
TL;DR
- ATO on mobile banking apps exploits credential stuffing, phishing, SIM swapping, and malware to hijack accounts and commit fraud
- Mobile apps present unique attack surfaces—emulators, reverse-engineered APIs, and overlay attacks bypass traditional defenses
- Effective prevention layers app-level controls—MFA beyond OTPs, RASP, Zero Trust device binding, and real-time user behavior analytics
- Continuous monitoring catches attacks that static defenses miss, keeping fraud rates low as threat tactics evolve
What is account takeover and why are mobile banking apps high-risk targets?
Account takeover in banking occurs when an attacker gains unauthorized access to a legitimate customer's account—typically to commit fraud, drain funds, or exfiltrate sensitive data. Unlike general data breaches that focus on bulk record theft, ATO is targeted and immediately monetizable. Nearly one in three incidents in 2024 resulted in credential theft, with attackers using multiple pathways to quickly access and monetize stolen login information.
Mobile banking apps are disproportionately targeted because they combine high-value financial access with a complex attack surface spanning the device layer, app runtime, network layer, and identity layer—all of which can be exploited independently or in combination. The numbers reflect this: attacks on Android banking apps surged 196% in 2024, rising from 420,000 incidents in 2023 to 1,242,000 in 2024. Nearly 248,000 users encountered mobile banking malware that same year—a 3.6-fold increase from the previous year.
What makes mobile apps especially vulnerable is the attack surface they expose. Poorly obfuscated apps can be reverse-engineered to extract hardcoded API keys and authentication logic—giving attackers everything they need to craft direct API attacks that bypass the app entirely. The underlying security gaps are widespread:
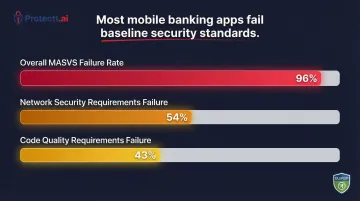
- 96% of mobile apps fail the OWASP Mobile Application Security Verification Standard (MASVS)
- 54% fail network security requirements
- 43% fail code quality requirements
How account takeover attacks happen on mobile banking apps
ATO on mobile banking is rarely a single-step attack. It typically exploits one or more specific weaknesses unique to the mobile environment.
Credential stuffing via automated bots
Attackers use large datasets of leaked username-password pairs and deploy bots to automate login attempts at scale against mobile banking app endpoints. Mobile apps' login APIs are especially vulnerable because they can be extracted through reverse engineering. In 2024, 44% of advanced bot traffic targeted APIs, with credential stuffing and ATO attempts rising 40% on APIs lacking adaptive MFA. The financial services industry absorbs 23% of all API attacks.
The pool of available credentials is massive. In January 2024, the "Naz.API" dataset was added to Have I Been Pwned, containing 71 million unique email addresses and 312 million rows harvested primarily from infostealer malware. Credential stuffing bots can mimic legitimate user behavior—simulated gestures, rotating IP addresses—to evade traditional rate-limiting and WAF controls.
Phishing and social engineering
Attackers craft convincing fake banking app interfaces, smishing messages, or fake customer care calls to trick users into revealing credentials, OTPs, or approving fraudulent transactions. Mobile-specific phishing variants are rising rapidly:
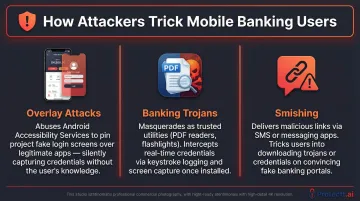
- Overlay attacks: Malicious apps like TeaBot and Copybara abuse Android Accessibility Services to display fake login screens over the real banking app, capturing credentials directly from the user's screen
- Banking trojans: Families like Mamont (36.7% of 2024 attacks), Anatsa, and Coper disguise themselves as legitimate apps—PDF readers, delivery trackers—to intercept authentication codes, log keystrokes, and initiate fraudulent transactions
- Smishing: 83% of mobile-targeted phishing attacks use SMS messages with malicious links to trick users into downloading trojans or entering credentials on fake mobile sites
In 2025, researchers tracked 34 active malware families targeting 1,243 financial institutions globally.
SIM swapping and OTP interception
Attackers convince telecom providers to transfer a victim's phone number to an attacker-controlled SIM, allowing them to intercept OTPs and bypass SMS-based two-factor authentication. In 2024, the FBI IC3 received 982 complaints related to SIM swapping, resulting in $25.9 million in losses.
SIM swapping is only part of the problem. SS7 protocol vulnerabilities expose SMS-based OTPs at the network level—attackers manipulate SS7 to make it appear as if a customer's device is roaming on a foreign network, rerouting OTPs before they reach the genuine user.
