
Introduction
Financial sector data breaches now cost organizations an average of $6.08 million per incident—22% higher than the global average—according to IBM's 2024 Cost of a Data Breach report. In the US, this figure spikes to $10.22 million. Beyond the direct financial toll, breaches erode user trust, trigger regulatory penalties, and inflict lasting reputational damage. Finland's S-Pankki learned this lesson the hard way: a mobile app authentication flaw resulted in combined fines of €9.47 million from GDPR and financial regulators—one of the largest penalties in Finnish banking history.
Fintech apps operate in a uniquely hostile environment in 2026. They handle sensitive financial data across mobile-first surfaces where attackers deploy AI-powered credential stuffing, deepfake-based fraud, runtime manipulation tools, and SIM-swap attacks targeting weak authentication flows.
Regulators are accelerating this pressure: India's Reserve Bank (RBI) is mandating the phase-out of SMS OTPs by April 2026, pushing the industry toward dynamic, device-bound authentication. This guide covers the specific controls fintech teams need in 2026—from hardening authentication and runtime protection to securing APIs and meeting compliance requirements without slowing delivery.
TL;DR
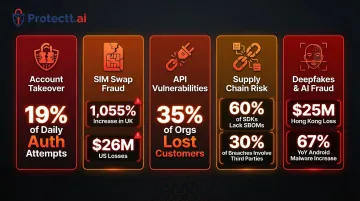
- Fintech apps face AI-powered attacks, API exploits, SIM swap fraud (up 1,055% in the UK), and runtime manipulation
- Multi-factor authentication (MFA), end-to-end encryption, and secure API design are mandatory baselines
- Runtime Application Self-Protection (RASP) catches threats static security misses — jailbroken devices, dynamic instrumentation, and in-app tampering
- PCI DSS, GDPR, and regional mandates set the compliance floor—not the ceiling
- Avoiding common mistakes like skipping penetration testing and relying on single-layer security matters as much as the best practices themselves
The fintech app threat landscape in 2026
Attackers have evolved beyond traditional network perimeters to target mobile endpoints directly. AI now automates credential stuffing, generates deepfake identities to bypass eKYC, and probes API endpoints at scale.
Account Takeover (ATO) and Transaction Fraud lead the threat landscape. Credential stuffing accounts for 19% of all daily authentication attempts, peaking at 44% on single days, according to Verizon's 2025 Data Breach Investigations Report.
SIM swap fraud has industrialized in parallel: the UK's Cifas reported a 1,055% increase in unauthorized SIM swaps in 2024, while the FBI tracked $26 million in losses from SIM swapping in the US alone. These attacks bypass OTP-based authentication by hijacking phone numbers—prompting regulators to deprecate SMS 2FA entirely.
API vulnerabilities have become a critical attack surface. Fintech apps depend heavily on APIs for payments, account access, and third-party integrations. Traceable's 2024 State of API Security report found that 35% of organizations lost customers directly due to API-related data breaches. Insecure endpoints, weak authentication, and over-permissive access controls make APIs prime targets.
Man-in-the-Middle (MitM) attacks exploit unsecured communication channels, especially on public Wi-Fi networks. Without proper TLS 1.3 implementation and certificate pinning, attackers intercept financial data in transit, exposing credentials and transaction details.
Supply chain risk compounds these threats. Over 60% of top Android and iOS third-party SDKs ship as precompiled binaries with incomplete software bills of materials (SBOMs), according to Zimperium's 2025 Global Mobile Threat Report. Verizon's 2025 DBIR notes that 30% of all breaches now involve a third party—making vendor vetting and software composition analysis (SCA) essential.
Deepfakes and AI-amplified fraud are actively exploiting identity verification gaps. FinCEN issued formal alerts in 2024 about GenAI bypassing mobile eKYC systems, while a single Hong Kong deepfake incident resulted in $25 million in losses. Simultaneously, banking trojans like Albiriox and Herodotus abuse Android accessibility features to perform on-device fraud, draining accounts during live sessions—a 67% year-over-year increase in Android malware-driven financial transactions.
