
Introduction
Mobile banking apps, fintech platforms, and insurance applications carry an uncomfortable truth: the moment you distribute them to users, your proprietary code lives in an environment you don't control. These apps contain sensitive business logic, API credentials, and authentication flows—all embedded in binaries sitting on millions of devices, accessible to anyone who downloads them. The exposure is not theoretical — it is the default state of every distributed mobile app.
Compiled mobile apps can be decompiled with freely available tools in minutes. An Android APK is just a ZIP archive — unpack it, run it through JADX, and you're reading Java or Kotlin source code. iOS binaries, despite compiling to machine code, retain extensive Objective-C and Swift metadata that makes them far more readable than most developers expect.
The attack surface is wide open by design.
Code obfuscation addresses this exposure directly, transforming readable source code into a functionally identical but deliberately incomprehensible form that resists reverse engineering and protects the intellectual property embedded in your mobile applications. This article breaks down how obfuscation works, what it protects against, and where it fits within a broader mobile security strategy.
TL;DR
- Code obfuscation transforms readable source into functionally identical but incomprehensible code to resist reverse engineering
- Protects intellectual property, API keys, authentication logic, and business algorithms in mobile apps
- Core techniques: identifier renaming, string encryption, control flow flattening, dead code insertion
- Operates at source, intermediate (LLVM), or binary level — binary-level protection is the strongest and toolchain-independent
- Must be combined with RASP and threat monitoring for complete mobile app security
What is code obfuscation?
Code obfuscation is the deliberate transformation of source code or compiled binary into a form that preserves full functional behavior while making the code's logic, structure, and intent extremely difficult for humans or automated tools to interpret. OWASP defines it as "the process of transforming code and data to make it more difficult to comprehend (and sometimes even difficult to disassemble)."
What obfuscation is NOT
Three common misconceptions are worth clearing up:
- Not encryption — the app runs normally without any decryption key; obfuscation restructures code to be unintelligible while remaining fully executable
- Not minification — minification shortens variable names to reduce file size; obfuscation conceals logic and meaning to prevent reverse engineering
- Not a vulnerability fix — obfuscation doesn't patch security flaws; it raises the cost, time, and complexity required for attackers to exploit your app
Why obfuscation exists for mobile
Unlike server-side code protected behind firewalls, mobile app binaries are distributed directly to millions of devices. Your code is accessible to anyone who downloads your app. An attacker doesn't need to breach your infrastructure. Downloading your app from the App Store or Google Play is enough.
For banking and fintech apps, this exposure is particularly dangerous. The binary contains proprietary systems that competitors and attackers can directly examine without obfuscation:
- Transaction processing logic
- Fraud detection algorithms
- Identity verification flows
How code obfuscation works
Obfuscation is a transformation pipeline applied to code before distribution. It operates at one of three levels, each with distinct tradeoffs:
Three Obfuscation Levels:
- Source Level: Applied to human-readable code before compilation; easiest to implement but least robust
- Intermediate Level (LLVM): Applied to compiler intermediate representation; language-independent and aligns with iOS submission practices
- Binary Level: Applied to compiled machine code; most robust and toolchain-agnostic, working directly on the final executable

Binary-level obfuscation offers the strongest protection because it's independent of your development toolchain and operates on the actual code that executes on devices.
Key obfuscation techniques
Identifier renaming and namespace flattening
Class names, method names, and variables are replaced with meaningless symbols or random strings, destroying semantic meaning. A function like getUserAccountBalance() becomes _0x4f2a(). This matters most for Java, Kotlin, Swift, and Objective-C apps, where readable identifiers help attackers navigate decompiled code.
String encryption
Sensitive string literals — API endpoints, keys, tokens, error messages — are encrypted at rest in the binary and only decrypted at runtime. This prevents static analysis tools from extracting secrets by scanning the binary.
For example, an API endpoint like https://api.bank.com/v2/accounts becomes an encrypted byte array that only resolves when the code executes.
Control flow obfuscation
The logical execution path is restructured using techniques like control flow flattening, opaque predicates, and dead code insertion. This turns readable, hierarchical logic into a flat or circuitous maze. Instead of clear if-then-else statements, the code becomes an infinite loop with a switch statement controlling flow. Both static and dynamic analysis tools struggle to follow it.
Data obfuscation and metadata stripping
Sensitive data structures are obscured and unnecessary debug metadata — class hierarchies, symbol tables, function signatures — is stripped from the binary. This removes the map that reverse engineers rely on to navigate compiled code.
