
This guide covers the authentication methods reshaping banking security—from legacy PINs and OTPs to advanced biometrics and silent carrier-based verification—plus the key security considerations and best practices that banking professionals and app developers need to deploy authentication that stops fraud without destroying user experience.
TLDR
- Mobile authentication uses what you know (PIN), have (device/SIM), or are (biometrics)—MFA is now the baseline standard
- SMS OTPs face 10–15% delivery failures and are vulnerable to SIM swap attacks, prompting regulatory phase-outs by 2026
- Server-side biometrics match live captures to KYC-enrolled templates, unlike device biometrics that only confirm phone possession
- Silent mobile verification and device-SIM binding remove OTP friction while blocking account takeovers via cryptographic network handshakes
- Adaptive authentication scales verification to transaction risk: minimal friction for balance checks, strong MFA for high-value transfers
The threat landscape making mobile authentication non-negotiable
Mobile banking fraud is accelerating fast. In 2025, fraud scams drained $62 billion from the global financial system—a 19.3% increase since 2023. Juniper Research projects a 153% surge by 2030, with losses rising from $23 billion in 2025 to $58.3 billion globally, driven heavily by synthetic identity fraud and account takeover attacks.
This explosion correlates directly with mobile banking adoption. As of 2024, mobile money surpassed two billion registered accounts and over half a billion active monthly users globally. More users mean more attack surface—and fraudsters are exploiting every vulnerability.
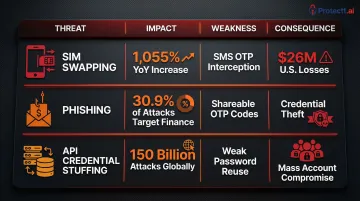
Three critical attack vectors targeting mobile banking
SIM Swapping: Fraudsters bypass digital security by compromising the telecom layer itself. The UK's fraud prevention service, Cifas, reported a 1,055% increase in unauthorized SIM swaps in 2024, rising to nearly 3,000 cases. In the U.S., the FBI's Internet Crime Complaint Center tracked $26 million in SIM swap losses in 2024 alone. Once attackers control your phone number, they intercept SMS OTPs and take over accounts.
Phishing and Social Engineering: These attacks bypass knowledge-based factors by tricking users into revealing credentials or OTP codes. The Anti-Phishing Working Group documented over 1 million phishing attacks in Q1 2025, with attacks against financial sectors comprising 30.9% of all phishing attempts. The attack model is straightforward: fake banking sites mimic legitimate ones pixel-for-pixel, capturing credentials and OTPs before the user realizes anything is wrong.
API Credential Stuffing and Account Takeover: Mobile apps rely heavily on APIs for login workflows. Akamai documented over 150 billion API attacks from January 2023 through December 2024, making these endpoints the primary vector for automated attacks—with financial services absorbing 79 billion of those hits. Fraudsters use stolen credentials from data breaches to systematically test login endpoints until they find valid combinations.
| Threat Vector | 2024-2025 Impact | Primary Weakness Exploited | Business Consequence |
|---|---|---|---|
| SIM Swapping | 1,055% YoY increase (UK) | SMS OTP interception | Direct account takeover; $26M US losses |
| Phishing | 30.9% of all attacks target finance | Shareable OTP codes | Credential theft; regulatory scrutiny |
| API Credential Stuffing | 150B attacks globally | Weak password reuse | Mass account compromise; $87B annual security cost |
Why mobile-first banking amplifies risk
Mobile-first banking stacks multiple risk factors that simply don't exist in controlled desktop environments. Devices move across public Wi-Fi and cellular networks, run operating systems with inconsistent update cycles, and lean on convenience features—saved passwords, auto-fill—that quietly erode security posture.
Users expect instant access. That expectation pressures security teams to reduce authentication friction, even in high-risk scenarios where stronger verification is exactly what's needed.
Core mobile authentication methods: from passwords to biometrics
Authentication factors fall into three categories: something you know (password, PIN), something you have (device, OTP token), and something you are (biometrics). Combining two or more factors—multi-factor authentication (MFA)—is now the minimum standard in banking because single-factor authentication cannot withstand modern attack sophistication.
