
Introduction
When an attacker already inside your network looks identical to a legitimate employee, perimeter defenses become irrelevant. Firewalls, VPNs, and implicit trust assumptions no longer stop breaches — they just delay detection.
The financial stakes are concrete: US data breach costs hit a record $10.22 million in 2025, while the global average stands at $4.44 million. For mobile-first Banking, FinTech, and Government sectors, these aren't just statistics — they're existential threats.
The answer is combining AI with Zero Trust architecture. Zero Trust enforces "never trust, always verify" at every access point; AI makes that enforcement continuous, context-aware, and fast enough to matter in mobile-first environments where no network perimeter exists.
This guide covers the five pillars of Zero Trust, how AI activates each one, real-world applications in banking and financial services, and a deployment roadmap for security leaders.
TLDR
- Zero Trust eliminates implicit trust—every user, device, and application must be continuously verified regardless of network location
- AI enables Zero Trust at scale through real-time anomaly detection, automated threat response, and adaptive identity verification
- All five Zero Trust pillars gain measurable capability through AI-driven automation across identity, devices, and data
- Mobile-first sectors benefit from AI-enhanced Zero Trust through app-level security, device binding, and behavioral analytics
- Implementation challenges—legacy integration, data privacy, algorithmic bias—are addressed through phased rollouts and continuous model auditing
Why traditional security is failing — and what zero trust changes
The fatal flaw of perimeter-based security
Perimeter-based security operates on a dangerous assumption: everything inside the network boundary is safe. This model collapses in modern environments characterized by cloud computing, remote work, and mobile-first operations. NIST explicitly warns that perimeter-based network security is insufficient, as once attackers breach the perimeter, lateral movement becomes trivial.
How attackers exploit implicit trust:
- Credential theft — Phishing and compromised credentials account for 16% of breaches
- Lateral movement — Attackers maintain an 11-day median dwell time before detection, navigating networks using valid credentials
- Insider threats — Malicious insider attacks cost an average of $4.92 million per breach
Zero trust: a fundamentally different model
Zero Trust architecture eliminates implicit trust entirely. NIST SP 800-207 defines Zero Trust as minimizing uncertainty in enforcing accurate, least-privilege access decisions in networks viewed as compromised. No asset or user account receives trust based solely on physical or network location.
The three core principles:
- Verify Explicitly — Authenticate and authorize based on device health, user role, location, and behavioral signals
- Apply Least Privilege — Limit access with Just-Enough-Access and Just-in-Time principles
- Assume Breach — Design systems to contain and respond to compromises automatically
Those three principles sound straightforward — but executing them continuously, across thousands of simultaneous access requests, is where human-only security teams hit a hard ceiling.
Why AI is essential for zero trust at scale
Zero Trust demands real-time evaluation of every access request, device state, and user behavior across an entire environment. Human analysts simply cannot operate at that speed or volume. AI closes that gap by automating the decisions Zero Trust depends on:
- Scoring each access request against live behavioral baselines
- Detecting anomalous lateral movement patterns before dwell time extends
- Enforcing least-privilege policies dynamically as context changes
- Flagging compromised credentials based on usage patterns, not just signatures
The 5 pillars of zero trust architecture
CISA's Zero Trust Maturity Model v2.0 defines five structural pillars that form the foundation of any Zero Trust implementation. Mature Zero Trust requires securing all five simultaneously:
- Identity — Who is requesting access, and are they who they claim to be?
- Devices — Is the device in a trusted, compliant state?
- Networks — Is the connection path segmented and verified?
- Applications and Workloads — Is access enforced at the application layer?
- Data — Is the data classified, governed, and protected at rest and in transit?

Identity: the new perimeter
Identity replaces network location as the primary security boundary. Every user, service account, and AI agent must be continuously verified through:
- Multi-factor authentication (MFA) — Preferably phishing-resistant methods
- Role-based access control (RBAC) — Permissions tied to job functions
- Just-in-Time (JIT) access — Temporary privilege elevation only when needed
AI enhances this pillar by analyzing behavioral context alongside credentials, detecting when legitimate credentials are used in suspicious patterns.
Devices: continuous posture assessment
Every device accessing resources must be assessed in real time for security posture:
- OS version and patch status
- Jailbreak or root detection
- Compliance with organizational policies
- Presence of malware or suspicious applications
This pillar is especially critical for mobile environments where device compromise represents a major threat vector. AI-driven device attestation continuously monitors for anomalies that signal compromise.
Networks: micro-segmentation
The Department of Defense Zero Trust Reference Architecture emphasizes micro-segmentation as critical for preventing lateral movement. Networks are divided into small zones so that even a compromised segment cannot lead to an organization-wide breach. Zero Trust never grants blanket network-level access—every connection is evaluated independently.
Applications and data: enforcement at every layer
Where network segmentation limits movement, application-layer controls determine what users and AI agents can actually do once they're in. CISA treats Applications and Workloads together with Data as a single unified pillar — because access without data governance is incomplete protection.
