
Introduction
Banking and fintech mobile applications rank among the most targeted attack surfaces in cybersecurity. These apps hold financial credentials, payment data, and transaction histories—making them prime targets for sophisticated threat actors. The threat landscape has intensified dramatically: Kaspersky reported a 196% surge in Trojan banker attacks on smartphones in 2024, reaching 1.24 million attacks. Meanwhile, Group-IB uncovered 27 banking apps injected with malicious functionality using frameworks like Frida and Dobby, with over 300 unique modified banking app samples targeting APAC users.
Mobile security for financial applications is categorically harder than general app development. Development teams face zero tolerance for fraud losses, intense regulatory scrutiny, and advanced persistent threats including overlay attacks, screen scrapers, reverse engineering, and SIM-swap exploits.
A single breach can cost millions in regulatory penalties—RBI's framework alone allows fines up to ₹5 crore per incident—and customer attrition that rarely reverses.
This guide provides a practical security checklist tailored for banking and fintech development teams building and hardening apps for 2026 and beyond.
TLDR:
- Banking apps face 196% surge in Trojan attacks; 27 legitimate apps found modified with malware
- Implement RASP with 100+ security checks to detect and block runtime attacks
- Replace SMS OTPs with cryptographic authentication via device and SIM binding
- Obfuscate code to protect API keys and business logic from reverse engineering
- Automate compliance evidence collection to reduce audit prep by 90%
Secure architecture, code hardening, and supply chain safety
Secure by design: non-negotiable for financial apps
"Secure by design" means embedding security requirements at the architecture phase, not as a post-launch patch. Banking and fintech development teams must align with OWASP MASVS (Mobile Application Security Verification Standard) and NIST frameworks from sprint zero. These baseline standards define security controls for authentication, cryptography, network communication, and platform interaction—creating a blueprint that prevents vulnerabilities before code is written.
Treating security as an afterthought creates technical debt that compounds with every sprint. By contrast, secure architecture establishes guardrails: principle of least privilege for permissions, zero-trust assumptions about device environments, and defense-in-depth across every layer.
Code obfuscation and binary hardening
Attackers reverse-engineer APKs and IPAs to extract API keys, business logic, and hardcoded secrets. Once they decompile your binary, they can identify authentication flows, payment logic, and backend endpoints, then exploit weaknesses or clone functionality.
Critical obfuscation techniques:
- Replace meaningful class, method, and variable names with random alphanumeric strings (identifier renaming)
- Insert dead code and illogical jumps to confuse program execution paths (control flow obfuscation)
- Encrypt API keys, URLs, and sensitive strings so they decrypt only at runtime
- Protect logos, images, and assets from extraction and reuse through resource encryption
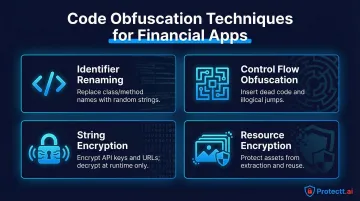
Protectt.ai's CodeProtectt platform applies these protections to both Android (APK/AAB) and iOS (IPA) binaries through a no-code engine — no source code modifications required. It handles AES key encryption, runtime signature validation, and detection of unauthorized version changes out of the box.
Least privilege principle for permissions and backend access
Banking apps should request only permissions strictly necessary for functionality:
- Camera for KYC verification
- Biometrics for authentication
- Location only when required for fraud detection
Every unnecessary permission expands the attack surface. On the backend, service accounts must be scoped tightly to prevent lateral movement after a breach. If an API key is compromised, it should grant access only to the specific service it was designed for—not your entire infrastructure.
Tight permissions cover your own code — but third-party SDKs introduce a different class of risk entirely.
Supply chain risk through third-party SDKs
Unvetted dependencies are a common entry point for financial app compromises.
Zimperium's 2025 report reveals that sideloaded apps are present on 23.5% of enterprise devices, increasing compromise risk through repackaged apps with embedded malicious code.
Supply chain security practices:
- Conduct Software Composition Analysis (SCA) to identify vulnerable dependencies
- Use monitoring tools like OWASP Dependency-Check or Snyk to track CVEs
- Maintain an internal approved-SDK list with security vetting requirements
- Regularly update dependencies to patch known vulnerabilities
- Verify SDK integrity through cryptographic signatures
Secure error handling and logging discipline
Verbose error messages and logs containing PII or transaction data are frequent sources of data leakage. Production logs must be sanitized before deployment, and error responses must never expose stack traces or internal system details to clients.