What the output looks like
The obfuscated binary retains 100% of its functionality. The CPU executes it correctly, but any decompiled output looks like meaningless, unnavigable code.
Before obfuscation:
public double calculateInterestRate(double principal, int term) {
double baseRate = 0.045;
return principal * baseRate * term;
}
After obfuscation:
public double _0x4f2a(double _0x3c1b, int _0x7e9f) {
double _0x2d4a = [encrypted_value];
return _0x3c1b * _0x2d4a * _0x7e9f;
}
Why code obfuscation is critical for mobile apps
The reverse engineering threat
Android APKs can be decompiled in under 5 minutes using freely available tools. One widely cited demonstration showed that extracting API keys, endpoint URLs, and class names from a production Flutter APK took less than five minutes using basic terminal commands—just unzip the APK and run a decompiler.
iOS apps present a similar problem. Despite being compiled to machine code, Objective-C and Swift metadata makes them far more readable than developers assume. The binary contains class names, method signatures, and structural information that guides reverse engineers through the code.
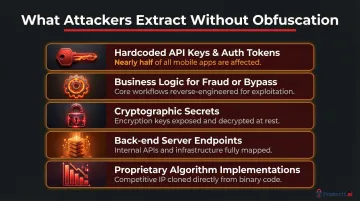
What attackers extract
Without obfuscation, attackers easily extract:
- Hardcoded API keys and authentication tokens — Nearly half of mobile apps contain hardcoded secrets, with 1 in 3 Android apps leaking sensitive data
- Business logic for fraud or bypass — Transaction processing rules, fraud detection algorithms, credit scoring logic
- Cryptographic secrets — Encryption keys, signing certificates, hash salts
- Back-end server endpoints — API URLs, internal service addresses, testing environments
- Proprietary algorithm implementations — Recommendation engines, risk models, pricing calculators
For financial apps, this exposure has direct consequences — not theoretical ones. These CVEs illustrate what happens when mobile binaries ship without protection:
- CVE-2024-23453: Android Spoon app contained hardcoded credentials allowing local attackers to retrieve API keys via reverse engineering
- CVE-2023-23132: Selfwealth iOS mobile app revealed hardcoded API keys in the decompiled binary
- CVE-2025-20615: Qardio Arm iOS app exposed usernames and passwords in a plist file, providing access to an engineering backdoor
Compliance and security standards
OWASP MASVS v2 Requirements:
OWASP Mobile Application Security Verification Standard (MASVS) explicitly requires anti-static analysis mechanisms under MASVS-RESILIENCE-3: "The app implements anti-static analysis mechanisms." This control aims to impede comprehension by making static analysis difficult.
PCI DSS Mandates:
PCI DSS v4.0 Requirement 8.6.2 states: "Passwords/passphrases for any application and system accounts that can be used for interactive login are not hard coded in scripts, configuration/property files, or bespoke and custom source code."
Meeting these standards is the floor, not the ceiling. The business consequences of failing to obfuscate extend well beyond a compliance audit.
Business impact of not obfuscating
- Competitor cloning — Competitors reverse-engineer and replicate proprietary features, eroding the competitive advantage built into your product
- App repackaging — Attackers modify legitimate apps to include malicious payloads, then distribute fake versions that look identical to the original; users unknowingly install compromised apps
- Direct financial fraud — Exposed transaction logic enables attackers to manipulate payment flows, bypass fraud detection, or exploit authentication vulnerabilities
Android malware-driven financial transactions increased 67% year-over-year, with mobile banking apps becoming the primary battleground for financial fraud.
Limitations of code obfuscation
Obfuscation is not impenetrable
A sufficiently skilled and resourced attacker with enough time can de-obfuscate code using tools like Frida for dynamic instrumentation, symbolic execution (automated analysis that maps all possible code paths), and AI-assisted code analysis. Obfuscation raises the cost and time of attack significantly but does not eliminate the risk permanently.
Frida, for example, injects JavaScript into a running process to alter app behavior in real-time — including bypassing SSL/TLS certificate pinning by hooking network libraries to accept any certificate, opening the door to Man-in-the-Middle traffic interception.
AI-assisted deobfuscation
Recent research on Large Language Models shows that state-of-the-art LLMs can autonomously deobfuscate low-resistance techniques like bogus control flow. However, models currently fail against high-resistance combined techniques such as control flow flattening plus instruction substitution. As LLM capabilities advance, relying on a single obfuscation technique becomes a progressively weaker defense — which is why combining multiple high-resistance techniques is now standard practice.
