
Introduction
Fintech and mobile banking apps sit at the top of every cybercriminal's target list. When users entrust these platforms with money, identity documents, transaction histories, and financial credentials, a single breach doesn't just expose data — it drains accounts, destroys credit records, and enables mass identity theft.
The US average data breach cost surged to $10.22M in 2025, with financial sector breaches averaging $6.08M globally in 2024. These figures cover remediation, user attrition, regulatory penalties, and reputational damage — any of which can end a fintech entirely.
Security and compliance now operate as interlocked requirements, not parallel workstreams. Regulators like FinCEN, the FCA, and RBI are aggressively penalizing systemic failures: FinCEN assessed a record $1.3B penalty against TD Bank in 2024 for AML program failures, and the FCA fined Nationwide £44M in 2025 for inadequate financial crime controls.
Fintechs that treat either as an afterthought face license revocation, operational suspension, and penalties that scale with breach severity.
This guide covers:
- The non-negotiable security features every fintech banking app must have
- Compliance standards and the regulators enforcing them
- Authentication best practices that have moved beyond OTPs
- Data protection protocols that reduce breach impact
- How to evaluate a purpose-built security platform for fintech's threat landscape
TLDR
- Fintech apps face mobile-specific attack vectors growing rapidly: mishing accounts for 54% of iOS threats, while PWAs bypass app store security entirely
- Core security must-haves: MFA, end-to-end encryption, RASP, certificate pinning, and AI-driven fraud detection
- Compliance is mandatory: PCI DSS, ISO 27001, AML/KYC, and data privacy laws (GDPR, India's DPDP Act) with escalating enforcement
- Authentication has evolved: biometrics, silent mobile verification, and Zero Trust device binding replace vulnerable SMS OTPs
- AI-powered monitoring platforms cut manual compliance effort and catch threats before they escalate
Why security and compliance are non-negotiable for fintech banking apps
Financial apps face disproportionate attack rates
The 2025 Verizon DBIR recorded 3,336 security incidents in the Financial and Insurance sector, with 927 resulting in confirmed data disclosure. When a banking app is compromised, damage is immediate and material: accounts are drained, identities stolen, credit records manipulated. Financial industry enterprises took an average of 168 days to identify and 51 days to contain breaches in 2024, giving attackers months to exploit compromised credentials.
The attack pattern is clear: 90% of financial sector breaches are financially motivated, targeting personal data (54%) and credentials (22%). System intrusion, social engineering, and web application attacks represent 74% of breaches—attack vectors that mobile banking apps are uniquely vulnerable to.
Mobile banking's unique risk profile
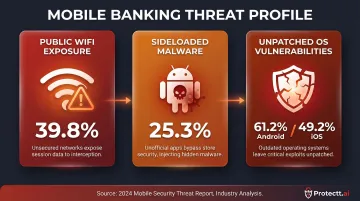
Mobile banking introduces attack surfaces desktop banking never faced. Three device-level risks stand out:
- Public WiFi exposure: 39.8% of iOS threats originate from network-based man-in-the-middle attacks on unsecured networks
- Sideloaded malware: 25.3% of Android devices run sideloaded applications that bypass official app store security checks
- Unpatched OS vulnerabilities: 61.2% of Android devices and 49.2% of iOS devices run outdated OS versions, leaving known exploits open
Password reuse across platforms creates cascading failure points. When credentials leak from one service, attackers systematically test them against banking apps. Account takeover fraud cost consumers $16B in 2024, with 5.1 million victims—a 9% increase from the prior year.
Regulatory consequences are escalating
Non-compliance isn't just a legal risk—it's an existential threat. Regulators can suspend operations, revoke licenses, and impose fines that scale with breach severity:
| Regulator | Entity | Penalty | Year | Violation |
|---|---|---|---|---|
| FinCEN (US) | TD Bank | $1.3B | 2024 | Willful failure to implement AML program |
| FCA (UK) | Nationwide | £44M | 2025 | Inadequate anti-financial crime systems |
| RBI (India) | Sutex Co-op Bank | ₹5 Lakh | 2024 | Failure to conduct mobile app penetration testing |
These penalties share a common thread: regulators no longer treat security failures as isolated technical incidents. They treat them as evidence of systemic operational failure—and penalize accordingly.
Core security features every fintech banking app must have
Multi-factor authentication (MFA)
MFA is the baseline across all major regulatory frameworks. It requires users to verify identity through at least two independent factors: something they know (password), something they have (device or token), or something they are (biometric). This prevents credential-stuffing attacks where stolen passwords alone can't grant access.
