
Introduction
Mobile apps have become the primary interface for banking, payments, and financial services worldwide. Yet, mobile-specific security standards remain misunderstood or overlooked by many compliance teams. Developers and compliance officers know they need "OWASP compliance," but few understand what that means specifically for mobile applications—where the attack surface extends beyond the browser into device storage, OS permissions, and runtime environments.
According to Zimperium's 2025 Global Mobile Threat Report, 17.86% of financial work apps exhibit insecure communication practices, while 57.20% of iOS finance apps leak sensitive data. These are systemic failures to implement basic OWASP Mobile Application Security Verification Standard (MASVS) controls — leaving transaction records, session tokens, and user credentials directly exposed to attackers.
For banking, fintech, and insurance teams operating under regulators like RBI, PCI DSS, or the DPDP Act, closing that gap isn't optional. Understanding which OWASP frameworks apply to mobile — and what they actually require — is where compliance work has to start.
TLDR
- OWASP is a nonprofit that publishes vendor-neutral security standards, tools, and testing guides used by developers and compliance teams worldwide
- For mobile apps, the critical OWASP resources are MASVS and MASTG—not just the web-focused Top 10
- The OWASP Mobile Top 10 2024 identifies the most exploited vulnerability categories, from insecure data storage to insufficient binary protections
- PCI DSS v4.0.1, ISO 27001:2022, and RBI's Digital Payment Security Controls all reference OWASP standards directly
- Meeting OWASP mobile standards cuts breach risk, shortens audit cycles, and strengthens user trust
What is OWASP and how did it evolve?
The Open Worldwide Application Security Project (OWASP) Foundation was launched on December 1, 2001, as a United States nonprofit charity originally focused on web application security. The organization operates on a strictly vendor-neutral, free, and open-source model—all resources, including standards, tools, and documentation, are freely available to anyone.
In early 2023, OWASP officially changed its name from the "Open Web Application Security Project" to the "Open Worldwide Application Security Project" to reflect its expansion beyond web security into mobile, API, IoT, and AI security domains. For mobile security teams, this shift matters: it signals that OWASP now publishes dedicated, authoritative standards for mobile-specific threats — not just web app vulnerabilities adapted for mobile.
The OWASP Mobile Application Security (MAS) flagship project was established as a dedicated workstream, separate from the web-focused Top 10, and delivers three core resources:
- MASVS (Mobile Application Security Verification Standard) — defines what secure mobile apps must do
- MASTG (Mobile Application Security Testing Guide) — describes how to test MASVS requirements
- MASWE (Mobile App Security Weakness Enumeration) — catalogs mobile-specific security weaknesses
The OWASP API Security Top 10 rounds out this framework for mobile teams, since most mobile apps route core transactions and data through backend APIs — making API vulnerabilities a direct mobile risk, not just a server-side concern.
OWASP's mobile security framework: MASVS and MASTG
Understanding MASVS: the security standard
The OWASP Mobile Application Security Verification Standard (MASVS) is the primary security standard for mobile applications. MASVS v2.1.0, released in January 2024, defines security requirements across eight control domains:
- MASVS-STORAGE — Protects sensitive data intentionally stored by the app
- MASVS-CRYPTO — Manages cryptographic keys throughout their lifecycle
- MASVS-AUTH — Secures authentication and authorization protocols
- MASVS-NETWORK — Protects data exchanges with remote servers
- MASVS-PLATFORM — Secures interaction with the mobile OS and other installed apps
- MASVS-CODE — Enforces security best practices for data processing
- MASVS-RESILIENCE — Provides defense-in-depth against reverse engineering and tampering
- MASVS-PRIVACY — Establishes baseline privacy and data collection transparency

MASVS v1.x used L1 (baseline security for all apps) and L2 (defense-in-depth for sensitive data apps) verification levels. In v2.x, these evolved into MASTG security testing profiles (L1, L2, R, and P) to allow varied testing approaches while keeping MASVS controls abstract and platform-agnostic.
Understanding MASTG: the testing guide
The OWASP Mobile Application Security Testing Guide (MASTG) is the companion testing guide that describes how to verify MASVS requirements. MASTG covers both iOS and Android, provides test cases for static and dynamic analysis, and guides penetration testers and security teams on what to check and how.
As of MASTG v1.6.0 and MASVS v2.1.0, checklists are completely automated and available in CycloneDX format—enabling easier integration into DevOps pipelines to track and comply with MASVS requirements through Software Bill of Materials (SBOM) generation.
Why these categories matter for financial apps
Each MASVS category addresses mobile-specific risks that don't exist in web applications. Three categories carry particularly high stakes for financial and enterprise apps:
- Insecure local data storage exposes transaction records, session tokens, or PII when attackers gain physical access to lost or stolen devices.
- Weak cryptography often stems from hardcoded encryption keys embedded in app binaries. Nearly one in five mobile apps contain hardcoded encryption keys, according to NowSecure's analysis of 525,600 assessments.
- Platform interaction vulnerabilities include insecure inter-process communication, tapjacking, and device-binding failures — threats with no web equivalent. Mobile apps run on what OWASP calls an "untrusted execution environment": the user's device, outside the organization's control.