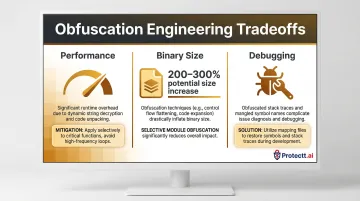
Practical tradeoffs
Stronger obfuscation comes with real engineering tradeoffs:
- Performance: Aggressive string decryption at runtime introduces measurable overhead. Modern tools mitigate this through selective application and debug-build exclusions, but the balance between protection strength and app performance needs deliberate tuning.
- Binary size: Heavy obfuscation can increase binary size by 200–300%. Selective obfuscation — applied only to sensitive modules — significantly reduces this impact.
- Debugging: Obfuscated stack traces complicate crash reporting. Well-implemented tools provide mapping files to translate obfuscated traces back to readable code, though this adds a step to development workflows.
The critical limitation: runtime exposure
These tradeoffs are manageable. The harder limitation isn't developer friction — it's what happens after launch. Obfuscation protects the code at rest — the static binary — but provides no protection once the app is running. At runtime, a hooking framework can intercept decrypted values and live function calls regardless of how well the binary was obfuscated. This is what necessitates runtime protection.
Beyond obfuscation: building a complete mobile app security strategy
The layered security model
Obfuscation handles static binary protection, but a complete strategy requires Runtime Application Self-Protection (RASP) that can detect and respond to threats while the app is executing.
RASP Capabilities Include:
- Detecting debuggers and hooking frameworks like Frida
- Identifying rooted or jailbroken devices
- Detecting emulators and virtualized environments
- Monitoring for SSL/TLS certificate pinning bypass attempts
- Identifying screen mirroring and overlay attacks

Full-stack mobile security platform
A comprehensive mobile security platform should cover every layer of the attack surface:
- Anti-tampering detection — verifies the app binary hasn't been modified or repackaged after distribution
- Device integrity verification — flags rooted, jailbroken, or otherwise compromised devices before they become attack vectors
- Real-time threat monitoring — tracks anomalous API calls and suspicious behavior patterns as they happen
- AI-driven behavioral analysis — catches unusual usage patterns that signal fraud, account takeover, or automated attacks
Protectt.ai's AI-native, full-stack mobile app security platform
Protectt.ai combines advanced code obfuscation with RASP (100+ security features), device binding, and continuous threat intelligence in a single integrated platform. Built for high-stakes environments — banking, insurance, and fintech — it covers both static and runtime protection, from binary distribution through active execution.
Customers like RBL Bank, Bajaj Finserv, and BSE rely on this layered approach because no single control is sufficient on its own. When obfuscation, RASP, and behavioral analysis operate together, attackers face compounding barriers at every stage of an attempted compromise.
Frequently asked questions
What is an example of obfuscation?
A readable function like getUserAccountBalance() becomes _0x4f2a() after renaming obfuscation. A plaintext API endpoint string becomes an encrypted byte array that only resolves at runtime. The code still works identically, but the logic and intent are completely obscured.
Why do people obfuscate their code?
Developers obfuscate code for three primary reasons:
- Protect intellectual property and proprietary business logic from competitors
- Prevent attackers from reverse engineering the app to find vulnerabilities or extract secrets
- Block malicious cloning and tampered repackaged versions of the app
Can AI read obfuscated code?
AI tools and LLMs can partially de-obfuscate code, with success depending heavily on obfuscation strength. Multi-layered binary-level obfuscation with control flow flattening remains resistant even to AI analysis—but as this threat evolves, pairing obfuscation with runtime protection is increasingly important.
Is code obfuscation enough to protect a mobile app on its own?
No. Obfuscation alone is not sufficient—it protects the static binary but provides no defense at runtime, where hooking tools can intercept live execution. A complete strategy pairs obfuscation with RASP, anti-tampering, and device integrity checks.
Does code obfuscation slow down app performance?
Obfuscation has minimal performance impact when applied correctly. String decryption at runtime adds negligible overhead, and modern tools apply transformations selectively. The main concern is aggressive dead code insertion, which can increase binary size.
What is the difference between code obfuscation and encryption?
Encryption locks data behind a key and requires decryption to use it. Obfuscation restructures code to be hard to understand while remaining fully executable—it doesn't require a "key" to run, it simply makes the code's logic unreadable to static analysis tools and reverse engineers.


