
Introduction
Financial institutions face mounting pressure from cyberattacks targeting mobile banking platforms. According to IBM's Cost of a Data Breach 2024 report, financial sector breaches now average $6.08 million—22% above the global average—with breach identification taking an average of 168 days. The fallout extends well beyond the breach itself:
- Regulatory penalties under frameworks like GDPR and PCI DSS
- Customer churn driven by eroded trust
- Reputational damage that takes years to repair
- Direct liability from fraud reimbursements
These costs make mobile finance apps a high-priority target. They combine high-value financial data with always-on connectivity and user convenience expectations — an attack surface that demands both disciplined development and continuous runtime defense.
Attackers exploit this aggressively. Zimperium's 2026 Banking Heist Report found 34 active malware families targeting 1,243 financial apps globally, with Android malware-driven financial transactions increasing 67% year-over-year.
The stakes extend beyond technology. Every vulnerability represents potential regulatory exposure, customer abandonment, and revenue loss. Protecting mobile finance apps requires embedding security from the design phase through post-launch operations, layering defenses across code, device, network, and runtime environments.
TL;DR
- Mobile finance apps concentrate credentials, PII, and transaction data in one place—attackers exploit weak code, authentication gaps, and network vulnerabilities
- Security belongs at the design stage: remediating production vulnerabilities costs up to 100x more than catching them during planning
- MFA with biometrics, TLS 1.3+ encryption, and OWASP-aligned coding form the baseline — not optional extras
- Runtime protection through RASP, device integrity checks, and behavioral monitoring defends against threats that evade development-phase controls
- Avoid critical mistakes: SMS OTP reliance, unvetted third-party libraries, and one-time-only security posture
Why mobile finance apps are prime targets for cyberattacks
Mobile finance apps hold everything attackers want: login credentials, account numbers, transaction history, and personally identifiable information—all accessible 24/7 from devices users carry everywhere. This concentration of high-value data in a portable, network-connected environment makes financial apps a higher-value target than virtually any other app category.
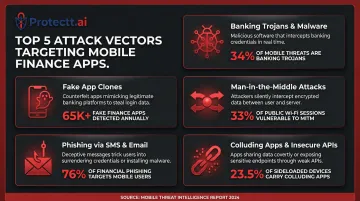
Primary threat categories targeting finance apps:
- Banking trojans and malware — Kaspersky detected 255,090 new mobile banking Trojan installation packages in 2025, representing a 271% increase over 2024; dominant families including TsarBot, CopyBara, and Hook now target over 60% of global banking apps
- Fake and counterfeit app clones — Sideloaded apps appear on 23.5% of enterprise devices, bypassing official app store security checks and frequently containing malicious code
- Man-in-the-Middle (MITM) attacks — 33% of network threats are MITM attacks, with malicious activity detectable within 10 minutes of connecting to unsecured networks
- Phishing via SMS and email — Social engineering attacks targeting device binding and authentication credentials
- Colluding apps and insecure APIs — Applications that silently share data across compromised API endpoints
Each of these attack vectors carries a direct regulatory cost. When breaches occur, financial institutions face scrutiny under PCI DSS, GDPR, FFIEC Cybersecurity Guidelines, and PSD2 — and regulators have shown they'll act on it.
The compliance dimension
Non-compliance penalties are substantial, and regulators publish them:
| Institution | Regulator | Fine | Violation |
|-------------|-----------|------|-----------|
| Intesa Sanpaolo | Italy GDPR | €17.6M | Unlawful mobile app profiling and inadequate notifications during digital migration |
| ACI Worldwide | CFPB | $25M | Using live consumer data in test environments, processing $2.3B in unauthorized mortgage payments |
| S-Bank | Finland GDPR | €1.8M | Authentication bug allowed logging into other customers' accounts via mobile service |
The ENISA Threat Landscape 2024 report confirmed that European banks accounted for 46% of observed cybersecurity incidents (301 incidents), with a 200% year-on-year growth in malware families targeting banking applications. With incident counts rising and regulators actively fining institutions for mobile-specific failures, security gaps in your app aren't an abstract risk — they're a documented liability.
Security best practices during mobile finance app development
Establish security-by-design from day one
Security requirements and threat models must be defined during planning, not bolted on after features are built. Cross-functional collaboration between development and security teams during the design phase cuts remediation costs before they compound.
Fixing a vulnerability in production costs $10,000 versus $100 during the requirements phase—a 100x cost multiplier. Organizations that deploy security AI and automation in prevention workflows save an average of $2.2 million in breach costs compared to those that don't.
Integrate continuous security testing into CI/CD
Security validation must be continuous, not a pre-launch audit. Integrate these testing layers:
- Static Application Security Testing (SAST) — Scans source code during development to catch vulnerabilities like hardcoded credentials, SQL injection flaws, and insecure cryptographic implementations before compilation
- Dynamic Application Security Testing (DAST) — Tests running applications to surface runtime-only issues such as authentication bypasses, session management flaws, and API endpoint vulnerabilities
- Interactive Application Security Testing (IAST) — Combines SAST and DAST approaches, providing real-time visibility during test runs by instrumenting the application and monitoring execution flow
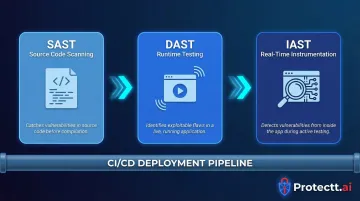
Frame this as continuous validation embedded in your deployment pipeline, not a quarterly penetration test.