Core security practices for fintech apps
Security must be embedded across the full app lifecycle—from code to device to network—not treated as a final checklist item before launch.
Secure authentication and identity verification
Multi-factor authentication (MFA) is the baseline, but OTP-only approaches are increasingly vulnerable. SIM swap attacks and phishing have made SMS 2FA unreliable. India's RBI now mandates that at least one authentication factor be dynamic and non-SMS by April 2026.
Stronger alternatives include:
- Biometric authentication — Fingerprint and facial recognition tied to device hardware (Secure Enclave on iOS, StrongBox on Android)
- Silent SIM-based verification — Cryptographic handshakes between the device's SIM and carrier network eliminate OTPs entirely while verifying identity in 2-4 seconds
- Device binding — Tying user identity to a specific device-SIM combination prevents unauthorized access even if credentials are compromised

Stronger authentication methods address the credential layer, but identity verification can't stop at login. Zero Trust principles require continuous validation of every session, device, and user throughout the entire interaction—not just at the point of entry. Behavioral analytics reinforce this by detecting anomalies like unusual transaction amounts, unfamiliar login locations, or rapid session changes that signal account compromise even when credentials are valid.
Data encryption and secure storage
TLS 1.3 for data in transit and AES-256 for data at rest are the required standards. NIST SP 800-52 Revision 2 mandates TLS 1.3 support as of January 2024, and PCI DSS v4.0.1 requires strong cryptography for all transmissions over public networks.
Sensitive data must never be stored in plaintext on the device. Platform-native secure storage is essential:
- Android Keystore — Use StrongBox KeyMint (API 28+) for hardware-backed key storage with
setIsStrongBoxBacked(true) - iOS Keychain and Secure Enclave — All biometric data and cryptographic keys remain exclusively in the Secure Enclave, never exposed to the main system
Avoid logging sensitive values in debug output or storing keys in application code or shared preferences. Hardware-backed encryption ensures that even if a device is compromised, cryptographic keys remain protected.
API security and secure communication
APIs connect every layer of a fintech app—payment processors, identity services, transaction engines—which makes them the most frequently targeted attack surface. Essential API security controls include:
- Strong authentication on every endpoint — Never trust client-side validation alone
- Input validation — Prevent injection attacks by sanitizing all user input
- Rate limiting — Block automated abuse and credential stuffing attempts
- Certificate pinning — Prevent MitM attacks by validating server certificates against known values
Certificate pinning does introduce operational risk worth planning for. OWASP MASTG recommends always including a backup key so certificate rotations don't break app connectivity. It's also worth noting that pinning only addresses network interception — if an attacker controls the device, they can disable pinning using dynamic instrumentation (tools that hook into running app processes at runtime).
Regularly audit third-party API integrations and avoid exposing backend logic through over-permissive endpoints. Platforms like Protectt.ai's ApiProtectt provide real-time API threat detection, behavioral analysis, and bot mitigation to secure API communications at the SDK level.
Code protection and anti-tampering
Reverse engineering of unprotected APKs and IPAs exposes business logic, cryptographic keys, and API credentials. Code obfuscation is a critical defense layer for any fintech app.
Key obfuscation techniques:
- Rename obfuscation — Replace variables, classes, and methods with random alphanumeric strings
- String encryption — Encrypt API keys, URLs, and UI text; decrypt only at runtime
- Code flow obfuscation — Add dead code and illogical jumps to confuse static analysis
- Resource encryption — Encrypt app resources like logos to prevent fake app creation
Obfuscation works at the static layer, but runtime integrity checks are equally important. Anti-tampering and anti-repackaging controls detect when an app has been modified or distributed through unofficial channels. Protectt.ai's CodeProtectt applies these protections at build time, transforming source code into unreadable logic while maintaining app performance — and runtime integrity checks reject server requests from modified APKs before they can cause damage.
Runtime and ongoing security
Static security measures leave a critical gap: once deployed, apps face live threats—jailbroken/rooted devices, screen overlay attacks, dynamic instrumentation tools, and in-session manipulation—that build-time security cannot catch.
