
The core problem facing banking institutions today is dangerous: most banks embed third-party security SDKs without fully understanding whether those tools address banking-specific threats like overlay attacks, SIM swap fraud, or reverse engineering. This creates blind spots that attackers actively exploit, targeting the seams between an SDK and the host application rather than the SDK itself.
This guide covers what a mobile app security SDK for banking is, the unique threats it must address, the capabilities every banking SDK needs, how RASP works, compliance requirements, and how to evaluate vendors effectively.
TLDR
- A mobile app security SDK for banking embeds directly into a bank's mobile app to provide real-time protection against fraud, tampering, and data theft
- Banking apps face unique threats—overlay attacks, screen capture malware, SIM swap fraud—that generic security tools cannot counter
- Comprehensive banking SDKs must include RASP, AI-driven threat intelligence, device binding, and behavioral analytics
- Verify PCI DSS, ISO 27001, and central bank digital security certifications before shortlisting any banking security SDK
- Evaluate vendors based on feature depth, integration overhead, false positive rates, and proven deployment with regulated financial institutions
What is a mobile app security SDK for banking?
A mobile app security SDK for banking is a collection of pre-built security libraries and modules that developers embed into iOS or Android banking apps to enforce protections at the application layer. Unlike server-side or network-layer tools that operate externally, a banking SDK integrates directly into the app's codebase, creating a security boundary within the application itself.
Banking-specific SDKs differ from general mobile security solutions because they're built around financial threat models, not generic app integrity concerns. They must address threats specific to financial services:
- Account takeover and transaction fraud — real-time detection during active money transfers
- Social engineering attacks targeting authentication flows and credential theft
- Regulatory compliance with frameworks like PCI DSS and central bank digital security mandates
- Audit trail integrity for forensic investigation and supervisory reporting
A common misconception is that integrating any secure SDK is sufficient. In reality, an SDK secures its own code boundary but cannot protect the rest of the application or its interactions with the operating system and device sensors.
The SDK's internal functions may be hardened while vulnerabilities in the host app — insecure data storage, unprotected API calls, weak authentication — remain fully exposed. Effective banking app security requires the SDK to work alongside secure coding practices throughout the entire application.
Why mobile banking apps face unique security threats
Overlay and screen capture attacks
Malicious apps render fake user interfaces on top of legitimate banking apps to harvest credentials or capture one-time passwords. These overlay attacks are particularly prevalent in banking because attackers know the exact screens where users enter sensitive information—login pages, transaction confirmation screens, and OTP entry fields.
The attack monitors which app is in the foreground, then instantly overlays a convincing replica of the banking interface. Users believe they're interacting with their bank, but every keystroke flows to the attacker. Screen capture malware operates the same way—silently recording passwords, balances, and transaction details as they appear on screen.
Reverse engineering and app tampering
Attackers decompile banking APKs or IPAs to extract hardcoded tokens, map API logic, or create fraudulent clones used in phishing campaigns. The exposure is substantial — attackers gain access to:
- Authentication flows that reveal how the app verifies user identity
- Encryption keys protecting data in transit
- Business logic governing transaction limits and approval workflows
- Hardcoded API endpoints that expose backend communication sequences
Tampered app versions use this knowledge to bypass security checks, disable fraud detection, or inject code that exfiltrates data to attacker-controlled servers.
SIM swap fraud and account takeover
SIM swap fraud occurs when attackers port a victim's phone number to a SIM card they control, intercepting SMS-based one-time passwords. This makes device-level identity binding critical — the app must verify not just that the correct phone number is in use, but that the specific physical device and SIM card combination matches the original registration.
Without device binding, stolen credentials plus a successful SIM swap equals full account takeover — password resets, transaction approvals, and fund transfers all become trivially accessible to the attacker.
Device-level risks
Three device-level conditions expose banking apps to serious risk:
- Rooted/jailbroken devices remove OS security boundaries, giving attackers access to restricted functions and memory
- Emulators let attackers run banking apps in controlled environments to manipulate inputs, observe internal state, and test exploits without detection risk
- Hooking frameworks like Frida enable runtime manipulation — intercepting function calls, modifying return values, and bypassing checks while the app runs
For banking apps specifically, this translates to disabled certificate pinning, bypassed biometric authentication, and transaction amounts altered before they reach the backend.
Real-world SDK bypass attacks
Threat actors increasingly target the seams between an SDK and the host app rather than attacking the SDK directly. Examples include:
- KYC facial recognition spoofing: Attackers inject synthetic video feeds that bypass the SDK's liveness detection, allowing fraudulent account creation
- Malware disabling SDK-to-app connections: Malicious code intercepts the communication channel between the security SDK and the host application, preventing threat alerts from triggering protective actions
- PCI MPOC gaps: Mobile point-of-sale applications that meet PCI Mobile Payment on COTS (MPOC) requirements but fail to secure the integration points between payment SDKs and the host app, creating exploitable vulnerabilities

Core security features every banking SDK must have
Runtime Application Self-Protection (RASP)
RASP embeds detection and response logic directly into the app runtime, enabling the app to detect attacks and react—block execution, alert security teams, or terminate sessions—without waiting for an external signal. For banking apps, this matters because attacks happen during live sessions, and defensive responses must be equally immediate.