Applications must enforce their own controls rather than inheriting trust from the network. Data must be classified, labeled, and governed so protections follow the data wherever it moves. Key requirements at this layer include:
- Enforcing access policies within the application, independent of network location
- Classifying and labeling data by sensitivity before AI systems process it
- Applying encryption and data-loss prevention controls at the workload level
- Governing AI agent access to sensitive data with the same scrutiny as human users
How AI strengthens zero trust: core capabilities
AI-powered continuous verification and adaptive authentication
Traditional authentication is a single gate at login. AI transforms this into an ongoing process throughout the entire session, analyzing multi-dimensional signals:
- User behavior patterns (typing rhythm, navigation habits)
- Geolocation and travel patterns
- Device posture and security state
- Time and context of access
Adaptive authentication means low-risk actions pass with minimal friction while high-risk operations trigger step-up verification—improving both security and user experience.
Behavioral analytics and anomaly detection
User and Entity Behavior Analytics (UEBA) mines potential incidents that deviate from normal behavior patterns. AI establishes a behavioral baseline for each user and device, then continuously monitors for deviations:
- Unusual login times or geographic locations
- Abnormal data access volumes
- Atypical application usage patterns
- Suspicious privilege escalations
This embodies the "assume breach" principle: AI treats anomalies as potential compromises and triggers investigation before damage occurs. Organizations using AI and automation extensively shortened breach times by 80 days compared to those without these solutions.
AI-driven threat intelligence and predictive defense
Cutting breach detection time is only half the equation — stopping attacks before they land is the other. Rather than waiting for known threat signatures, AI analyzes historical patterns and live threat intelligence to predict where attacks are likely to originate. Predictive AI can:
- Flag users receiving escalated privileges without authorization
- Identify connections between suspicious activities across disparate systems
- Preempt zero-day attacks that signature-based tools would miss entirely
Automated incident response
The gap between threat detection and remediation drives breach costs. In 2025, the mean time to identify and contain a breach was 241 days. AI-powered automated response dramatically narrows this gap, reducing response time from hours to seconds.
Typical automated playbook:
- AI detects anomalous behavior
- System triggers step-up authentication
- If unresolved, isolates affected device or suspends access rights
- Alerts security team with full incident context

Organizations that extensively utilized security AI and automation lowered breach costs by $1.9 million, demonstrating the financial impact of automated containment.
Least privilege access at machine speed
AI dynamically adjusts permissions based on real-time risk context — Just-Enough-Access (JEA) in practice. AI replaces static role assignments with continuously recalculated access rights based on:
- User's current behavior patterns
- Device security posture
- Session context and risk indicators
- Business justification for access
This directly enforces Zero Trust's principle of minimizing the blast radius of any potential compromise.
AI-enhanced zero trust in high-stakes environments: mobile and financial services
The mobile security challenge
Mobile-first environments in Banking, FinTech, Insurance, and Government face unique Zero Trust challenges. Users authenticate through personal devices, transactions happen across untrusted networks, and the attack surface spans app, device, and network layers simultaneously.
UK fraud prevention service Cifas reported a 1,055% surge in unauthorized SIM swaps in 2024, with 48% of all account takeover cases involving mobile phone accounts. BioCatch reported mobile fraud attacks rose from 47% to 61% as fraudsters shifted to weaponized mobile emulators — a trajectory that shows no signs of reversing.
Regulatory mandates for app-layer security
Regulators recognize that traditional network security is insufficient for mobile environments. The US Office of Management and Budget (OMB M-22-09) explicitly mandates that "MFA must be enforced at the application layer, instead of the network layer" and requires phishing-resistant MFA.
The Reserve Bank of India's 2024 Master Directions require non-bank Payment System Operators to ensure mobile app integrity, secure authenticated sessions, and revalidate device binding.
Zero trust principles in mobile applications
For mobile-first environments, Zero Trust must extend beyond network controls:
- App-level enforcement — Security lives inside the application, not just the network
- Device binding — Continuous assessment of device security posture
- Transaction-level verification — Every transaction evaluated for behavioral risk before execution
CISA's 2025 Mobile Communications Best Practice Guidance explicitly warns highly targeted individuals: "Do not use a personal virtual private network (VPN). Personal VPNs simply shift residual risks... often increasing the attack surface." VPNs provide network access without contextual awareness of the mobile device's posture or the application's runtime integrity.
Runtime Application Self-Protection (RASP)
RASP is an application-level security tool that operates from within the application's runtime environment to monitor behavior and context, controlling execution and preventing real-time attacks without human intervention. The OWASP AppSensor project provides frameworks for application-layer intrusion detection and automated response.
RASP vs. Traditional Security Controls:
| Feature | WAF | EDR | RASP |
|---|---|---|---|
| Location | Network perimeter | OS/Device level | Inside app runtime |
| Primary Focus | Filter HTTP traffic | Detect malware | Block in-app tampering |
| Context Awareness | Low | Medium | High |
| Mobile Suitability | Poor | Poor | Excellent |
RASP is the only control that travels with the application, ensuring Zero Trust principles are enforced directly on the endpoint regardless of network security.