Runtime Application Self-Protection (RASP)
RASP is a security mechanism that runs inside the app at runtime, detecting and responding to threats in real time without requiring server-side intervention. Unlike Web Application Firewalls (WAFs) that inspect network traffic externally, RASP validates data requests directly inside the app—what Gartner describes as residing "within a to-be-protected application's runtime environment."
Why RASP is critical for fintech:
Rooted and jailbroken devices are 250 times more likely to suffer total system compromise and 3.5 times more likely to be targeted with malware, according to Zimperium's 2025 data.
When a device is jailbroken, it gains root access—enabling unauthorized software installation, system file modifications, and direct access to app data that should remain protected.
RASP detects and blocks:
- Jailbreak/root detection — Identifies compromised devices and prevents app execution
- Emulator detection — Blocks apps running in cloud emulators used for automated fraud
- Dynamic instrumentation tools — Detects Frida, Xposed, and other hooking frameworks that attackers use to bypass security controls at runtime
- Screen overlay attacks — Prevents malicious apps from overlaying fake UI elements to steal credentials

Platforms like Protectt.ai's AppProtectt offer RASP with 100+ security features, including real-time threat detection, anti-tampering validation, and automated response mechanisms—delivering runtime protection without measurable latency impact.
Continuous monitoring and behavioral analytics
User behavior analytics (UBA) detect anomalous patterns that signal account compromise even when credentials are valid. Key indicators include:
- Unusual transaction amounts or velocity
- Login locations inconsistent with user history
- Rapid session changes or device switching
- Access from newly registered or suspicious devices
Detecting these signals early only matters if your incident response plan is ready to act. Financial industry organizations take an average of 168 days to identify and 51 days to contain a breach, according to IBM.
Fintech teams must detect, contain, and report incidents within regulatory timeframes—often 72 hours under GDPR Article 33. Real-time threat intelligence feeds are what make that window achievable.
Compliance, standards, and third-party risk management
Primary compliance frameworks for fintech apps in 2026 include:
PCI DSS v4.0.1 (published June 2024) mandates external penetration testing at least once every 12 months and after any significant infrastructure or application upgrade. Requirement 9.5.1 extends Point-of-Interaction (POI) protection to commercial off-the-shelf devices like smartphones and tablets used for mobile payments.
GDPR (Regulation EU 2016/679) requires breach notification within 72 hours and enforces data minimization principles. Violations carry fines up to €20 million or 4% of global annual turnover, whichever is higher.
India's RBI Authentication Mechanisms Directions 2025 mandate that all digital payment transactions use two-factor authentication with at least one dynamic factor—effective April 1, 2026. This directive explicitly deprecates static SMS OTPs.
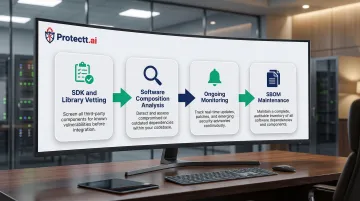
Meeting these regulatory thresholds is necessary — but regulatory compliance doesn't cover every attack surface. Supply chain vulnerabilities, compromised SDKs, and unpatched dependencies operate outside the compliance checklist entirely.
Managing third-party and supply chain risk requires:
- Vetting SDKs and libraries for known vulnerabilities
- Applying software composition analysis (SCA) tools to detect compromised dependencies
- Monitoring for updates or security advisories affecting third-party components
- Maintaining software bills of materials (SBOMs) for all dependencies
Schedule penetration testing and independent security audits at minimum annually and after every major release. Edgescan's 2025 data shows that 17.4% of critical and high-severity vulnerabilities remain unpatched after 12 months, with an average remediation time of 74.3 days — exposure gaps no fintech operation can afford.
Common security mistakes fintech teams make
With average remediation times exceeding 74 days, discovered vulnerabilities stay open long enough for automated scanners to find and exploit them. Teams that treat security as a pre-launch checklist — skipping post-launch monitoring or delaying patches — create exactly this kind of exposure. Security requires continuous practice, not a one-time sign-off.