Implement multi-layered authentication
Why SMS OTP alone is insufficient:
The FBI IC3 reported over 5,100 Account Takeover complaints in 2025, with losses exceeding $262 million from social engineering and SMS OTP interception. SIM swap fraud—where attackers convince carriers to transfer a victim's number to a new SIM—enables interception of one-time codes. SS7 protocol vulnerabilities in cellular networks can also be exploited to intercept SMS messages in transit.
Stronger alternatives:
- Biometric authentication: Fingerprint and facial recognition tied to device hardware, removing shared-secret vulnerabilities entirely
- Behavioral signals: Typing patterns, touchscreen gestures, and session timing that build unique user profiles for continuous verification
- Silent Mobile Verification: Carrier-network identity verification that performs a cryptographic handshake between the device SIM and mobile network operator — no OTP issued, no OTP to intercept
The goal is phishing-resistant authentication that cannot be intercepted or socially engineered.
Enforce encryption standards
Data in transit:
NIST SP 800-52r2 requires TLS 1.3 support to protect sensitive data during transmission. TLS 1.3 eliminates weak cipher suites, reduces handshake latency, and encrypts more of the connection setup process. PCI DSS v4.0 Requirement 4.2.1 mandates strong cryptography to safeguard Primary Account Numbers during transmission over public networks.
Data at rest:
NIST SP 800-57 Part 1 Rev 5 specifies AES-256 to achieve 256 bits of security strength. Never store credentials, card numbers, or session tokens in plaintext or insecure local storage on devices.
Address supply chain risk through third-party hygiene
Mobile apps rely heavily on third-party libraries, creating hidden vulnerabilities. Synopsys OSSRA 2024 found that 74% of commercial codebases contain high-risk open-source vulnerabilities—a 54% surge from 2022.
Veracode reports that 70% of applications contain flaws in third-party code, and fixing those flaws takes 50% longer than fixing first-party issues.
Mitigate supply chain risk:
- Maintain a Software Bill of Materials (SBOM) — Track all dependencies using NTIA-supported formats per NIST SP 800-161r1; this enables rapid identification of vulnerable components when new CVEs are disclosed
- Vet third-party libraries before integration — Check for known vulnerabilities in the National Vulnerability Database (NVD) and review security advisories
- Audit API endpoints — Validate authentication mechanisms, check for excessive data exposure, and enforce least-privilege access
- Enforce regular updates — Patch newly disclosed vulnerabilities promptly; half of known open-source flaws remain unresolved for eleven months

Runtime and post-launch security for finance apps
Runtime Application Self-Protection (RASP)
RASP is security embedded directly within the application that monitors behavior during execution. Unlike perimeter defenses that operate outside the app, RASP instruments the runtime environment to detect and block attacks in real time.
What RASP protects against:
- Tampering and reverse engineering attempts that try to extract proprietary logic or cryptographic keys
- Debugger attachment that enables dynamic code inspection and manipulation
- Code injection attacks that attempt to execute unauthorized commands
- Hooking frameworks like Frida that modify app behavior at runtime
For high-frequency financial apps, RASP implementation must carry zero performance overhead — latency directly impacts transaction throughput and user experience. Protectt.ai's RASP platform covers 100+ threat vectors while adding no measurable lag to app operations.
AI-driven behavioral monitoring and anomaly detection
User Behavior Analytics (UBA) establishes baseline patterns for each user—typical transaction amounts, login geographies, session timing, device usage—then flags deviations that indicate compromise.
Anomalies detected:
- Unusual transaction amounts or frequencies that deviate from historical patterns
- Logins from new geographies or IP addresses inconsistent with user history
- Atypical session timing, such as access during unusual hours or abnormally long sessions
- Changes in behavioral biometrics like typing speed, swipe patterns, or navigation flows
Automated responses:
- Step-up authentication requiring additional verification before completing transactions
- Session termination to prevent unauthorized access from continuing
- Real-time fraud alerts to security teams for investigation
- Account lockdown pending manual review for high-risk anomalies

Network security at runtime
SSL certificate pinning:
Implement certificate pinning to prevent MITM attacks even on compromised networks. OWASP recommends pinning a leaf certificate with a backup pin — an intermediate CA or alternate pinset — to maintain resilience during certificate rotation. This ensures the app exclusively trusts its intended remote hosts.
Public Wi-Fi warnings:
Display in-app warnings when users connect via public or unsecured Wi-Fi. The FBI explicitly advises: "Be careful when connecting to a public Wi-Fi network and do not conduct any sensitive transactions". Hotel and café networks are high-risk environments where attackers set up fake access points or force networks into using insecure protocols.