Protectt.ai: full-stack zero trust for mobile
Platforms like Protectt.ai embed comprehensive Zero Trust capabilities through a lightweight SDK, providing:
- Runtime protection — Over 100 security features detect and block attacks in real time
- Device security — Jailbreak/root detection, device binding, SIM verification
- Silent network-based identity verification — Eliminates OTP friction by verifying identity directly through carrier networks, without routing traffic through the app
- AI-driven behavioral analytics — Detects account takeover attempts through anomalous patterns
- Zero performance overhead — The SDK runs security checks asynchronously, so protection adds no measurable latency to app response times

The result is continuous trust evaluation at every layer — app, device, and transaction — without the latency or user friction that typically accompanies layered security controls.
Challenges and best practices for implementing AI-driven zero trust
Common implementation challenges
Three obstacles consistently slow AI-driven Zero Trust deployments:
Legacy infrastructure incompatibility tops the list. A 2025 GAO report found that many federal legacy systems cannot support Zero Trust without full modernization — they lack multi-factor authentication and encryption at the protocol level. Middleware layers, APIs, and phased migration plans are non-negotiable starting points.
Data privacy and algorithmic bias create compliance friction. AI systems monitoring user behavior at scale must satisfy GDPR, HIPAA, and sector-specific regulations. GDPR mandates Data Protection Impact Assessments for any systematic profiling. The NIST AI Risk Management Framework also warns that bias embedded in training data can produce discriminatory access decisions — diverse datasets are required, not optional.
Alert fatigue undermines even well-designed systems. Security teams overwhelmed with false positives become desensitized, making them less likely to catch genuine threats. AI models need ongoing tuning to keep noise low and signal high.
These challenges don't make AI-driven Zero Trust unworkable — they make a staged deployment approach essential.
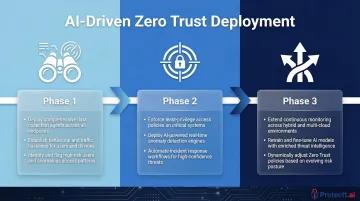
Phased implementation approach
Start with high-value assets and high-risk users, then expand. Attempting enterprise-wide rollout simultaneously is how deployments stall.
Phase 1 — Establish Visibility
- Deploy telemetry (behavioral and event data) collection across identity and device layers
- Establish baseline activity patterns for users and endpoints
- Flag high-risk users and map critical applications
Phase 2 — Apply Zero Trust to Critical Assets
- Enforce Zero Trust policies on sensitive data and applications first
- Deploy AI-driven anomaly detection against established baselines
- Automate response for high-confidence threat signals
Phase 3 — Scale Across the Environment
- Extend AI-driven monitoring to all users and devices
- Retrain AI models regularly against current threat intelligence feeds
- Adjust policies based on operational feedback and false positive rates
Resource allocation guidance
Budget not just for technology licenses but for:
- Data quality improvements — AI model accuracy depends on clean, comprehensive telemetry
- Staff training — Security teams must understand AI-driven decisions to act on them effectively
- Continuous evaluation cycles — AI effectiveness depends on regular model updates and tuning
Teams that treat telemetry as an afterthought tend to discover their blind spots during incidents rather than before them.
Frequently asked questions
What is the Zero Trust approach to AI?
Zero Trust applied to AI means treating AI agents, models, and workloads with the same "never trust, always verify" scrutiny as users and devices. This includes continuously validating AI identities, restricting access to only what's needed, and designing systems resilient to manipulation like prompt injection or data poisoning.
How does the Zero Trust model enhance the security of an organization's systems and data?
Zero Trust eliminates implicit trust, meaning every access request is verified regardless of network location. This reduces lateral movement risk after a breach, enforces least-privilege access to limit blast radius, and ensures continuous monitoring of all activity to detect and contain threats before they escalate.
What are the main components of AI architecture and how to secure it?
Key components include data pipelines, model training infrastructure, inference endpoints, and agent/plugin integrations. Securing each layer requires Zero Trust access controls on data and models, continuous behavioral monitoring, and defenses against adversarial inputs like prompt injection and data poisoning.
What are the 5 pillars of zero trust architecture?
The five pillars are Identity, Devices, Networks, Applications, and Data. Each pillar carries its own verification and access control policies — together, they eliminate implicit trust at every layer of the architecture.
What are the biggest challenges in implementing AI-driven Zero Trust security?
The top challenges are integrating AI-driven Zero Trust controls with legacy infrastructure, ensuring AI models are trained on diverse and accurate data to avoid bias and false positives, and maintaining data privacy compliance while collecting the behavioral telemetry that AI models need to function effectively.
How does AI-enhanced Zero Trust security protect mobile applications?
AI-enhanced Zero Trust in mobile security operates through Runtime Application Self-Protection (RASP), device posture assessment, behavioral analytics, and silent network-based identity verification. Together, these layers enable continuous trust evaluation across device, app, and transaction contexts — without requiring OTPs or manual re-authentication steps.