Tier 1: common in-app authentication methods
These methods remain the most widely deployed despite growing security concerns:
SMS/Voice OTP: About 74% of banks send customers one-time codes via SMS or automated phone calls, making this the most common in-app method. Yet SMS OTPs carry 10-15% delivery failure rates and are vulnerable to SIM swap attacks — the codes are shareable secrets users can be socially engineered into handing over.
Password/PIN Entry: Familiar but fragile. Passwords are vulnerable to credential stuffing, keylogging malware, and shoulder surfing. Reused or weak PINs amplify the risk considerably.
Card Detail Verification: Some apps require users to enter card numbers, CVV codes, or card expiration dates. This adds a possession factor (the physical card) but creates friction and doesn't verify the person entering the details is the legitimate cardholder.
Tier 2: intermediate authentication methods
Where Tier 1 methods fall short, these approaches offer a stronger security-to-friction ratio for targeted scenarios:
Email OTP: Delivered to the inbox rather than via carrier network, making it more resistant to SIM swap attacks. The tradeoff: a compromised email account negates the advantage, and spam filters can delay delivery.
Authenticator Apps (TOTP): Time-based one-time password apps like Google Authenticator generate codes locally on the device, eliminating SMS interception risk. Users must manually enter the code, adding friction, but the method is phishing-resistant if implemented correctly.
Security PINs and Secure Email Links: Security PINs provide a knowledge factor with lower entropy than passwords. Secure email links (magic links) send a time-limited URL that authenticates the user when clicked, reducing password fatigue but requiring email access.
Tier 3: innovative and emerging in-app authentication
Advanced methods provide stronger security with reduced user friction:
In-App Face Recognition: Distinct from device FaceID, in-app face recognition captures a selfie within the banking app and compares it server-side to the face verified during KYC/onboarding. This ensures identity continuity—the person transacting now is provably the same person who opened the account.
Selfie Video with Liveness Detection: Users record a short video performing specific actions (blinking, turning head) to prove they're a live person, not a photo or deepfake. ISO/IEC 30107-3 certified liveness detection is becoming baseline for banking-grade biometrics to combat AI-generated deepfakes.
Voice Biometrics: Analyzes unique vocal characteristics—pitch, tone, cadence—to verify identity. Useful for phone banking and voice-activated transactions, though vulnerable to high-quality voice synthesis attacks.
Behavioral Biometrics: Monitors typing cadence, swipe patterns, touch pressure, and navigation behavior to create a unique behavioral profile. This enables continuous, passive authentication throughout the session — no user action required. Protectt.ai's platform uses these signals to detect behavioral anomalies in real time, flagging account takeover attempts before a transaction completes.
Step-up authentication for high-risk actions
Step-up (or adaptive) authentication requires only standard verification for low-risk actions like checking balances or viewing history, but triggers stronger verification for high-risk events: large transfers, changing account details, or adding new payees.
How it works: The system assigns a risk score to each action based on signals including:
- Transaction amount relative to the user's typical behavior
- Payee status (known recipient vs. new beneficiary)
- Device trust level and session location
- Real-time behavioral anomalies
Low-risk actions proceed without friction. High-risk actions trigger an additional verification step — biometric check, OTP, or security question — before the transaction clears.
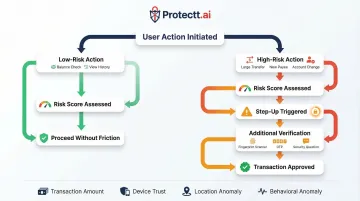
The result: users move through routine tasks without interruption, while the bank maintains strong protection precisely where exposure is highest.
Local vs. server-side biometrics: what banks need to know
Not all biometric authentication is equal. The distinction between local (device-bound) and server-side biometrics determines whether your bank achieves true identity assurance or just device possession verification.
The limitation of local (device-bound) biometrics
Local biometrics—Apple FaceID, Android fingerprint—operate entirely on the device. The biometric template never leaves the phone; it's stored in a hardware-backed Secure Enclave. When a user authenticates, the device compares the live biometric capture to the stored template locally and returns a simple yes/no result to the app.