NIST SP 800-63B explicitly restricts use of the PSTN (SMS/Voice) for out-of-band authentication precisely because it is not phishing-resistant.
Mobile malware and app-layer exploits
Malware—banking trojans, spyware, screen readers—installed on rooted or jailbroken devices can log keystrokes, intercept session tokens, and relay real-time data to attackers. Zimperium data shows 1 in 400 Android devices are rooted, and 1 in 2,500 iOS devices are jailbroken—a surface area that cannot be ignored.
The app layer itself is an equally exposed target. Attackers reverse-engineer poorly obfuscated banking apps to extract hardcoded API keys, server URLs, and authentication logic—then craft direct API attacks that bypass the app entirely. A NowSecure analysis found that 55% of monitored apps were run in a debugger or with modified code over a 28-day period.
Dynamic instrumentation tools like Frida let attackers inject JavaScript into running apps, bypassing SSL pinning, root detection, and authentication checks in real time. Yet a Promon study found that only 2% of top Android apps actively identified an unmodified Frida attack out of the box.
The consequences of ignoring ATO prevention in mobile banking
Account takeover fraud resulted in $15.6 billion in reported losses in the U.S. in 2024, up from $12.7 billion in 2023. For every $1 lost to fraud, it costs North American financial institutions an average of $4.41 in recovery, investigation, and legal fees.
Beyond direct financial losses, ATO destroys customer lifetime value. 75% of consumers are ready to switch banks over inadequate fraud protection, and 67% would consider switching after a serious data breach. 43% would stop using a banking app entirely after their account was compromised — a loss that rarely reverses.
Customer attrition is only half the exposure. Regulators are also stepping up enforcement, with penalties that make weak ATO controls a direct liability:
- CFPB (US, 2025): $175 million penalty to Block (Cash App) for weak security protocols and incomplete ATO investigations
- FCA/PSR (UK, 2024-2025): £173 million reimbursed to victims under new mandatory Authorized Push Payment (APP) fraud rules
- PCI DSS v4.0: Requirement 8 mandates multi-factor authentication for all access into the Cardholder Data Environment and requires systems to prevent credential abuse
- GDPR Article 32: Requires technical measures to ensure confidentiality and system resilience — non-compliance has triggered fines exceeding €20 million or 4% of global annual turnover under enforcement actions across the EU

Warning signs your mobile banking app is under ATO attack
Early detection relies on behavioral and technical signals. Security teams should monitor:
- Spike in failed login attempts from unusual geographies or device profiles; multiple account access attempts within implausibly short timeframes
- Sudden change in user device fingerprint or SIM associated with an account followed by high-value transaction attempts
- Surge in reported unauthorized activity or OTP requests the account holder did not initiate
How to prevent account takeover attacks on mobile banking apps
Effective ATO prevention requires defense at every layer—app, device, network, and identity—not just at the authentication gate.
Implement strong MFA that goes beyond OTP
SMS OTP alone is insufficient. NIST SP 800-63B states that "OTP authentication is not phishing-resistant" and warns that verifiers should consider risk indicators like SIM changes or number porting before using SMS. Layered authentication combines:
- Biometric verification: Use local biometric activation (FaceID, fingerprint) to unlock cryptographic keys stored in secure enclaves, not transmitted over networks
- Device binding: Bind accounts to specific, verified devices so that even if credentials are stolen, access from an unregistered device is blocked automatically
- Behavioral signals: Monitor typing rhythm, swipe patterns, and session duration to differentiate legitimate users from attackers
Zero Trust Device and SIM Binding extends this further by tying accounts to a verified SIM—so even a credential-perfect login attempt from an unregistered SIM is rejected at the app layer.
Deploy Runtime Application Self-Protection (RASP)
RASP monitors and protects an app from within its own runtime environment, detecting and blocking attacks—tampering, emulator use, overlay injection, reverse engineering attempts—in real time without requiring network calls. RASP is particularly effective for mobile banking because it secures the app even when the device is compromised.
Protectt.ai's platform, for instance, embeds RASP directly into the app SDK with zero performance overhead—covering all of the following detection surfaces without requiring server-side calls:
- Real-time detection of overlay attacks, emulator execution, and tampering
- Device integrity checks (root/jailbreak detection)
- Anti-reverse engineering controls
- Malware and spyware detection
- Protection against dynamic instrumentation (Frida detection)
When to implement RASP: At the development/SDK integration phase, before app release—not as a post-breach retrofit. RASP should be embedded into the mobile app CI/CD pipeline as a security gate, ensuring runtime protections are in place before deployment.