The FBI IC3 2024 report recorded $25.9M in losses from SIM-swap attacks, where attackers hijack phone numbers to intercept authentication codes. The industry is shifting toward app-based authenticators and biometrics that can't be intercepted via telecom infrastructure.
Runtime Application Self-Protection (RASP)
RASP operates as an in-app security layer that detects and blocks attacks in real time from within the application itself. Unlike perimeter defenses that protect network boundaries, RASP identifies threats directly at the application layer:
- Reverse engineering and code tampering attempts
- Hooking frameworks (such as Frida and Xposed)
- Emulator environments and debugging sessions
- App spoofing and binary modification
Mobile fintech apps face a particular challenge: the device environment can't be controlled. Attackers using dynamic instrumentation frameworks like Frida can bypass purely client-side RASP, making server-side validation and cryptographic binding essential alongside in-app defenses.
Protectt.ai offers 100+ RASP security features covering runtime hooking, app spoofing, reverse engineering, and debugging attempts — maintaining protection even on devices that enterprise teams don't manage.
Certificate pinning and secure communication
All data in transit must be protected using TLS 1.3, the current standard for encrypted communication. Certificate pinning adds an additional layer by ensuring the app only communicates with verified, legitimate servers—preventing man-in-the-middle attacks that intercept financial data between the app and backend systems.
Without certificate pinning, attackers on compromised networks can present fraudulent certificates and decrypt supposedly secure traffic. This is particularly dangerous on public WiFi networks where network-based threats represent 39.8% of iOS security incidents.
Device binding and root/jailbreak detection
Device fingerprinting and Zero Trust device binding tie a user's authenticated session to a known, verified device. When a login occurs from a new or unrecognized device, the system flags it for step-up verification—requiring additional authentication factors before granting access.
Root and jailbreak detection identify devices where OS protections have been stripped. 1 in 400 Android devices is rooted, and 1 in 2,500 iOS devices is jailbroken. These devices are prime targets for credential theft because built-in security controls have been disabled.
Protectt.ai's AppBind solution implements Zero Trust device and SIM binding through proprietary LSAP and SSiD technologies, creating a secure binding between users, devices, and SIM cards that prevents unauthorised access even when credentials are compromised.
Code obfuscation and anti-tampering
Mobile app binaries can be reverse-engineered by attackers to understand business logic, extract API keys, or create fraudulent lookalike apps. Code obfuscation transforms source logic into unreadable code while maintaining functionality, making reverse engineering exponentially more difficult.
Integrity checks verify the app hasn't been tampered with at runtime. If an attacker modifies the app binary to disable security controls or inject malicious code, integrity verification detects the tampering and terminates the session before damage occurs.
Real-time fraud detection and user behaviour analytics
AI/ML-driven monitoring continuously profiles normal user behaviour—transaction patterns, device usage, geolocation, typing rhythms, and app navigation timing. When activity deviates from established baselines, the system flags anomalies and can automatically trigger step-up authentication or session termination.
Organisations using AI and automation extensively shortened breach times by 80 days and lowered average breach costs by $1.9M compared to those without these solutions. Protectt.ai's platform monitors billions of mobile app sessions globally and prevents 200 million+ cyber threats and fraud events monthly through AI-driven threat intelligence and user behaviour analytics.
Key compliance standards governing fintech banking apps
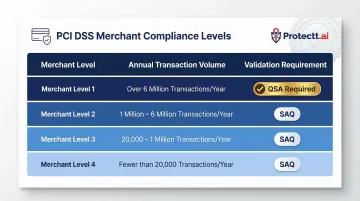
PCI DSS (Payment Card Industry Data Security Standard)
Any fintech handling card payments must comply with PCI DSS. Version 4.0.1, published June 2024, specifies how cardholder data is stored, processed, and transmitted. Requirements include:
- Requirement 4.2: Primary Account Numbers (PAN) must be protected with strong cryptography during transmission over open, public networks
- Requirement 3.6.1: Procedures to protect cryptographic keys used to protect stored account data
- Mobile acceptance standards: The PCI SSC Mobile Payments on COTS (MPoC) standard provides security requirements for solutions enabling merchants to accept payments using commercial off-the-shelf mobile devices
Compliance validation requirements scale with transaction volume:
| Merchant Level | Annual Transaction Volume | Validation Requirement |
|---|---|---|
| Level 1 | > 6,000,000 | Annual Report on Compliance (ROC) by QSA |
| Level 2 | 1,000,000 – 6,000,000 | Annual Self-Assessment Questionnaire (SAQ) |
| Level 3 | 20,000 – 1,000,000 e-commerce | Annual SAQ |
| Level 4 | < 20,000 e-commerce | Annual SAQ |
ISO 27001 (Information Security Management System)
ISO/IEC 27001:2022, published October 2022, specifies requirements for establishing, implementing, maintaining, and continually improving an information security management system (ISMS). For fintech auditors and banking partners, certification signals that security governance is structured and verifiable—not improvised.
