
Introduction
Mobile apps now handle everything from banking transfers and insurance claims to investment portfolios and digital wallets—making them prime targets for organized fraudsters. Mobile app fraud encompasses any malicious activity that exploits a mobile application to steal data, funds, or user identities, ranging from credential stuffing and device-level attacks to app tampering and SIM swapping.
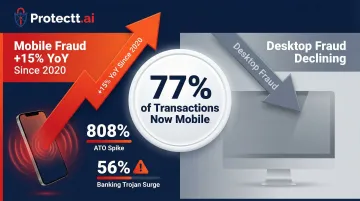
Fintech apps experienced an 808% year-over-year spike in Account Takeover (ATO) attacks in 2024, while mobile banking Trojan attacks surged 56% in 2025, reaching 255,090 unique malicious packages. With 77% of financial transactions now originating from mobile devices, the mobile channel has become the primary battleground for digital fraud.
This guide covers the most dangerous fraud types targeting mobile apps, their root causes, early warning signs, and the layered prevention strategies every mobile-first business needs to protect users, secure transactions, and defend brand trust.
TL;DR
- Mobile app fraud includes account takeovers, device-level attacks, app tampering, SIM swapping, and in-app malware targeting users and businesses
- Attackers exploit weak authentication, unprotected app code, compromised devices, and social engineering to access accounts and transactions
- Direct financial losses, regulatory penalties, and reputational damage follow unchecked fraud—especially in banking, fintech, and insurance
- Effective prevention combines runtime app protection, multi-factor authentication, device integrity checks, and AI-driven behavioral analytics
- Teams that monitor for impossible logins and abnormal transaction velocity catch fraud before significant damage occurs
What is mobile app fraud? Common types and root causes
Mobile app fraud covers any fraudulent activity targeting or carried out through a mobile application: attacks on the app itself, the device it runs on, and the user behind it. It arises from weak app security, insufficient authentication, and attackers deliberately probing the mobile channel as it handles increasingly high-value transactions.
Mobile fraud has increased 15% year-over-year since 2020, while desktop fraud has declined. As transaction volumes shift mobile, attackers follow, automating attacks at massive scale using fraud-as-a-service tools available for as little as $150 per month.
Account takeover (ATO)
Akamai tracked 113 billion active attack sessions in 2024, a 63% year-over-year increase — the majority targeting mobile APIs. The method driving that volume: credential stuffing, where bots test stolen username-password combinations against mobile login endpoints until something breaks.
Poor password hygiene and data breach dumps fuel these attacks. A banking app login from an unrecognized device after a phishing campaign, or a fintech wallet accessed using credentials bought off a dark web marketplace — these are the everyday realities of ATO at scale.
Device-level attacks: rooted, jailbroken, and emulated devices
Attackers use rooted Android or jailbroken iOS devices (and software emulators) to bypass app security controls, intercept data, and manipulate app behavior in ways standard devices would prevent. Rooted devices face more than 3.5 times higher malware risk compared to stock devices, with filesystem compromise incidents spiking by a factor of 3,000.
Emulator farms automate fraudulent actions at scale, especially fake registrations and transaction manipulation. Criminal syndicates run hundreds of parallel mobile onboarding sessions from desktop infrastructure, injecting pre-recorded or deepfake videos directly into biometric SDKs to bypass liveness checks.
App tampering and reverse engineering
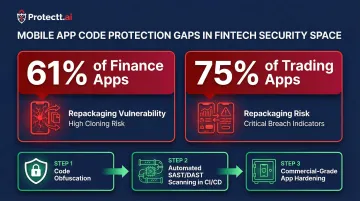
Promon testing found 61% of top finance apps could be successfully repackaged, and 60% of iOS apps lack basic code protection. Those gaps give fraudsters an opening to decompile apps, extract API keys, inject malicious code, or build counterfeit versions distributed through unofficial channels.
Repackaged fake apps that mimic legitimate banking or payment apps steal credentials and damage brand reputation. Nearly 1 in 5 apps contain hardcoded encryption keys that attackers can extract through reverse engineering.
SIM swapping and phone number hijacking
Attackers convince telecom operators to transfer a victim's number to a new SIM, then intercept OTPs to bypass MFA entirely. Europol's "Operation SIMCARTEL" dismantled a single SIM-box network operating 40,000 SIM cards that had enabled 49 million fake accounts — one operation, one network.
The FBI reported $25.9 million in SIM swap losses in 2024 across just 982 complaints. What makes it effective: SMS OTPs treat phone number possession as proof of identity, which breaks the moment the number is no longer yours.