RASP operates within the application's execution environment, continuously monitoring for threats while the app is running. When suspicious activity is detected, the response is instantaneous—targeted to the specific threat type.
Code obfuscation and anti-tampering
Code obfuscation makes reverse engineering prohibitively difficult by transforming readable code into functionally equivalent but incomprehensible logic. In practice, this means:
- Variable names become random strings
- Control flow is restructured with illogical jumps
- String constants are encrypted until runtime
Integrity checks detect whether the app binary has been modified post-distribution by validating cryptographic signatures and checksums. Both must work in tandem: obfuscation raises the cost of analysis, while integrity checks detect when attackers succeed despite obfuscation.
Zero trust device binding and identity verification
Device fingerprinting and SIM binding tie a banking session to a specific authenticated device, making stolen credentials alone insufficient for account takeover. The system creates a unique identifier based on device hardware characteristics, operating system version, and SIM card details, then validates this identifier with every session.
Advanced implementations eliminate OTP dependency through carrier-network verification. The banking app communicates directly with mobile carrier networks to confirm the device initiating the session matches the registered SIM card—no manual code entry required.
AI/ML-powered threat intelligence and behavioral analytics
Continuous monitoring of user behavior and transaction patterns enables anomaly detection that identifies fraud in real-time. Unlike rule-based fraud detection that relies on predefined thresholds (for example, "flag transactions over ₹10,00,000"), behavioral analytics learns normal patterns for each user and detects deviations.
The system analyzes signals across multiple dimensions:
- Typing speed and touchscreen pressure
- Swipe patterns and transaction timing
- Geographic location and device context
When behavior deviates significantly—a transaction from a new device in a different country with atypical input patterns, for instance—the system can require additional authentication or block the transaction outright.

Secure communication controls
Certificate pinning prevents man-in-the-middle attacks by validating that the server's SSL certificate matches the expected certificate embedded in the app. Encrypted communication channels protect data in transit. Network traffic integrity checks detect when communications are being intercepted or modified.
These controls work together to ensure that even on compromised networks—public Wi-Fi, corporate proxies, or networks under active attack—the banking app maintains secure communication with backend systems.
Screen protection and keyboard security
The user interface is a distinct attack surface that code-level protections don't cover on their own. Banking SDKs must address it directly:
- Block screen capture to prevent malware from recording sensitive data
- Restrict third-party keyboard access that could log keystrokes
- Detect overlay attacks at the UI layer before credentials are entered
Together, these controls close the gap between internal code security and the moment a user actually interacts with the app.
Platforms like Protectt.ai consolidate all six of these layers—RASP, code obfuscation, device binding, behavioral analytics, secure communications, and screen protection—within a single lightweight SDK trusted by institutions including RBL Bank, Yes Bank, Bajaj Finserv, and LIC.
How RASP works inside a banking security SDK
Unlike perimeter defenses that operate outside the app, RASP instruments the app's own runtime environment—it monitors execution context, intercepts suspicious function calls, and enforces security policies from within the running application.
Detection mechanics
RASP continuously checks for indicators of compromise during runtime:
- Flags debugger attachment the moment any debugging tool connects to the app process
- Identifies Frida, Xposed, or similar hooking frameworks attempting to intercept function calls
- Recognizes emulator environment signatures that indicate the app isn't running on physical hardware
- Validates code and resource integrity against the original build to catch post-installation tampering
Legitimate users never notice these checks. When the app runs in a clean environment, there's no visible impact on the user experience.
Response options
RASP enables configurable responses based on threat severity:
- Graceful degradation: Disables high-risk features like money transfers while keeping read-only functions available
- Forced re-authentication: Prompts identity verification before the session can proceed
- Silent alerting: Notifies the security operations center without tipping off the attacker
- Full session termination: Closes the app immediately and forces a clean re-login
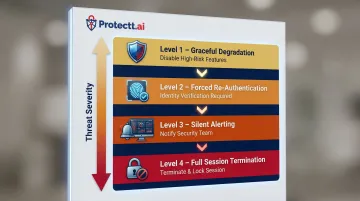
The response can be tailored to the specific threat—a rooted device might trigger forced re-authentication, while active hooking framework detection might result in immediate session termination.
RASP vs. static protections
**Static analysis and obfuscation** harden the binary before deployment, raising the cost of reverse engineering. RASP picks up where static defenses leave off — operating inside the live execution environment where attacks actually land.
The two layers complement rather than replace each other. Static protections make analysis harder upfront; RASP detects and responds to attacks that succeed despite those defenses.
Performance impact is minimal. According to research on RASP performance monitoring, checks run lightweight and asynchronous, with most implementations adding less than 5% overhead to transaction processing time.
Compliance and regulatory requirements your banking security SDK must meet
PCI DSS alignment
The Payment Card Industry Data Security Standard (PCI DSS) establishes specific requirements relevant to mobile banking apps: secure network architecture, encrypted data storage, strict access controls, and regular security testing. A banking security SDK should provide controls that directly map to these requirements, reducing compliance audit burden.