Logging best practices:
- Mask account numbers, card data, and PII in all logs
- Log security events (failed auth attempts, suspicious activity) separately
- Implement log retention policies aligned with regulatory requirements
- Use structured logging for efficient threat analysis
- Never log authentication credentials or session tokens
Authentication, zero-trust identity, and session security
Why password-only authentication is insufficient
The 2026 threat model has made single-factor authentication untenable for financial apps. Three attack categories drive this:
- Credential stuffing — billions of leaked credentials from past breaches fuel automated login attacks
- Phishing — sophisticated fake login pages specifically targeting mobile banking users
- SIM-swap fraud — fraudsters hijack phone numbers to intercept SMS verification codes
Each of these attacks exploits a different weakness in password-only flows. Defending against all three requires layered authentication: biometrics (fingerprint, Face ID), device binding, and step-up authentication for high-risk actions like fund transfers or beneficiary additions.
Multi-factor authentication beyond SMS OTPs
SMS OTPs are vulnerable to SIM-swap attacks and SS7 protocol exploits. Financial institutions must transition to cryptographically stronger alternatives:
TOTP (Time-based One-Time Passwords) – Generate codes locally on the device using shared secrets; resistant to interception but still vulnerable to phishing.
FIDO2/WebAuthn Passkeys – Use public-key cryptography with hardware-backed security; phishing-resistant and eliminate shared secrets.
Network-Based Silent Verification – Authenticate users through secure carrier network channels without exposing OTP codes at all. Protectt.ai's Silent Mobile Verification, for example, completes this via a cryptographic handshake between the SIM card and mobile network operator — eliminating the exposed OTP factor entirely.

Zero trust device and SIM binding
Even when credentials are compromised, device and SIM binding can stop account takeover. Binding an authenticated session to a specific device fingerprint and SIM identity ensures only the legitimate device holder can access the account.
Protectt.ai's AppBind uses LSAP (Legitimate SIM Authentication Protocol) and the proprietary 3-Way Hairpin methodology to validate mobile numbers at registration and continuously verify physical SIM possession. When a SIM-swap is attempted, the hijacked SIM becomes immediately invalid — the cryptographic challenge relies on a unique secret key stored only in the original SIM card.
Secure session management requirements
Sessions must use short-lived tokens (JWT with appropriate expiry), automatically time out after inactivity, support remote session revocation, and require re-authentication before sensitive operations.
Session security checklist:
- Implement JWT tokens with 15-30 minute expiry for access tokens
- Use refresh tokens with secure rotation mechanisms
- Enforce automatic logout after 5-10 minutes of inactivity
- Enable remote session revocation via admin dashboard
- Require step-up authentication for high-risk transactions
- Invalidate all sessions immediately upon password change
Server-side authentication validation
All authentication decisions must be enforced on the backend — client-side checks are bypassable and should never be the final gate. Attackers routinely modify app binaries to circumvent local logic, but they cannot forge cryptographic signatures validated server-side.
Token storage on the device must use platform-native secure storage: iOS Keychain and Android Keystore, both backed by hardware TEE (Trusted Execution Environment) or StrongBox where available.
Data encryption, secure storage, and privacy compliance
Encryption at rest for banking apps
Sensitive data—account numbers, PAN data, transaction history, biometric templates—should never be stored in plaintext. Use AES-256 for local storage, platform-native encrypted storage (EncryptedSharedPreferences on Android, Keychain on iOS), and hardware-backed key storage where available.
Hardware-backed security advantages:
- Keys stored in TEE or Secure Enclave cannot be extracted
- Cryptographic operations occur in isolated hardware
- Brute-force attacks become computationally infeasible
- Compliance frameworks recognize hardware-backed storage as best practice
Encryption in transit requirements
All communication between mobile apps and backends must use TLS 1.2 or higher (enforce TLS 1.3 where possible). Enforce strict certificate validation and certificate pinning to prevent MITM attacks, especially on public Wi-Fi networks.
Certificate pinning considerations:
- Pin public keys rather than certificates to survive certificate rotation
- Implement backup pins to prevent outages during certificate updates
- Use dynamic pinning with secure update mechanisms
- Monitor certificate expiration dates proactively
- Test pinning implementation thoroughly before production
Data minimization and PII handling
Banking apps should not cache sensitive data beyond immediate need. Prevent screenshots and screen recordings of sensitive screens using FLAG_SECURE on Android or overlaying a privacy screen during app backgrounding on iOS (via applicationWillResignActive). Mask data in UI fields and memory after use.