Overlay attacks and in-app malware
Kaspersky detected a 56% increase in Trojan banker attacks in 2025, reaching 255,090 unique installation packages. The attack works by drawing transparent overlays on top of legitimate banking apps, capturing credentials and payment details while the user interacts with what looks like their normal app.
Attackers trick users into granting Android Accessibility permissions, giving malware full control over the device UI. Keyloggers and screen-capture malware operate at the device layer, targeting mobile app sessions even after successful authentication.

The hidden cost of mobile app fraud
The financial impact of mobile fraud extends far beyond stolen funds, encompassing operational drain, regulatory fines, and customer abandonment. Businesses absorb fraud losses, chargebacks, and reimbursement obligations—with mobile fraud losses increasing 52% in 2022 while desktop fraud losses dropped 16%.
Regulatory exposure compounds the financial hit. The French privacy regulator fined Free Mobile and Free a combined €42 million for a 2024 data breach exposing 24 million users' personal data, citing failures to implement basic security measures. Violations of PCI DSS, GDPR, and sector-specific mandates result in heavy fines and mandatory audits when fraud incidents reveal security gaps.
The user trust damage is equally measurable. 43% of consumers would stop using a site or app if their accounts were compromised by ATO, and 67% of customers would consider switching banks after a serious breach. For banks and fintechs, a single high-profile breach permanently erodes user trust and damages app store ratings.
These costs are preventable — but only if you catch the signals early.
Warning signs your app is being targeted
Anomalous authentication activity provides early indicators of credential-based attacks:
- Multiple failed login attempts from the same device or IP
- Logins from new or impossible geographic locations
- Sudden spikes in password reset requests
- Authentication attempts at unusual hours
Unusual transaction patterns signal potential fraud in progress:
- Abnormally high transaction velocity compared to user baseline
- Transfers to new or unverified recipients
- Small test transactions followed immediately by large transfers
- Rapid changes in transaction amounts or frequencies
App integrity signals indicate attackers are probing or interacting with the app outside normal use:
- Increased crash reports from specific device types
- Unexpected API call patterns from non-standard devices
- Detection of running on emulators or rooted environments
- Unusual device fingerprint combinations
How to prevent mobile app fraud
Effective prevention requires a multi-layered strategy—no single control stops all fraud. The most robust defense combines app-layer protection, device intelligence, identity verification, and continuous monitoring working together.
Implement Runtime Application Self-Protection (RASP)
RASP embeds security controls directly into the app binary, enabling it to detect and respond to attacks in real time (including tampering, hooking, debugging, and emulated environment detection) without relying on perimeter defenses alone.
Key RASP capabilities include:
- Real-time detection of app tampering and unauthorized modifications
- Blocking of runtime hooking attacks that manipulate business logic
- Prevention of debugging attempts and code injection
- Identification of emulator and rooted/jailbroken device environments
- Automated protective actions: session termination, blocking, or alerting

Solutions like Protectt.ai's RASP SDK with 100+ security features allow apps to detect threats at runtime and take automated protective actions with zero performance overhead. Embedding RASP during development — rather than bolting on security post-launch — ensures the app is hardened before it reaches any distribution channel, legitimate or otherwise.
Enforce multi-factor authentication and zero trust
MFA beyond OTP creates stronger identity assurance. Biometric authentication, device binding, and behavioral factors provide layered verification that's harder to compromise. OTP alone is vulnerable to SIM swap attacks — network-based silent verification alternatives eliminate this risk by validating identity directly through carrier networks.
Zero Trust applied to mobile means every session, device, and transaction is treated as untrusted until verified. This limits the blast radius of any credential compromise by requiring continuous validation — not just a one-time check at login.
A practical MFA stack for mobile apps includes:
- Biometric verification (fingerprint or face recognition)
- Device binding tied to a specific device fingerprint
- Silent network-based identity verification via carrier
- Behavioral signals (typing rhythm, interaction patterns) as passive factors
Detect and block compromised devices
Device integrity checks should detect rooted/jailbroken devices, emulators, VPN/proxy abuse, and device spoofing at the point of access. When risk is detected, apps should either block access entirely or apply step-up verification before allowing sensitive operations.
Device binding — linking an account to a specific device fingerprint — immediately flags any login attempt from an unrecognized device. This creates a powerful signal for fraud detection, as legitimate users typically access accounts from a small set of known devices.
Apply code obfuscation and app hardening
Code obfuscation makes it significantly more difficult for attackers to reverse-engineer the app, find vulnerabilities, or repackage it as a fake. String encryption and control flow obfuscation are core techniques that should be applied before every release as part of the CI/CD pipeline, not as a one-time step.
