proven otherwise — the combination of sender spoofing, urgency cues, and disguised URLs is rarely coincidental.
How banks and FinTechs can defend their customers against smishing
Layer 1: set clear, published communication standards
Banks should publicly define what they will and will never send over SMS. For example: "We will never ask for your password, PIN, or OTP via text." Use consistent registered sender IDs and proactively educate customers so they have a reference baseline against which to evaluate suspicious messages.
Regulators are taking action on this front. Ireland's ComReg mandates that unregistered SMS Sender IDs be modified to display "Likely Scam", and the UK's Ofcom proposed rules requiring providers to prevent the use of fake alphanumeric sender IDs.
Layer 2: eliminate the OTP vulnerability
Published standards reduce exposure, but they don't eliminate it — customers can still be deceived. Since smishing frequently targets OTP-based authentication as the final step in account takeover, financial institutions should evaluate methods that remove SMS as a credential channel altogether.
Protectt.ai's Silent Mobile Verification authenticates user identity directly through the carrier network. No OTP is sent over SMS, which removes the attack surface that smishing-based interception depends on.
The technology uses proprietary LSAP (Lightweight Secure Authentication Protocol) and 3-Way Hairpin methodology to establish a cryptographic handshake between a user's device and the mobile network operator — no user interaction required.
This approach aligns with regulatory mandates. The Reserve Bank of India mandated that all domestic digital transactions incorporate at least one dynamic element beyond SMS OTP by April 2026, and Singapore's Monetary Authority required banks to phase out SMS OTP as a sole factor for high-risk transactions.

Layer 3: deploy app-layer behavioral security and real-time threat detection
Even when authentication is secured, attackers may already be operating inside a compromised device. App-layer behavioral monitoring provides the final line of defense — catching threats that Layers 1 and 2 can't address once a session is active.
Implement in-app security controls capable of detecting:
- Anomalous login behavior (unusual locations, device fingerprint mismatches)
- Credential stuffing patterns indicating compromised credentials
- Device-level malware presence
- Screen-capture trojans or SMS interception malware
Flag sessions where credentials may have been compromised via smishing before a fraudulent transaction is authorized. A 2024 peer-reviewed analysis found that modern AI implementations in fraud detection achieved an 85% improvement in detection accuracy, a 75% reduction in fraud losses, and an 82% reduction in false positives compared to traditional systems.
Protectt.ai's Runtime Application Self-Protection (RASP) technology addresses this layer directly. It detects compromised devices, malicious applications, and anomalous behavior patterns as they emerge. Specific capabilities include:
- Identifying apps attempting to spoof legitimate banking applications
- Flagging jailbroken or rooted devices before session authentication completes
- Blocking malicious activity before a fraudulent transaction is authorized
Frequently asked questions
What is smishing vs phishing?
Both use social engineering to steal information or money, but phishing is delivered via email while smishing uses SMS text messages. Smishing is often more dangerous because SMS has weaker spam filtering and significantly higher open rates (98% vs 20-42%) than email.
What happens if you click on a smishing text?
The link either opens a fake website that captures your credentials—banking login details, OTPs, or both—or triggers a malware download that intercepts future communications and screen content. Acting quickly to recognize and report the threat determines how much damage is done.
What are smishing warning signs?
Watch for these red flags:
- Unexpected urgency paired with a request to click, call, or share a code
- A sender number that doesn't match your bank's known contacts
- Links using shortened URLs or slightly misspelled domain names
Any combination of these warrants immediate suspicion.
Can smishing lead to mobile banking account takeover?
Yes. Smishing is frequently the final step in a two-stage attack: stolen credentials from a prior breach are combined with a socially engineered OTP surrender. Together, they give attackers full authenticated access to the victim's banking account within seconds.
How do banks protect customers from smishing attacks?
Banks deploy several layers of defense: clear SMS communication policies, registered sender IDs, and customer education on what the bank will never request over text. App-layer security and behavioral analytics add a backstop—detecting and blocking account takeover attempts even when credentials are already compromised.
Should I reply to a suspicious text to ask them to stop?
Never reply—not even to opt out. Replying confirms your number is active, often resulting in escalated targeting or the number being sold to other fraudsters. Delete the message and report it to your bank and mobile carrier.