Data minimization practices:
- Clear sensitive data from memory immediately after use
- Disable clipboard access for password and OTP fields
- Prevent screen capture during authentication and transaction flows
- Implement secure keyboard input for sensitive fields
- Avoid logging PII or transaction details in analytics
Compliance-aligned data handling
PCI DSS requirements (for cardholder data) and data protection laws (GDPR, regional regulations) create specific obligations around how financial data is stored, transmitted, and deleted. Non-compliance carries regulatory penalties, audit failures, and reputational damage—each with direct financial consequences.
Key compliance obligations for banking app data handling include:
- Encrypting cardholder data at rest and in transit per PCI DSS scope
- Honoring data subject deletion requests under GDPR and regional equivalents
- Maintaining audit trails for data access and processing activities
- Documenting data retention and disposal policies
Protectt.ai holds PCI DSS, ISO 27001, ISO 42001, and ISO 22301 certifications. Banking and fintech teams integrating the platform can map directly to these frameworks during audits, reducing the compliance documentation burden their own security teams carry.
Runtime application protection and application integrity
Runtime Application Self-Protection (RASP)
RASP operates inside the app at runtime to detect and respond to attacks in real time—including hooking attempts via tools like Frida, code injection, reverse engineering, and debugging. Unlike perimeter defenses that assume a safe environment, RASP recognizes that banking apps run on uncontrolled user devices where the operating system itself may be compromised.
Protectt.ai's platform implements RASP with 100+ security checks—covering rooted/jailbroken device detection, emulator detection, and tamper response—with no performance overhead. Behavioral analysis runs continuously across device activity, network interactions, and application behavior to flag anomalies and enforce security responses in real time.
RASP security checks include:
- Detection of hooking frameworks (Frida, Xposed, Cydia Substrate)
- Identification of debugging tools and reverse engineering attempts
- Runtime code integrity verification
- Memory tampering detection
- Dynamic analysis prevention
- Screen overlay attack detection

Jailbreak and root detection
Zimperium's 2025 report reveals that 1 in 400 Android devices is rooted and 1 in 2,500 iOS devices is jailbroken. These compromised environments remove OS-level sandboxing that banking apps depend on for security.
Banking apps must detect compromised devices and respond appropriately:
- Warning the user – Inform them of increased security risk
- Limiting functionality – Disable high-risk operations like fund transfers
- Blocking access – Prevent app launch on severely compromised devices
The response should align with your risk tolerance and regulatory requirements. Some institutions block all access on rooted devices; others allow read-only access while restricting transactions.
App integrity verification at runtime
Use Play Integrity API (Android) and App Attest API (iOS) to verify that the app binary has not been tampered with and is running on a genuine device. These APIs provide hardware-backed cryptographic proof of app legitimacy—a necessary safeguard against repackaged banking apps distributed through unofficial channels.
However, advanced root-hiding techniques can bypass attestation mechanisms. Treat attestation APIs as one layer in a broader defense strategy, and always validate results server-side—client-side verification alone is not sufficient.
API security and secure network communication
API authentication and authorization hardening
Banking app APIs require multiple layers of protection at the authentication and data handling level. Core requirements include:
- Use OAuth 2.0 with short-lived access tokens — not static API keys
- Validate and sanitize all inputs server-side to prevent injection attacks
- Enforce strict output encoding to prevent data leakage
- Apply rate limiting to block brute force and enumeration attempts
Reference the OWASP API Security Top 10 as your framework:
- Broken object level authorization
- Broken authentication
- Broken object property level authorization
- Unrestricted resource consumption
- Broken function level authorization
- Unrestricted access to sensitive business flows
- Server-side request forgery
- Security misconfiguration
- Improper inventory management
- Unsafe consumption of APIs
Rate limiting strategies:
- Limit authentication attempts to 3-5 per minute per IP
- Throttle API calls to prevent enumeration attacks
- Implement progressive delays after failed attempts
- Monitor for distributed attacks across multiple IPs
Rate limiting addresses individual IP abuse — but transport-layer security is equally critical. Certificate pinning protects your APIs from man-in-the-middle attacks at the network level.
Certificate pinning trade-offs and implementation
Certificate pinning is essential for banking APIs to prevent MITM attacks, but teams must build in reliable update and fallback mechanisms. Hardcoded pins cause outages when certificates rotate.
Pinning best practices:
- Pin public keys rather than full certificates
- Include backup pins for certificate rotation
- Implement dynamic pinning with secure update channels
- Monitor certificate expiration proactively
- Test pinning thoroughly in staging environments
Network security configuration best practices
Enforce HTTPS-only through Android's Network Security Config and iOS App Transport Security (ATS). Block cleartext traffic and avoid mixed-content patterns. In banking apps, user-installed certificates are a known attack vector — rogue CAs installed on a device allow attackers to intercept traffic silently.