A 2025 Guardsquare survey found that nearly 40% of organizations rely solely on OS-built-in security measures, while 60% have not implemented RASP. That's a significant gap, because sophisticated attacks are designed to bypass individual controls. MFA alone won't stop API exploits, and firewalls won't prevent on-device malware. Relying on a single layer isn't a security strategy — it's a bet that attackers won't notice.
Ignoring mobile-specific threats is common among teams with web-security backgrounds. Mobile environments face unique risks:
- Rooted/jailbroken devices with disabled security controls
- Repackaged apps distributed through unofficial channels
- Screen overlay attacks where malware overlays fake UI elements to steal credentials
- Clipboard data leakage exposing copied passwords or account numbers
- Accessibility abuse where malware mimics human behavior to bypass biometric controls
Banking trojans like BingoMod use screen overlay capabilities to bypass identity safeguards and initiate unauthorized transfers. Albiriox and Herodotus abuse Android accessibility features, randomizing keystroke intervals to defeat behavioral biometrics and silently drain accounts during live sessions. Teams without mobile-specific protections — UI safeguards, malicious keyboard detection, overlay blocking — have no visibility into these attacks until the damage is done.
Conclusion
Keeping a fintech app secure in 2026 means treating security as an ongoing operational discipline, not a project milestone. Authentication, encryption, runtime protection, compliance, and incident response all need to work together continuously. Attackers now use AI to automate exploits, hit APIs at scale, and manipulate apps at runtime — static, single-layer defenses can't keep up.
Before adding new controls, fintech teams should evaluate where their current posture falls short. Key gaps to check:
- Relying solely on OS-level protections without runtime coverage
- No RASP layer to detect and block in-app threats
- Missing behavioral monitoring for anomalies and API abuse
- Third-party SDKs that are unvetted or overdue for review
Platforms like Protectt.ai address this by unifying protection across the app, device, and transaction layers — covering RASP, code obfuscation, API security, and silent mobile verification in a single, lightweight SDK. For fintech organizations in banking, insurance, and payments, that kind of comprehensive coverage is what makes regulatory compliance achievable and user trust sustainable.
Frequently asked questions
What are common security issues in fintech apps?
The most prevalent issues include account takeover (ATO) through credential stuffing and SIM swap attacks, API vulnerabilities exposing sensitive endpoints, insecure data storage on devices, Man-in-the-Middle (MitM) attacks on unsecured networks, and reverse engineering of app code to extract business logic and cryptographic keys.
What are the security best practices and standards for fintech mobile apps?
Core best practices span authentication, data protection, and runtime defense:
- Authentication: MFA with biometric or device-bound factors
- Encryption: TLS 1.3 for transport, AES-256 for data at rest
- API security: Authentication, rate limiting, and input validation
- App hardening: Code obfuscation, anti-tampering, and RASP
- Compliance: PCI DSS, GDPR, and regional mandates like RBI's authentication directives
What is RASP and why do fintech apps need it?
Runtime Application Self-Protection (RASP) runs inside the app to detect and block threats in real time—protecting against jailbroken devices, dynamic instrumentation tools like Frida, screen overlay attacks, and in-session manipulation that static security cannot address. RASP is essential because rooted devices are 250 times more vulnerable to system compromise.
How often should a fintech app undergo security testing?
Penetration testing and security audits should occur at least annually, and after every major release, infrastructure change, or new third-party integration. PCI DSS v4.0.1 explicitly requires external penetration testing every 12 months and after significant upgrades.
How does PCI DSS compliance affect fintech app security requirements?
PCI DSS mandates controls covering cardholder data protection, access management, and vulnerability monitoring—including annual penetration testing and secure transmission via strong cryptography. Mobile apps handling payments also fall under POI device protection requirements. Non-compliance can result in fines and loss of payment processing rights.
What is the difference between app shielding and runtime protection?
App shielding applies protections at build time—code obfuscation, string encryption, and anti-tampering—making the compiled app difficult to reverse engineer. Runtime protection (RASP) monitors live execution, catching jailbroken devices, dynamic attacks, and in-session manipulation that build-time controls cannot detect.


