
Introduction
Mobile banking apps now handle billions of transactions daily, processing authentication, session tokens, transaction authorization, and sensitive financial data across global markets. That volume has made them the most targeted category of financial software—and the attacks have followed accordingly. According to Zimperium's 2025 research, 34 active malware families targeted 1,243 financial institutions across 90 countries, with Android malware-driven financial fraud increasing 67% year-over-year.
Perimeter defenses — firewalls, network monitoring, server-side controls — don't follow an attacker into the runtime environment. Once inside the app, traditional security tools have no visibility into how requests are actually processed, leaving a blind spot that static controls cannot close.
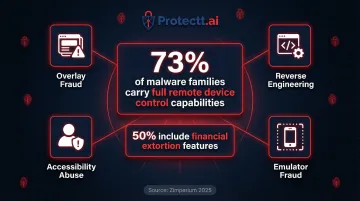
Modern attackers exploit exactly that gap. Techniques like overlay fraud, accessibility service abuse, and on-device transaction manipulation all operate after authentication succeeds, where conventional defenses stop watching.
Runtime Application Self-Protection (RASP) addresses this directly — embedding security logic inside the app itself, where it can detect and respond to threats as they happen. This guide breaks down how RASP works, why it matters for mobile banking specifically, and what to look for when evaluating runtime protection.
TL;DR
- RASP (Runtime Application Self-Protection) embeds directly inside a mobile app and detects attacks while the application is actively running
- Its inside-out visibility gives RASP access to actual runtime behavior — something firewalls and WAFs never see
- Mobile banking apps face overlay attacks, reverse engineering, rooting/jailbreaking, and API manipulation that firewalls and WAFs miss entirely
- RASP intercepts system calls and app logic in real time, blocking credential theft and transaction fraud at the point of execution
- Properly implemented RASP delivers this protection with no measurable performance impact on the end user experience
What is RASP?
Runtime Application Self-Protection (RASP) is a security technology built into or linked to an application's runtime environment. It enables the app to detect, intercept, and block attacks as they execute, without requiring changes to the underlying source code.
This closes a critical blind spot. Traditional security tools — firewalls, WAFs, and intrusion prevention systems — operate outside the application and cannot observe how requests are actually processed once inside the app.
What RASP is NOT:
- Not a mobile device management (MDM) tool
- Not an antivirus scanner
- Not a network firewall
- Not a traffic filter — it monitors and governs the app's own execution behavior, not the device or network
For mobile, RASP comes in two deployment forms:
- Agent-based: Embedded as a library or SDK directly within the app binary at build time
- In-app instrumentation: Hooks into the app's runtime to intercept function calls as they happen
Mobile RASP typically uses SDK-based integration for iOS and Android, embedded at build time so protection travels with the app to every device.
Why mobile banking apps are prime attack targets
Mobile banking apps sit at the intersection of personal identity and financial access—processing session tokens, transaction authorizations, and sensitive account data in a single attack surface. That makes them far more valuable to attackers than generic apps. The United States alone has 162 banking applications under active targeting, the highest concentration globally.
Mobile-specific threat categories that make banking apps especially vulnerable:
- Decompiling APK/IPA files to extract business logic, hardcoded API keys, or cryptographic secrets
- Displaying fake UI overlays (malware like Anatsa does this) to capture credentials or silently authorize fraudulent transactions
- Exploiting Android Accessibility APIs to read screen content, intercept OTPs, and execute automated gestures without user awareness
- Simulating legitimate user sessions via emulators to bypass device fingerprinting and behavioral analytics
What makes these attacks harder to stop than web threats is the device itself. Banks don't control the phones their customers use — rooted handsets, compromised OS environments, sideloaded malware, and manipulated network connections all break traditional security assumptions before a single line of app code runs. Zimperium found that 73% of analyzed malware families carry full remote device control capabilities. Half include financial extortion features.
How RASP works inside a mobile banking app
Mobile RASP embeds its security logic directly into the app binary at build time, executing within the same process as the app itself. This gives it real-time visibility into every function call, data access, and behavioral signal — forming a continuous protection loop that travels with the app to every device.
Initiation and embedding
RASP is integrated as a lightweight SDK at build time with no server-side agent required for mobile. Protection travels with the app to every device and does not depend on network connectivity or external policy servers to function.
Monitoring starts the moment the app launches — not only when suspicious events are detected — which allows RASP to establish a behavioral baseline and catch deviations immediately.
Core runtime monitoring
During execution, RASP monitors:
- System calls and API interactions
- Memory access patterns
- Debugger attachment attempts
- Hooking frameworks (such as Frida or Xposed)
- Screen capture attempts
- Keyboard overlay activity
This is behavioral interception, not signature matching. RASP uses the app's own execution context to evaluate whether a behavior is legitimate.
A screen capture call from the app's own code during a supported export feature is treated differently from an external process triggering the same call mid-session. That contextual distinction is what keeps false positives low without dulling its sensitivity to real abuse.
Protectt.ai's SDK-based implementation — trusted by RBL Bank, Yes Bank, and Bajaj Finserv — embeds 100+ security checks spanning device integrity, runtime tampering, and transaction-level anomalies, with minimal measurable overhead on the end user's device.