Because the device itself is the threat surface, web-centric security frameworks leave critical gaps. That's precisely what MASVS and MASTG are designed to fill.
The difference from web-focused OWASP Top 10
MASVS and MASTG are purpose-built for mobile attack surfaces. The web-focused OWASP Top 10 doesn't address mobile-specific risks such as:
- Insecure inter-process communication
- Tapjacking and overlay attacks
- Device-binding failures
- Rooted/jailbroken device exploitation
- Binary reverse engineering and code tampering
MASVS is continuously updated to reflect evolving mobile threat patterns, so organizations need to track versions to maintain genuine compliance rather than point-in-time checklist coverage. The v1 to v2 shift is a practical example: security controls moved from level-based pass/fail to abstract, platform-agnostic requirements tested through MASTG profiles — a change that directly affects how teams scope assessments and structure audit evidence.
The OWASP Mobile Top 10: key vulnerabilities explained
The OWASP Mobile Top 10 2024 Final Release is the currently active version, superseding the 2016 list. Unlike the Web Top 10, it accounts for the mobile-specific attack surface: local device storage, mobile OS permissions, hardware-level identifiers, and app-to-app communication channels.
Each of the 10 categories maps to a distinct class of risk. The first five address credential, supply chain, authentication, input handling, and communication failures — the most commonly exploited vectors in enterprise mobile apps.
Critical vulnerability categories
M1: Improper Credential Usage covers hardcoded credentials within source code, insecure transmission and storage of credentials, and weak authentication methods. Zimperium found that 18% of Android finance apps use vulnerable encryption algorithms, directly risking credential exposure.
M2: Inadequate Supply Chain Security targets vulnerabilities in the mobile app supply chain, including development tooling used to inject malicious code. NowSecure discovered that 15% of mobile apps contain third-party SDKs with known vulnerabilities.
M3: Insecure Authentication/Authorization encompasses the authentication and authorization mechanisms used by mobile apps. This category ranks among the top 5 MASVS control violations across all assessed apps.
M4: Insufficient Input/Output Validation relates to validating app input and output. Inadequate validation leads to data corruption and allows attackers to bypass local security checks and manipulate financial transactions.
M5: Insecure Communication addresses controls that protect data exchanges with remote servers. 17.86% of financial work apps exhibit insecure communication practices, making them vulnerable to man-in-the-middle attacks.
Device and binary-level risks
The remaining five categories target the device layer — where mobile diverges most sharply from web security. These risks exploit the physical accessibility of app binaries, on-device storage, and OS-level configurations.
M6: Inadequate Privacy Controls — failure to protect users' personal data and ensure responsible data handling
M7: Insufficient Binary Protections — absence of binary protections that leaves apps open to analysis, reverse engineering, and modification. Nearly 75% of tested apps left debug symbols in their code, giving attackers a direct path to decompile and extract sensitive logic.
M8: Security Misconfiguration — improper configuration of security settings, permissions, and controls that create exploitable vulnerabilities
M9: Insecure Data Storage — leaves sensitive or regulated data open to attackers with physical or remote access to the device
M10: Insufficient Cryptography — enables threat agents to decrypt sensitive data, manipulate cryptographic processes, or leak encryption keys
Reverse engineering and code tampering have no direct equivalent in the web Top 10 — and that gap matters. App binaries are publicly downloadable from app stores, which means an attacker can decompile your binary, extract hardcoded API keys, and modify authentication logic without ever touching your server. Binary protection (M7) and cryptography controls (M10) are the primary defenses against this attack class.

Why OWASP compliance matters for mobile apps in banking and FinTech
Direct regulatory references to OWASP
PCI DSS v4.0.1 treats native mobile apps that render payment fields or transmit card data as in-scope payment applications. Requirement 6.2.4 mandates that software engineering techniques prevent or mitigate common software attacks, while Requirement 11.4.1 requires penetration testing based on "industry-accepted penetration testing approaches," explicitly citing OWASP as an accepted standard.
ISO/IEC 27001:2022 Annex A.8 focuses on Technological Controls highly relevant to mobile app security:
- A.8.24 (Use of Cryptography) — maps to MASVS-CRYPTO
- A.8.25 (Secure Development Life Cycle) — embeds security within mobile app development
- A.8.26 (Application Security Requirements) — defines security requirements during app design
- A.8.28 (Secure Coding) — enforces practices that prevent Mobile Top 10 vulnerabilities
- A.8.29 (Security Testing in Development and Acceptance) — requires automated VA/PT and MASTG testing before production release
The Reserve Bank of India's Master Direction on Digital Payment Security Controls (2021) goes furthest. Paragraph 31 explicitly states that Regulated Entities (REs) shall refer to "OWASP-MASVS, OWASP-ASVS and other relevant OWASP standards" and that testing must verify vulnerabilities including the "OWASP Mobile Top 10."