Annex A has been updated to align with ISO/IEC 27002:2022, which contains 93 controls (11 new) organized into 4 themes. Achieving certification confirms that an organization's security controls have been independently audited against a globally recognized baseline.
AML / KYC requirements
Anti-Money Laundering and Know Your Customer obligations are core compliance requirements. Fintechs must verify user identities at onboarding (KYC), screen against sanctions lists, and monitor for suspicious transaction patterns (AML). Failure here results in license revocation, not just fines—as demonstrated by FinCEN's $1.3B penalty against TD Bank for willful failure to file Suspicious Activity Reports.
Data privacy regulations
Two regulations carry the most direct impact for fintech apps operating across global and Indian markets:
GDPR (General Data Protection Regulation)
- Article 33(1): Controllers must notify supervisory authorities within 72 hours of discovering a personal data breach
- Article 5(1)(c): Data minimisation — personal data must be adequate, relevant, and limited to what is necessary
India DPDP Act 2023
- Section 6: Every consent request must include a notice identifying the personal data collected and its processing purpose
- Section 8(5): Data Fiduciaries must implement reasonable security safeguards to prevent breaches, with penalties up to ₹250 crore for failures
Regulatory body requirements by region
| Regulator | Region | Key Requirement |
|---|---|---|
| RBI | India | Digital Lending Directions 2025: apps must not store personal data beyond minimal necessary data; Authentication Directions 2025 mandate two distinct authentication factors, with at least one dynamic factor per transaction |
| FCA / PSD2 | UK | Strong Customer Authentication (SCA) required for all electronic payment transactions; contactless exemptions apply under £100, with a £300 cumulative or five-transaction limit |
| FFIEC | US | 2021 guidance: single-factor authentication is inadequate for high-risk transactions; Multi-Factor Authentication recommended using memorized secrets, out-of-band devices, biometrics, or cryptographic keys |
User authentication and identity verification: the first line of defense
The evolution from passwords to passwordless
Authentication in fintech has evolved from static passwords to MFA, and now toward passwordless and continuous authentication models. Biometrics will authenticate over $3 trillion of payment transactions in 2025, up from $404B in 2020. The FIDO Alliance's 2024 report found that 53% of surveyed users have enabled passkeys on at least one account, with 61% considering them more convenient than passwords and 58% considering them more secure.
Biometric authentication—fingerprint, face ID—combines low friction with high security, provided biometric data is processed on-device and never transmitted to servers. This prevents biometric data from being intercepted or stored in centralized databases that become high-value targets.
Silent mobile verification: eliminating SIM-swap vulnerabilities
Silent Mobile Verification (SMV) represents the next generation of zero-friction authentication. Rather than sending an OTP via SMS, SMV verifies identity directly through the carrier network in a silent background check. The authentication relies on a unique, secret key stored within the physical SIM card itself.
When a SIM is swapped, the fraudster's device cannot complete the cryptographic handshake — they don't possess the legitimate user's SIM card with its embedded secret key. A spoofed number fails immediately for the same reason: the cryptographic challenge requires the original SIM, making the attempt impossible to authenticate.
Protectt.ai's AppBind solution implements this through proprietary LSAP technology for mobile number validation and a 3-Way Hairpin Methodology that creates a robust acknowledgement loop: Mobile → SMS Gateway → Server → Mobile. The entire process completes in 2-4 seconds, with no OTP for attackers to intercept and no extra steps for the user.
Layered access control
Authenticated users should not receive blanket access. Viewing an account balance may require one factor, but initiating a transfer should trigger an additional verification step. Time-based, location-based, and risk-scored access controls add adaptive layers that respond to contextual signals:
- Terminates sessions automatically after inactivity, requiring re-authentication before resuming
- Triggers step-up verification when access originates from new regions or flags impossible travel patterns
- Generates real-time trust scores by combining device risk, AI analysis, and behavioural insights — approving legitimate users instantly while blocking anomalous requests

Data protection, encryption, and fraud prevention
Encryption at every layer
Fintech apps require encryption at every layer:
- Data at rest: AES-256 encryption for stored user records, transaction histories, and account details
- Data in transit: TLS 1.3 for all communication between app and backend systems
- Field-level encryption: Additional encryption for particularly sensitive data like account numbers or card details, ensuring that even if a database is compromised, the most critical data remains encrypted
Tokenisation replaces sensitive data with non-sensitive surrogates during processing, limiting the scope of any breach. If payment card data is tokenised, attackers who compromise the system obtain tokens that are useless outside the specific transaction context.