61% of finance apps and 75% of trading apps could be successfully repackaged due to missing code protection. Automated SAST/DAST scanning in CI/CD catches hardcoded secrets before release, while commercial-grade obfuscation protects against cloning on unofficial app stores.
Deploy AI-driven behavioral analytics and threat intelligence
AI/ML models build a behavioral baseline for each user — normal login times, transaction patterns, device usage — and flag deviations in real time as potential fraud signals. These models analyze typing patterns, touchscreen gestures, session duration, and navigation timing to create unique behavioral profiles.
Continuous threat intelligence feeds allow security teams to adapt defenses as new attack patterns emerge, rather than waiting for the next incident. Platforms with embedded AI like Protectt.ai monitor billions of mobile sessions globally, providing massive scale for training and validating behavioral models that detect fraud while minimizing false positives.
Long-term mobile app fraud prevention strategies
Continuous monitoring and real-time alerting form the foundation of proactive defense. Implement 24/7 monitoring of app telemetry, device signals, and transaction anomalies — then configure automated alerts so security teams can respond before fraud escalates. Key signals to track include:
- Failed authentication attempts and repeated credential stuffing patterns
- Unusual device fingerprints or new device registrations
- Abnormal transaction velocity or value spikes
Monitoring catches active threats, but periodic audits catch structural weaknesses before attackers find them. Schedule third-party penetration tests focused on mobile-specific attack surfaces: API security, authentication flows, and local data storage. PCI DSS Requirements 11.3.1 and 11.3.2 mandate pen testing at least annually and after any significant infrastructure change. Use findings to prioritize and track iterative security improvements.
The third pillar extends your defense perimeter to the users themselves. Embed in-app guidance that alerts users to suspicious account activity, explains phishing and SIM swap risks in plain language, and provides a direct path to report concerns. Push notifications for unrecognized device logins or unusual transactions give users the context they need to act fast — before a fraud attempt succeeds.
Conclusion
Mobile app fraud has identifiable, preventable causes—from weak app code and device vulnerabilities to social engineering—and businesses serving mobile-first users cannot afford a reactive posture. The shift of 77% of transactions to mobile devices has created an expanded attack surface that traditional perimeter defenses cannot protect.
Layered, proactive defenses are what stop fraud before it reaches users or your financials. Organizations that build these controls into their mobile stack can detect and respond to threats in real time:
- Implement RASP to block runtime attacks without relying on external detection
- Eliminate SMS OTP dependencies in favor of silent, carrier-verified authentication
- Enforce device integrity checks to catch rooted, emulated, or compromised environments
- Deploy behavioral analytics to surface anomalies before fraud completes
Done together, these measures protect customer trust and satisfy regulatory compliance requirements—ahead of the fraud techniques targeting mobile-first users today.
Frequently asked questions
How to prevent app fraud?
Preventing app fraud requires a layered approach: runtime application self-protection (RASP) to detect tampering and attacks, multi-factor authentication beyond SMS OTP, device integrity checks to block compromised devices, and continuous behavioral monitoring to identify anomalies.
Can someone hack my mobile banking app?
Yes, banking apps can be targeted through account takeover, overlay attacks, and reverse engineering. Properly hardened apps with RASP, code obfuscation, and real-time monitoring make successful attacks much harder by detecting threats at runtime and blocking malicious activity.
Can a scammer access my bank account with my phone number?
SIM swapping allows fraudsters to hijack a phone number to intercept OTPs and bypass MFA, enabling account access. Banks should deploy network-based silent verification or device binding as more secure alternatives to SMS OTP, eliminating reliance on telecom security.
What app will protect my phone from hackers?
Protection comes primarily from security built into apps by developers—RASP, encryption, secure authentication—rather than a separate consumer app. Users should look for apps from providers with visible security certifications, regular updates, and transparent security practices.
What is the most common type of mobile app fraud?
Account takeover (ATO) is the most prevalent type, driven by credential stuffing, phishing, and SIM swapping. It's particularly damaging in banking and fintech because it directly leads to unauthorized transactions, with fintech ATO attacks surging 808% year-over-year as attackers automate credential testing at scale.
How do I know if my mobile app has been compromised?
Key indicators include unexpected account activity, logins from unknown devices or impossible locations, app crashes on specific device types, or user complaints about unauthorized transactions. Real-time monitoring tools can detect these signals automatically before users notice, enabling immediate response to contain threats.