The problem: Local biometrics only prove possession of the phone, not true identity. If an attacker knows the device PIN or passcode, they can disable FaceID and re-enroll their own face. Local biometrics cannot be linked back to the face verified during KYC/onboarding, breaking the chain of identity assurance required for high-value banking transactions.
Apple's Platform Security guide notes that the probability of a random person unlocking a device using Face ID is less than 1 in 1,000,000. That's excellent for device unlock, but insufficient for verifying the person transacting is the same person who opened the account.
Server-side biometrics and identity continuity
Server-side biometrics close this gap by comparing the in-app biometric capture to a verified enrollment template stored on the server. The process works in two stages:
- Onboarding: The user completes KYC verification (submitting ID documents and a selfie). The verified face becomes the enrollment template.
- Subsequent transactions: The app captures a live biometric sample, sends it encrypted to the server, and the server compares it to the KYC-enrolled template.
This ensures the person transacting now is provably the same person who passed identity verification, establishing identity continuity.
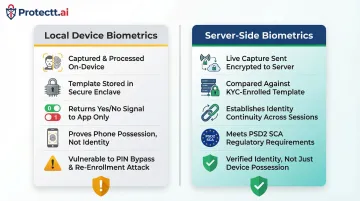
Regulatory compliance: Server-side biometrics meet Strong Customer Authentication (SCA) mandates under PSD2's Commission Implementing Regulation (EU) 2018/389, which requires authentication based on two or more elements and dynamic linking to transaction details.
Centralized vs. decentralized storage: a privacy and security trade-off
| Centralized Storage | Decentralized Storage | |
|---|---|---|
| How it works | All biometric templates held in a single server or database | Data fragmented or stored as cryptographic keys that never leave the device |
| Risk profile | Single breach exposes millions of records; biometrics can't be reissued like passwords | Server compromise yields no usable biometric data |
| Example | Traditional server-side template databases | FIDO2/WebAuthn passkeys (private key on device, public key server-side) |
Spain's ABANCA deployed FIDO2 passkeys in their mobile banking app, achieving 42% customer adoption and protecting over 11 million high-risk transactions without technical incidents.
Liveness detection: preventing spoofing attacks
Biometric authentication is only as strong as its anti-spoofing layer. Two detection approaches exist:
- Passive liveness: Analyzes the capture for signs of fakery (screen glare, pixelation) without user action
- Active liveness: Requires specific user actions (blink, turn head, smile) to confirm a live person is present
The rise of generative AI has raised the stakes significantly. FinCEN issued an alert in 2024 (FIN-2024-Alert004) regarding fraud schemes involving deepfake media targeting financial institutions. Europol's 2025 report confirms that systems can be tricked using masks, artificial fingerprints, or deepfakes.
ISO/IEC 30107-3 certification for Presentation Attack Detection (PAD) is becoming baseline for banking-grade biometrics. This standard establishes principles and methods for testing how well a biometric system detects presentation attacks, ensuring the sample is from a live, present human.
Going beyond OTP: advanced authentication techniques for secure banking
SMS OTP's ubiquity masks its catastrophic weaknesses. Global regulators are mandating phase-outs, forcing banks to adopt advanced authentication techniques that eliminate OTP vulnerabilities.
Why SMS OTP is a liability
SIM Swap Fraud: ENISA reports that attackers intercept OTP SMS using SS7 protocol vulnerabilities, making SIM swapping the easiest way to intercept SMS for banking fraud without requiring complex technical tools. The SMS infrastructure relies on older protocols with well-known security flaws that cannot be patched.
Regulatory Exodus: Regulators worldwide are setting hard deadlines to eliminate SMS OTPs:
- Philippines: Bangko Sentral ng Pilipinas mandated banks move away from SMS OTPs by June 30, 2026
- UAE: Central Bank directive requires financial institutions to eliminate SMS and email OTPs by March 2026
- Europe: The European Banking Authority stated in Q&A 2018_4414 that SMS does not protect confidentiality, authenticity, and integrity, and SS7 vulnerabilities allow interception
User Friction: 10-15% of SMS OTPs never reach users due to network issues. Users must wait for the message, switch apps, copy the code, and return—creating abandonment risk at critical conversion points.
Silent mobile verification and SIM binding
Silent authentication via carrier network verification eliminates OTPs entirely. The banking app initiates a silent check directly through the mobile network operator to confirm the SIM card and phone number match—no user action, no OTP to intercept.