The compliance risk of ignoring OWASP mobile standards
These mandates exist for good reason. Verizon's 2025 Data Breach Investigations Report recorded 3,336 incidents in the Financial and Insurance sector, with System Intrusion and Social Engineering representing 74% of breaches. Financial motivations drive 90% of these attacks.
Mobile app vulnerabilities directly contribute to those losses. Failed audits can trigger mandatory app takedowns, while publicly disclosed breaches cause lasting reputational damage. Organizations that treat MASVS L1 as "done" miss the point: for financial apps handling transactions, PII, or authentication, MASVS L2 or the Resilience extension is typically required to meet the spirit—not just the letter—of regulatory mandates.
How Protectt.ai supports OWASP compliance
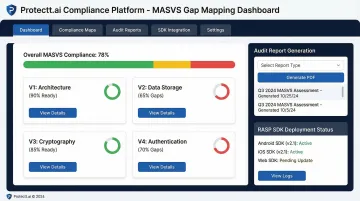
Protectt.ai's platform, certified under PCI DSS and ISO 27001, helps organizations map their mobile app security posture against OWASP MASVS requirements. Three capabilities drive the compliance workflow:
- MASVS gap mapping — automated assessment of iOS and Android apps against L1, L2, and Resilience controls
- Audit report generation — reduces manual compliance preparation time by up to 90%, turning weeks of work into automated output
- RASP SDK deployment — addresses MASVS-RESILIENCE controls with 100+ security features integrated into mobile apps with zero performance overhead
How to align your mobile app with OWASP standards
Start with a MASVS-based gap assessment
Identify where your current app falls short of L1 or L2 requirements. Map identified gaps to MSTG test cases to build a prioritized remediation roadmap. This assessment should cover all eight MASVS control domains and determine which testing profile (L1, L2, R, or P) fits your app's risk profile.
Integrate OWASP-aligned security testing into CI/CD
Shift security testing left by integrating MASTG tests directly into your CI/CD pipeline. This ensures vulnerabilities are caught before each release rather than discovered during audits.
The numbers make the case: a Forrester Total Economic Impact study on DevSecOps found:
- 483% ROI from integrated security workflows
- 305 hours reclaimed annually by development teams
- Incident response time cut from up to 30 days to just 1 hour
Implement runtime protection for MASVS-RESILIENCE
OWASP MASVS-RESILIENCE controls, which address tampering, reverse engineering, and jailbreak/root detection, require runtime defenses—not just secure code. This is where Runtime Application Self-Protection (RASP) becomes essential. NIST Special Publication 800-53 Revision 5 officially recognizes RASP under control SI-7(17), noting that RASP employs runtime instrumentation to block exploitation and protect the runtime environment from tampering.
Protectt.ai's RASP SDK covers these resilience controls with 100+ security features that can be integrated into iOS and Android apps, including:
- Jailbreak/root detection
- Hooking prevention
- App spoofing detection
- Reverse engineering protection
- Code tampering detection
- Debugging prevention
- Screen mirroring detection

Make OWASP compliance an ongoing process
Threat patterns evolve, MASVS versions update, and new mobile OS releases can invalidate previous security assumptions. Establish continuous monitoring and re-testing schedules tied to your app release cycles. Teams that tie OWASP re-assessments to each release are far better positioned to catch regressions before they become incidents.
Frequently asked questions
What is OWASP used for?
OWASP is used by developers, security teams, and compliance professionals to access free, vendor-neutral security standards, tools, and testing guides for web, mobile, and API security. Organizations rely on OWASP frameworks to establish security baselines and demonstrate compliance with regulatory requirements.
What are OWASP 10 vulnerabilities?
The "OWASP Top 10" traditionally refers to the top web application security risks such as Broken Access Control, Injection, and Cryptographic Failures. However, there is also a separate OWASP Mobile Top 10 that covers mobile-specific threats like insecure data storage, code tampering, and reverse engineering.
What is the OWASP Mobile Application Security Verification Standard (MASVS)?
MASVS is OWASP's dedicated security standard for mobile apps, covering requirements across authentication, cryptography, and network security. It defines two primary levels — L1 for baseline security and L2 for high-risk apps — plus Resilience and Privacy extensions.
Is OWASP compliance mandatory for mobile apps?
OWASP itself does not mandate compliance, but frameworks like PCI DSS v4.0.1 and ISO 27001:2022 — both legally or contractually required for financial apps — reference OWASP standards directly. The RBI explicitly mandates OWASP MASVS testing for digital payment apps, making alignment effectively mandatory for banking and fintech apps in India.
How does OWASP relate to PCI DSS compliance for mobile banking apps?
PCI DSS v4.0.1 includes application security requirements for apps handling cardholder data that align directly with OWASP MASVS controls. Demonstrating MASVS compliance supports PCI DSS audit evidence for mobile payment apps, particularly for Requirements 6.2.4 and 11.4.1.
What is the difference between the OWASP Web Top 10 and the OWASP Mobile Top 10?
The Web Top 10 covers browser-facing vulnerabilities like SQL injection and XSS. The Mobile Top 10 addresses risks unique to app binaries, device storage, OS permissions, and runtime threats like tampering and reverse engineering — none of which exist in web applications.