Detection and response
When a threat is detected, RASP can respond in several ways:
- Terminate the session immediately
- Block the specific action without crashing the app
- Send real-time alerts to the security backend
- Log attack telemetry for forensic analysis
- Gracefully degrade app functionality

Because RASP acts within the same execution thread as the attack, it can intervene in milliseconds—before credentials are exfiltrated, before a fraudulent transaction is authorized, or before a reverse-engineering tool maps the app's sensitive logic.
RASP vs. traditional mobile security tools
RASP vs. WAF (Web Application Firewall)
A WAF analyzes incoming HTTP/HTTPS traffic at the server boundary and cannot see what happens inside the mobile app itself. It is blind to on-device tampering, memory manipulation, or local overlay attacks. RASP operates inside the execution environment, catching what WAF never sees.
RASP vs. MDM (Mobile Device Management)
MDM governs device-level policies — screen lock, remote wipe, app whitelisting — but has no visibility into runtime behavior within a specific app. RASP operates at the individual app level and works even on unmanaged or BYOD devices that fall outside MDM enrollment.
How these three layers work together
RASP, WAF, and MDM complement each other — they don't compete. Each defends a distinct layer:
| Tool | Scope | What It Protects |
|---|---|---|
| WAF | Server boundary | Filters malicious HTTP/HTTPS traffic before it reaches your backend |
| MDM | Device level | Enforces corporate policies across enrolled devices |
| RASP | App runtime | Detects and blocks in-app threats like memory manipulation and overlay attacks |
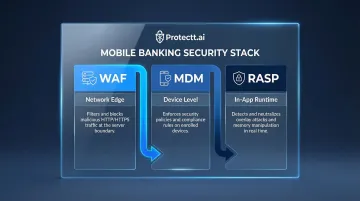
Together, this stack blocks threats at every stage — from the network edge to the device to the app itself — giving mobile banking a genuine defense-in-depth posture.
Key benefits of RASP for mobile banking security
Real-time threat neutralization
RASP detects and stops in-app attacks — hooking, overlay fraud, API manipulation — at the moment they occur, before they result in account takeover or financial loss.
The threat is real: Anatsa malware infected an estimated 90,000 users via a fake PDF app on Google Play, displaying "Scheduled Maintenance" screens to block users from contacting support while fraudulent transactions ran in the background.
Low false-positive rate
RASP evaluates behavior within full application context — not just traffic patterns or signatures. This means it distinguishes genuine malicious activity from normal app functionality, which delivers two concrete operational benefits:
- Reduces alert fatigue for security operations teams
- Avoids unnecessary session interruptions for legitimate users
Zero-day and unknown threat coverage
Because RASP detects behavioral anomalies rather than known signatures, it can identify and block novel attack techniques — including zero-day exploits and custom malware — not yet catalogued in threat intelligence databases.
USENIX Security 2024 research uncovered zero-day dynamically loaded transaction abuse routines in Cerberus malware that signature-based tools missed. Behavioral detection is what makes that catch possible.
Compliance support
Regulators increasingly require runtime application protection as part of a layered security mandate — including PCI DSS guidelines for payment apps and financial sector cybersecurity frameworks.
NIST SP 800-53 explicitly includes RASP as control SI-7(17), stating it "can reduce the susceptibility of software to attacks by monitoring its inputs and blocking those inputs that could allow attacks."
Institutions deploying full-stack RASP gain more than runtime protection: behavioral analytics and threat intelligence generated during monitoring feed directly into fraud prevention workflows, tightening security posture over time. Protectt.ai's platform is built around this closed-loop model, combining RASP with AI-driven threat intelligence and user behavior analytics.
Frequently asked questions
How is RASP different from a mobile antivirus or MDM solution?
Antivirus scans for known malware signatures on files, MDM enforces device-level policies, while RASP monitors and governs the behavior of a specific app during execution. They operate at different layers and are ideally used together for comprehensive protection.
Does RASP slow down a mobile banking app for end users?
Well-implemented RASP SDKs are designed for zero performance overhead. They run lightweight in-process checks that are imperceptible to users. Poorly optimized RASP implementations can introduce latency if not properly tested before deployment.
Can RASP detect rooted or jailbroken devices?
Yes. Device integrity detection (identifying rooted Android or jailbroken iOS environments) is one of the standard checks built into mobile RASP. The app can detect compromised OS environments and respond by blocking access or alerting the security team.
What threats can RASP alone not defend against in mobile banking?
RASP focuses on runtime and in-app threats; it does not replace server-side controls, secure coding practices during development, or network-layer defenses. Social engineering attacks targeting users are also outside RASP's scope.
Is RASP required for PCI DSS or banking regulatory compliance?
RASP directly supports compliance with PCI DSS and banking regulations by delivering the runtime protection, application-layer monitoring, and real-time threat detection those frameworks require. It isn't always named by term, but what it does maps precisely to the technical controls regulators expect.
How is RASP deployed in a mobile banking app — does it require code changes?
Mobile RASP is typically delivered as an SDK integrated at build time, requiring minimal code changes. It instruments the app binary before release, meaning the protection layer is baked in without rearchitecting the app.