The system performs a secure cryptographic handshake between the device's physical SIM card and the mobile network operator's core network. This verifies possession of the legitimate SIM in real time, completing authentication in 2-4 seconds without user intervention.
Device and SIM binding ties the authenticated session to a specific verified device-SIM combination. Even if credentials are stolen, account access from an unbound device is blocked—effectively preventing remote account takeover attacks.
Protectt.ai's Silent Mobile Verification uses proprietary LSAP technology and 3-Way Hairpin methodology to create a verified acknowledgement loop (Mobile → SMS Gateway → Server → Mobile) that validates the mobile number through the carrier network. The cryptographic process relies on a device-specific key stored within the physical SIM card — a credential attackers cannot replicate.
When fraudsters attempt SIM swap attacks, silent verification fails immediately: the fraudster's SIM lacks the legitimate user's cryptographic key.

Zero Trust Device & SIM Binding from Protectt.ai cryptographically ties user identity to a specific device-SIM combination, blocking account takeover from a different device even when passwords are compromised.
Device binding secures the access point — but a sophisticated attacker who compromises a legitimate device still needs another layer of scrutiny. That's where behavioral biometrics step in.
Behavioral biometrics and AI-driven anomaly detection
Behavioral biometrics enable continuous passive authentication throughout the session. The system monitors typing rhythm, touch pressure, swipe velocity, navigation patterns, and session duration to build a behavioral baseline per user.
AI/ML models analyze these patterns in real time and flag deviations. If a user's typing cadence suddenly changes, or navigation patterns become erratic, the system triggers step-up verification to confirm identity before allowing sensitive transactions.
Real-world effectiveness: A 2025 academic study utilizing LSTM deep learning networks for behavioral biometrics in digital banking achieved 97.9% accuracy, 95.6% precision, and 93.4% recall in fraud detection. BioCatch's case study at a top 5 U.S. bank showed that behavioral biometrics successfully identified fraudulent activity and deflected sustained account takeover attacks.
Protectt.ai's platform builds unique user profiles by monitoring:
- Typing patterns and touchscreen gestures
- Swipe velocity and app navigation timing
- Session duration and contextual behavior shifts
These behavioral signals combine with device risk assessment to generate real-time trust scores, triggering step-up authentication when anomalies are detected.
Zero trust architecture applied to mobile banking
Zero Trust operates on the principle "never trust, always verify." Every request, even from an already-authenticated session, is validated against contextual signals rather than assuming trust based on initial login.
NIST SP 800-207 defines Zero Trust as a paradigm where trust is never granted implicitly but must be continually evaluated. Authentication and authorization are discrete functions performed before each session, evaluating the observable state of client identity, application, and requesting asset.
Context-aware access control dynamically adjusts authentication requirements based on:
- Device health: Jailbroken/rooted status, OS version, security patch level
- Location: Geographic location, VPN/proxy detection, velocity checks (impossible travel)
- Network environment: Public Wi-Fi vs. cellular, man-in-the-middle risk indicators
- Transaction risk score: Amount, payee status, frequency, time of day
Protectt.ai's platform implements Zero Trust through continuous device integrity verification, runtime threat detection, and real-time behavioral analysis. These signals enforce adaptive authentication policies without requiring code changes — keeping security tight as threat landscapes shift.
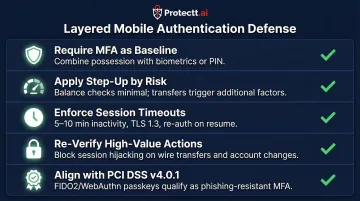
Best practices for deploying mobile authentication in banking apps
Implementing secure mobile authentication requires a layered defense strategy that balances security, user experience, and regulatory compliance.