For example, PCI DSS Requirement 6.5.6 addresses memory corruption vulnerabilities, which a well-implemented SDK addresses through runtime memory protection. Requirement 8.2 on multi-factor authentication aligns with device binding capabilities that create a second authentication factor beyond passwords.
Central bank and regional mandates
Regulators have issued specific guidelines on mobile banking security, data localization, and fraud prevention that banks must demonstrate compliance with. In India, the Reserve Bank of India's Digital Payment Security Controls mandate specific protections including device binding, session management, and fraud monitoring.
Similar frameworks apply across other jurisdictions:
- MAS (Singapore) — Technology Risk Management guidelines covering mobile app integrity and transaction security
- EBA PSD2 (Europe) — Strong Customer Authentication requirements for payment initiation and account access
- HKMA (Hong Kong) — Cybersecurity guidelines specifying authentication, encryption, and incident response standards

Each of these frameworks prescribes specific technical controls, which means the SDK you choose directly determines whether your app passes a compliance audit — not just a security review.
ISO standards and data privacy
ISO 27001 certification confirms that an SDK vendor has implemented comprehensive information security management systems. ISO 22301 covers business continuity, ensuring the vendor can maintain security protections through disruptions. When evaluating vendors, these certifications signal genuine institutional commitment to security — not just product-level claims. Protectt.ai, for instance, holds both certifications alongside PCI DSS compliance.
GDPR and equivalent data protection laws add another layer of requirements. The SDK must process personal data lawfully, apply data minimization to behavioral telemetry, and support users' privacy rights. These obligations sit alongside — not in place of — the active threat monitoring the SDK performs.
How to choose the right mobile app security SDK for banking
Evaluation criteria checklist
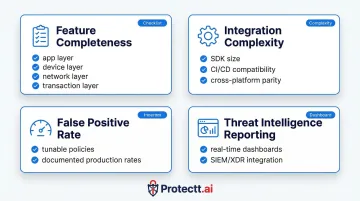
Use these four criteria to evaluate any candidate SDK before committing to a deployment:
- Feature completeness — Covers all attack surfaces: app, device, network, and transaction. Should detect overlay attacks, prevent reverse engineering, validate device integrity, and monitor transaction behavior.
- Integration complexity — Minimal SDK size and performance overhead, with feature parity across iOS and Android. Deployable through CI/CD pipelines without manual code rework.
- False positive rate — Documented low false-positive rate in production. Security policies should be tunable so legitimate users aren't blocked.
- Threat intelligence reporting — Real-time dashboards for detected threats and security events. Native integration with SIEM or XDR platforms is a strong differentiator.
Certifications and compliance coverage
The vendor should hold relevant certifications including PCI DSS, ISO 27001, and ISO 22301. The SDK's controls should map to:
- OWASP Mobile Top 10
- OWASP Mobile Application Security Verification Standard (MASVS)
- Central bank and regional regulatory guidelines
According to the QKS Group SPARK Matrix for In-App Protection 2025, vendor certifications accelerate the bank's own compliance posture by providing pre-audited controls that map directly to regulatory requirements.
Vendor track record with regulated financial institutions
Evaluate reference customers in banking and fintech. Protectt.ai is deployed across 25+ financial institutions — banks, insurance companies, and securities firms — and holds ISO 27001, ISO 22301, PCI DSS, and ISO 42001 certifications. The platform has received recognition including Cybersecurity Company of the Year 2023 and carries a Gartner Peer Insights rating of 4.9/5.
That kind of regulated-sector deployment history means the vendor has already navigated the audit requirements and system integration constraints your institution will face.
Frequently asked questions
What is a mobile app security SDK for banking?
It's a pre-integrated security library embedded in a banking app's codebase that enforces runtime protections—covering fraud prevention, anti-tampering, and identity verification—without requiring the bank to build these capabilities from scratch.
How does RASP protect mobile banking applications?
RASP monitors the app's execution environment in real-time, detects threats like debugger attachment or hooking frameworks at the moment they occur, and responds automatically, blocking attacks before they can exploit the application.
What threats does a mobile banking security SDK protect against?
Primary threats include overlay and screen capture attacks, reverse engineering and app tampering, SIM swap and account takeover, man-in-the-middle network attacks, and device-level risks from rooted or emulated environments.
Can a banking security SDK be integrated without impacting app performance?
A well-engineered SDK uses lightweight, asynchronous checks that add negligible latency and minimal binary size increase. Before integration, evaluate the vendor's published performance benchmarks and test under your app's expected load conditions.
What compliance standards should a banking security SDK support?
The SDK should support PCI DSS, ISO 27001, OWASP Mobile Top 10, and central bank mandates relevant to your region. A vendor holding these certifications directly—rather than simply claiming alignment—provides stronger assurance of actual control rigor.
Is a security SDK alone sufficient to protect a mobile banking app?
A banking security SDK secures its own code boundary, but the host application still interacts with the OS, sensors, and third-party libraries that sit outside that boundary. Full protection requires layering in RASP, API security, and device binding to cover those additional attack surfaces.