Device integrity verification
Rooted and jailbroken device detection:
Compromised devices bypass OS-level security protections. Zimperium data reveals that rooted devices are more than 3.5 times more likely to be targeted by malware, with exposure factors ranging from 3x to 3000x compared to stock devices. Apps should detect these environments and restrict access or alert users accordingly.
SIM binding and device fingerprinting:
Tie account sessions to verified, trusted devices through cryptographic device fingerprinting and SIM card binding. This reduces account takeover risk by ensuring that even if credentials are compromised, the attacker cannot access the account from an unrecognized device.
Common mobile finance app security mistakes that put users at risk
Treating security as a one-time deployment task
Many organizations conduct a pre-launch security audit, ship the app, and consider security complete. This approach fails because the threat landscape evolves continuously—new malware families emerge, unpatched libraries accumulate vulnerabilities, and attackers probe newly released versions for weaknesses.
Security must be an ongoing operational discipline with regular penetration testing, continuous library updates, and incident response drills. Attackers move fast: malicious activity on unsecured networks is detectable within 10 minutes of a device connecting.
Relying exclusively on SMS OTP for authentication
SMS one-time passwords are easy to implement but dangerously vulnerable. SIM swapping, SS7 interception, and social engineering attacks can compromise this channel, leaving account takeover risk high even when users believe they are verified.
Regulators are already acting on this risk: the UAE mandated elimination of SMS OTPs by March 2026, and India requires stronger alternatives by April 2026. Financial institutions must migrate to phishing-resistant methods, including:
- FIDO-based protocols that resist phishing at the protocol level
- Biometric authentication tied to device hardware
- Cryptographic device binding that verifies the registered device, not just the credential
Ignoring third-party and open-source library vulnerabilities
Developers integrate libraries to accelerate feature development, but outdated or unvetted dependencies introduce untracked CVEs into the codebase. Without maintaining an SBOM (Software Bill of Materials), rapid incident response becomes nearly impossible when a widely used library discloses a critical vulnerability.
70% of applications contain flaws in third-party code—making dependency hygiene a non-negotiable part of any security program. To close this gap, teams should:
- Maintain a current SBOM and review it with every release
- Monitor vulnerability databases (NVD, OSV) for CVEs affecting dependencies
- Enforce aggressive patching timelines, especially for high-severity disclosures
Conclusion
Protecting mobile finance apps requires an ongoing security posture, not a single technical decision. The goal is layering defenses across secure development practices, runtime protections, encrypted communications, and behavioral intelligence—making exploitation so difficult and costly that attackers move on.
Development and security teams at financial institutions should evaluate whether their current stack covers all critical layers:
- Code integrity — tamper detection and obfuscation to block reverse engineering
- Device compromise detection — identifying rooted, emulated, or malware-infected environments
- Network security — certificate pinning and encrypted API communication
- Runtime defense — RASP controls that respond to active attacks in real time
- Transaction monitoring — behavioral analytics to flag anomalous activity before fraud occurs
Platforms like Protectt.ai address this full stack through a single SDK, combining RASP, AI-driven threat intelligence, and zero-trust device binding—purpose-built for banks, NBFCs, and FinTechs operating at mobile scale.
The financial sector's disproportionate breach costs—averaging $6.08 million per incident—underscore the ROI of proactive security investment. Every dollar spent on prevention during development saves far more in remediation, regulatory penalties, and customer trust recovery. The organizations that treat security as a first-principles engineering requirement—not an aftermarket addition—are the ones that avoid making that calculation the hard way.
Frequently asked questions
How do I secure the financial apps on my phone?
Enable biometric authentication (fingerprint or facial recognition), keep apps updated to the latest version, avoid using financial apps on public Wi-Fi, and only download apps from official app stores. Use strong device passcodes and enable remote wipe capabilities in case of loss or theft.
Is it safe to keep banking apps on your phone?
Banking apps from established institutions are safe when your phone is protected with a strong passcode, the operating system is kept updated, and you avoid downloading apps from unofficial sources or clicking suspicious links. Modern banking apps use encryption and multi-factor authentication to protect your data.
Is it safe to use a banking app on hotel Wi-Fi?
Hotel Wi-Fi is an unsecured public network where Man-in-the-Middle attacks are possible. Switch to mobile data (your cellular network) for any financial transactions and avoid accessing banking apps on shared or untrusted Wi-Fi networks.
Why is app protection scanning my phone?
App protection scans are security features built into banking apps that check for device integrity issues like rooting, jailbreaking, or malware that could compromise your accounts. This is a proactive defense mechanism protecting your financial data — not a privacy violation.
What encryption is used in mobile banking apps?
Reputable mobile banking apps use TLS 1.3 (Transport Layer Security) to encrypt data in transit between your device and the bank's servers. AES-256 encryption protects data stored on those servers. Both standards ensure intercepted data cannot be read without the correct decryption key.
What are the biggest security risks for mobile finance apps?
The top threats for mobile finance apps include:
- Banking trojans and malware that intercept credentials
- Fake app clones distributed through unofficial channels
- Phishing attacks targeting authentication
- Man-in-the-Middle attacks on unsecured networks
- Account takeover via compromised credentials or SIM swap fraud