Layered defense strategy
- Require MFA as baseline: Combine possession (device/SIM) with biometrics or a PIN so attackers need multiple compromises to succeed
- Apply step-up authentication by risk: Balance checks need minimal verification; large transfers or adding a payee trigger additional factors
- Enforce short session timeouts: 5–10 minutes of inactivity, TLS 1.3 for all traffic, and re-authentication after timeout or background resume
- Require re-verification for high-value actions: Even after a valid MFA login, wire transfers and account changes need an additional check to block session hijacking
- Align with compliance frameworks: PCI DSS v4.0.1 Requirement 8.4.2 mandates MFA for all non-console access to cardholder data environments; PCI SSC FAQ 1595 confirms FIDO2/WebAuthn passkeys qualify as phishing-resistant MFA
Operational requirements banks often overlook
These foundational layers work best when paired with operational measures that many teams deprioritize during deployment.
- Use hardware-backed credential storage: TEE (Trusted Execution Environment) or Secure Enclave isolates biometric and auth credentials from the main OS, keeping them inaccessible even on a compromised device
- Run SDK integrity checks at runtime: Deploy RASP controls to detect reverse engineering, code tampering, and hooking attempts before they execute. Protectt.ai's RASP SDK covers anti-tampering, hooking detection, and device binding as a single integrated layer
- Monitor continuously with real-time alerts: Track anomalous access patterns, device binding changes, and behavioral signals. Protectt.ai's security dashboard surfaces threat severity, configuration gaps, and historical trends so teams can act before damage occurs
The UX imperative: security without abandonment
Authentication security must not create abandonment. Research shows that 53% of consumers would switch financial institutions based on the strength and convenience of their authentication processes. Bain & Company found a 103-point Net Promoter Score spread between customers who successfully opened accounts digitally on the first attempt versus those who couldn't.
Friction-Right Design Principles:
- Invisible security layers for routine actions: behavioral biometrics, silent verification, device binding—all operate without user awareness
- Explicit verification only when risk warrants it: step-up authentication for high-value transactions, adaptive MFA based on contextual signals
- Eliminate unnecessary steps: silent mobile verification completes in 2-4 seconds with zero user action, replacing the multi-step SMS OTP flow
- Optimize onboarding: 68% of European consumers have abandoned digital financial processes due to technical barriers or lack of trust—streamline KYC and initial authentication to reduce drop-off
Protectt.ai's Silent Mobile Verification delivers zero-friction access by eliminating OTP wait times and manual code entry, directly improving conversion rates at critical touchpoints like sign-up and checkout while maintaining stronger security than SMS OTP.
Frequently asked questions
How does mobile authentication work?
Mobile authentication verifies a user's identity by checking one or more factors—something they know (PIN/password), something they have (device/SIM/OTP), or something they are (biometrics)—before granting access or approving a transaction. Multi-factor authentication combines two or more factors so attackers need multiple simultaneous compromises to succeed.
What should you avoid to ensure mobile banking security?
Key risks to eliminate include:
- Relying solely on SMS OTP (vulnerable to SIM swap and phishing)
- Using weak or reused PINs and skipping multi-factor authentication
- Allowing unverified devices to remain paired to accounts
- Neglecting session timeouts, app-level runtime protection, or centralized biometric storage without strong encryption
What are the 5 main types of biometric authentication?
The five primary types are fingerprint recognition, facial recognition, voice recognition, iris/retina scanning, and behavioral biometrics (typing cadence, swipe patterns, navigation behavior). Facial recognition leads adoption in mobile banking because it ties directly to KYC identity verification, maintaining identity continuity from onboarding through every transaction.
Is biometric authentication safer than OTP for mobile banking?
Server-side biometrics are more secure than SMS OTPs—they cannot be intercepted via SIM swap or phishing. Local device biometrics (FaceID, Android fingerprint) are not sufficient on their own; banking-grade security requires matching against an identity-verified template stored server-side to establish true identity continuity.
What is device binding in mobile banking?
Device binding cryptographically ties a user's authenticated identity to a specific device (and SIM card), so that even if credentials are stolen, account access from an unbound device is blocked. This effectively prevents remote account takeover by ensuring authentication sessions are locked to verified devices, blocking fraudsters from accessing accounts from any unregistered device.
What is step-up authentication in banking apps?
Step-up authentication dynamically requires stronger verification only when a higher-risk action is detected—such as a large transfer, changing account details, or adding new payees. Low-risk actions like checking a balance proceed with minimal friction, while high-value transactions trigger additional checks (biometric verification, OTP, security questions)—keeping friction proportional to actual risk.