Network security checklist:
- Disable all cleartext HTTP traffic
- Enforce TLS 1.2 minimum (TLS 1.3 preferred)
- Block user-installed CA certificates
- Implement certificate pinning for critical APIs
- Use separate certificate pins for different environments
Security testing, regulatory compliance, and continuous monitoring
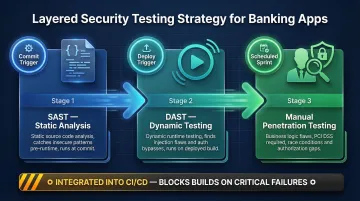
Layered testing strategy
SAST (Static Application Security Testing) – Analyze source code to catch insecure coding patterns early, before runtime.
DAST (Dynamic Application Security Testing) – Test running apps to find runtime vulnerabilities like injection flaws and authentication bypasses.
Manual Penetration Testing – Required for PCI DSS compliance and to catch business logic flaws that automated tools miss, such as improper authorization or race conditions.
Integrate these into your CI/CD pipeline, not as one-time pre-release checks. Automated security testing should block builds that fail critical security thresholds.
Regulatory compliance frameworks
PCI DSS mandates specific controls for apps handling card data. Financial regulators (RBI in India, FCA in UK) issue mobile banking security guidelines that development teams must track. ISO 27001 and SOC 2 affect organizational security posture.
Teams that automate compliance evidence collection spend less time on manual audit work. Protectt.ai's platform cuts manual compliance work by 80% and audit preparation time by 90% through automated policy enforcement and audit trail generation. Its PCI DSS, ISO 27001, ISO 42001, and ISO 22301 certifications mean clients can build on an already-certified security foundation.
Compliance automation benefits:
- Transform weeks of manual audit preparation into automated report generation
- Proactive risk identification prevents regulatory penalties
- Continuous policy enforcement reduces gaps between audits
- Automated evidence collection reduces operational costs
Real-time threat monitoring and incident response
Compliance controls cover what you build — monitoring covers what happens after launch. Behavioral analytics flag anomalies in real time: unusual transaction patterns, logins from unfamiliar devices, repeated failed biometric attempts. Teams must maintain documented incident response plans covering emergency app updates, remote session revocation, and forensic log access.
Incident response capabilities:
- Real-time alerting for suspicious activity
- Remote session revocation across all devices
- Emergency app update distribution via app stores
- Forensic logging for post-incident analysis
- Automated threat intelligence integration
Protectt.ai's platform uses AI/ML-driven behavioral analysis to detect and respond to new attack techniques as they emerge — reducing dependence on manual threat hunting between release cycles.
Frequently asked questions
What are the most critical mobile security threats targeting banking apps in 2026?
Account takeover via credential stuffing and SIM-swap attacks, overlay and screen scraping attacks, reverse-engineered APKs distributed through unofficial channels, and AI-powered phishing campaigns targeting mobile banking users represent the top threats. The 196% surge in Trojan banker attacks demonstrates the scale and sophistication of current threats.
How does Runtime Application Self-Protection (RASP) differ from traditional mobile security testing?
RASP operates inside the app at runtime to detect and block active attacks, while testing (SAST/DAST/pentesting) identifies vulnerabilities before deployment. RASP provides complementary runtime defense, not a replacement for pre-deployment security testing.
What compliance frameworks must banking mobile apps adhere to?
PCI DSS for card-handling apps, ISO 27001 for information security management, regional banking regulator guidelines such as RBI's mobile banking circular in India, and applicable data protection laws like GDPR. Non-compliance risks regulatory fines, loss of operating licenses, and lasting reputational damage.
Why are SMS OTPs considered insecure for banking authentication in 2026?
SMS OTPs are vulnerable to SIM-swap attacks, SS7 protocol exploits, and social engineering. Alternatives like FIDO2 passkeys, biometric authentication, or network-based silent verification offer stronger fraud resistance — they use cryptographic verification that cannot be intercepted or redirected, eliminating the exposed OTP factor entirely.
How should banking apps handle sensitive data on a user's device to minimize breach risk?
Encrypt data at rest using AES-256 and hardware-backed keystores (iOS Keychain, Android Keystore with TEE/StrongBox), minimize local data retention to only what's immediately necessary, mask PII in memory and UI after use, and prevent screen capture of sensitive screens using platform-native controls like FLAG_SECURE.