Harden API security and apply code obfuscation
Banking app APIs are a primary target. Enforce certificate pinning and mutual TLS (mTLS) to ensure only the legitimate app binary can communicate with backend APIs, blocking bot-crafted direct API calls. Certificate pinning ensures the app trusts only the intended remote hosts, preventing Man-in-the-Middle attacks and API interception.
Code obfuscation prevents reverse engineering by:
- Renaming variables, classes, and methods with random alphanumeric strings to mask their true purpose
- Encrypting embedded API keys and server endpoints with AES so attackers cannot extract credentials from compiled binaries
- Injecting dead code and false branches into authentication logic, making login flows impractical to replicate or intercept
- Scrambling control flow to prevent attackers from mapping business logic or authentication mechanisms

Block weaponized environments at the app layer
Most ATO bots depend on non-standard environments to operate—emulators, rooted devices, and ADB-connected setups give attackers the automation layer they need for credential stuffing at scale. Blocking execution in these environments cuts off that infrastructure at the app layer.
Key environments and tools to detect and block:
- Emulators and simulators used to automate credential injection
- Rooted or jailbroken devices that bypass OS-level security controls
- ADB-connected environments that expose the app to external command execution
- Dynamic instrumentation frameworks like Frida (
frida-serverpresence, memory anomalies, attached debuggers)
Deploy AI-driven behavioral analytics and threat intelligence
Continuous user behavior monitoring establishes baselines of normal behavior per user—transaction patterns, session duration, typing rhythm, location—and flags deviations in real time, enabling pre-transaction fraud prevention without adding user friction. AI/ML models differentiate between legitimate users, bots, and fraudsters operating via Remote Access Trojans (RATs).
Protectt.ai's behavioral analytics layer, for example, monitors the following signals continuously to identify ATO attempts before account compromise occurs:
- Typing patterns and touchscreen gestures
- Motion patterns and device orientation
- Geolocation data and network environment
- VPN/proxy detection and mock location identification
- Session duration and app usage patterns

Real-world results: A top U.S. credit union reduced residual Zelle fraud losses by 95% in two months using behavioral biometrics, while a UK bank detected 81% of fraudulent activity and recovered £1.5 million in prevented losses within six months. These outcomes reflect what consistent behavioral signal monitoring delivers across markets—regardless of geography.
Long-term strategies to sustain ATO prevention
Sustainable ATO prevention isn't a one-time project — it's an ongoing practice built on three pillars.
Shift security left in your development pipeline. Integrate security testing, threat modeling, and RASP controls into your CI/CD process rather than bolting them on post-release. Treat security as a release gate, not an afterthought. NIST SP 800-218 (Secure Software Development Framework) notes that shifting left minimizes technical debt and cuts the cost of remediating vulnerabilities.
Monitor threat intelligence continuously. Review feeds for newly leaked credential databases, emerging ATO tactics targeting banking apps, and dark web mentions of your institution. Detection rules need proactive updates — attackers don't wait for your quarterly review cycle.
Run red team exercises against mobile-specific ATO vectors. Generic penetration testing isn't enough. Simulate the attacks your banking app actually faces:
- Credential stuffing and password spray scenarios
- SIM swap and number-porting test cases
- Overlay injection and screen-capture attacks
- API manipulation and dynamic instrumentation (for example, using Frida)
Use findings to harden controls before attackers find the same gaps.
Frequently asked questions
What is account takeover in banking?
ATO in banking occurs when a cybercriminal gains unauthorized access to a customer's bank account by stealing or bypassing login credentials, then uses the access to commit fraud, transfer funds, or steal identity information.
How does account takeover happen?
ATO exploits multiple attack paths. Common methods include:
- Credential stuffing using breached username/password databases
- Phishing and social engineering to harvest login details
- SIM swapping to intercept OTPs before they reach the user
- Mobile malware or app-layer exploits that extract credentials or session tokens
What are the red flags for account takeover?
Key warning signs include unusual login attempts from new devices or geographies, unexpected OTP requests users didn't initiate, sudden changes in account contact information or device fingerprints, and unexplained transaction activity.
What is account takeover prevention?
ATO prevention combines technical controls (MFA, RASP, device binding, behavioral analytics) with operational practices. Together, these measures help banks and FinTechs detect and block unauthorized access attempts before fraud occurs.
How to protect a mobile banking app?
Core protections include:
- Implementing RASP for runtime threat detection
- Enforcing code obfuscation and certificate pinning
- Enabling root and emulator detection
- Binding accounts to verified devices and SIMs
- Deploying AI-driven behavioral monitoring for real-time anomaly detection
Is it safe to keep banking apps on your phone?
Banking apps are safe when downloaded from official sources, used on updated OS versions, and installed on non-rooted devices. Banks that deploy runtime protections like RASP and device binding add a critical extra layer of defense.