Data minimisation and governance
GDPR Article 5(1)(c) requires collecting only data that is necessary for the stated purpose, with clear retention and deletion policies. India's DPDP Act Section 6 requires that consent requests specify the personal data and processing purpose.
Fintechs that store excess data unnecessarily expand their regulatory and security liability. Every data field stored represents potential breach exposure and regulatory scrutiny. Data minimisation reduces attack surface and simplifies compliance.
Real-time transaction monitoring
AI-driven systems score each transaction against behavioural baselines and known fraud patterns. When a transaction deviates from expected behaviour, the system automatically blocks it or triggers reverification without adding friction to legitimate users. Deviation signals include:
- Unusual transaction amount relative to historical spend
- Unexpected merchant category or geography
- Atypical time of day or access location
- Sudden high-frequency transaction patterns
The financial impact is measurable: organisations using AI and automation extensively lowered average breach costs by $1.9M compared to those without these capabilities. For fintech teams managing thousands of daily transactions, that gap directly affects both customer trust and regulatory standing.
How to choose a fintech security and compliance platform
Core evaluation criteria
Evaluating a fintech security platform requires checking coverage across four layers: app, device, network, and transaction. Start with these questions:
Key questions to ask:
- Runtime protection: Does the platform detect and block reverse engineering, code tampering, hooking frameworks, and emulator environments at runtime?
- Device integrity: Does it validate device integrity through root/jailbreak detection, device fingerprinting, and Zero Trust device binding?
- Network security: Does it enforce certificate pinning, detect man-in-the-middle attacks, and protect against unsecured WiFi risks?
- Fraud detection: Does it profile user behaviour and flag anomalies through AI/ML-driven analytics?
- Performance: What is the SDK's resource consumption impact on CPU, memory, and battery life?

Certifications and regulatory alignment
A credible security platform should hold relevant certifications—ISO 27001, PCI DSS, ISO 22301—and demonstrate compliance posture to regulators on behalf of its clients. Automated audit report generation and compliance documentation significantly reduce preparation burden.
Protectt.ai holds ISO 27001, PCI DSS, ISO 22301, and ISO 42001 certifications and serves major institutions including RBL Bank, Yes Bank, BSE, Bajaj Finserv, and Equitas Bank. This existing certification stack shortens go-to-market timelines and cuts the manual effort of demonstrating regulatory compliance from scratch.
Implementation and DevSecOps integration
The best security tools automate policy enforcement, reduce false positives, and integrate with existing DevSecOps pipelines. Development teams bypass or deprioritise security tools that slow workflows or create friction.
A Forrester TEI study found that automated compliance reporting reduced audit preparation efforts by $232,000 over three years. DevSecOps automation reduced the time teams spend managing environments and remediating issues by 8-15%, resulting in savings of $3.1M.
Platforms that support dynamic, policy-driven adaptive controls let teams push policy updates without app redeployment — a practical advantage when a new regulatory requirement drops or a threat vector shifts mid-cycle.
Frequently asked questions
What are the compliance standards of fintech?
Fintechs must comply with PCI DSS for payment data security, ISO 27001 for information security management, AML/KYC for user verification and transaction monitoring, GDPR or equivalent data privacy laws for data protection, and regional regulatory requirements from bodies like RBI (India), FCA (UK), or FFIEC (US) depending on operating jurisdiction.
How secure is fintech?
Modern fintech apps can be highly secure when built with layered defenses—MFA, RASP, encryption, device binding, and real-time fraud monitoring. Security posture varies widely across providers, so evaluating a fintech's specific controls before onboarding is essential for users and partners alike.
What are the 5 key technologies in fintech?
The five key technologies are AI/ML for fraud detection and credit scoring, blockchain for transaction transparency, cloud infrastructure for scalability, biometric authentication for identity verification, and open banking APIs for interoperability. RASP and encryption serve as the security layer that all five depend on to function safely.
What are the 4 pillars of fintech?
The four pillars are:
- Security — protecting data and transactions
- Compliance — meeting regulatory obligations
- User Experience — frictionless access
- Innovation — leveraging AI, APIs, and cloud to deliver new financial services
What is fintech software?
Fintech software refers to applications and platforms that deliver financial services digitally, including mobile banking apps, payment gateways, lending platforms, insurance tech, and investment tools. Regulatory frameworks require security controls to be built in from the design phase, not added after deployment.


