
Introduction
The global digital payments industry generated $2.5 trillion in revenue from $2.0 quadrillion in value flows across 3.6 trillion transactions in 2024, with McKinsey projecting revenue growth to reach $3.0 trillion by 2029. Yet this explosive growth has created a parallel surge in financial crime exposure. Consumers lost $12.5 billion to fraud in 2024 in the US alone—a 25% increase from the previous year—while European payment fraud reached €4.2 billion and UK criminals stole £1.17 billion through unauthorised and authorised fraud.
Digital payment providers face a real tension: delivering fast, frictionless experiences while building defenses that satisfy regulators, protect customers, and preserve brand trust. The shift to real-time payment rails has compressed fraud detection windows from days to milliseconds, making legacy rule-based systems structurally inadequate.
Criminals now exploit the same features that make digital payments valuable—speed, accessibility, and low friction—to run fraud operations at scale. This guide examines the key financial crime risks in digital payments and how providers can build effective, layered defenses without sacrificing user experience.
TLDR
- Real-time payments compress fraud detection windows to milliseconds, making batch processing and manual review ineffective
- Synthetic identity fraud accounts for 80% of new account fraud, costing the US economy $30–35 billion annually
- Mobile channels are the primary attack vector — RASP at the app layer is the frontline defense
- AI/ML models and behavioral biometrics enable real-time anomaly detection that adapts to evolving threats
- Shared liability mandates now require receiving institutions to actively detect money mule accounts
Why digital payments create elevated financial crime risk
Speed and accessibility enable scalable attacks
The core benefits of digital payments—instant settlement, 24/7 availability, and minimal user friction—are precisely the properties criminals exploit. Unlike physical bank robbery requiring presence and resources, digital attacks can target thousands of accounts simultaneously from anywhere in the world. In the UK, 96% of fraudulent Authorised Push Payment scams utilized Faster Payments, confirming that real-time rails eliminate the settlement delays that once allowed fraud detection.
In India, UPI fraud surged 85% year-over-year to 13.42 lakh cases amounting to Rs 1,087 crore in FY 2023-24. The millisecond detection window for real-time payments makes traditional batch-processing systems obsolete—by the time alerts trigger, funds have already moved.
Mobile-first channels concentrate risk
Mobile banking has become the primary channel for remote financial interactions, making it the highest-value target. While UK mobile banking fraud cases decreased 9% in 2024, financial losses increased 3% to £46.7 million, indicating criminals are shifting toward higher-value targeted attacks rather than volume-based schemes.
The mobile channel is uniquely vulnerable because device trust is often assumed after initial authentication. Criminals exploit this assumption through attacks that bypass traditional perimeter defenses by compromising the endpoint device itself:
- Account takeover (ATO) — credential theft targeting authenticated sessions
- Malicious overlays — fake UI layers that intercept credentials in real time
- Screen mirroring — remote viewing of live device activity without user awareness
- SIM swapping — hijacking phone numbers to intercept OTPs and authentication codes

Jurisdictional fragmentation creates blind spots
Digital payments often operate across borders and through non-bank intermediaries—FinTechs, payment aggregators, and digital wallet providers—creating supervisory gaps criminals deliberately exploit. 71% of card fraud using EU/EEA-issued cards in H1 2023 was cross-border, a direct consequence of fragmented oversight across regulatory boundaries.
The Financial Action Task Force notes that as payment chains grow more complex, it becomes harder for institutions to identify suspicious activity and comply with sanctions—a gap criminals exploit through layered transactions across multiple jurisdictions and non-bank providers.
Common financial crime typologies in digital payments
Identity theft and account takeover (ATO)
Criminals steal user credentials through data breaches, phishing, malware, or SIM swapping, then use stolen identities to initiate unauthorized transactions. The FBI's IC3 received over 5,100 ATO complaints since January 2025, with losses exceeding $262 million.
ATO is particularly dangerous on mobile, where device trust is assumed post-authentication. Once inside, attackers can drain accounts, initiate wire transfers, or establish money mule networks—all while appearing as legitimate users to transaction monitoring systems.
Synthetic identity fraud
Fraudsters combine real and fabricated personal data to create entirely new identities that pass standard KYC checks. Synthetic identity fraud accounts for up to 80% of new account fraud, costing the US economy $30–35 billion annually. Generative AI has industrialized this process, enabling criminals to produce deepfakes and AI-generated personas at scale.
These synthetic identities build credit profiles over time before executing "bust-out" fraud—maxing out credit lines and disappearing. Behavior appears entirely legitimate for months, making detection difficult until the final extraction phase.
Authorized Push Payment (APP) fraud
APP fraud manipulates victims into authorizing payments themselves through impersonation scams, fake investment schemes, and romance fraud. In 2024, APP fraud cost the UK £450.7 million, with 70% of cases originating online via social media and search engines rather than compromised banking systems.
Because victims authorize transactions themselves, these payments are indistinguishable from legitimate ones at the transaction layer alone. Detection requires behavioral analysis, velocity checks, and cross-institutional intelligence sharing to identify receiving accounts controlled by criminals.
Money mule networks and micro-structuring
Criminal networks recruit or coerce intermediaries to move illicit funds across multiple accounts and platforms. Europol's EMMA 8 operation identified 8,755 money mules and 222 recruiters, leading to 2,469 arrests worldwide.
Micro-structuring splits large amounts into smaller transactions designed to evade AML detection thresholds. The pattern follows classic money laundering stages:
- Placement: Illicit funds enter the payment system through mule accounts
- Layering: Funds move across multiple accounts, platforms, and jurisdictions to obscure origin
- Integration: "Clean" funds re-enter the legitimate economy

Merchant fraud and refund abuse
Criminals exploit digital payment platforms by acting as both merchant and customer in P2M schemes, or systematically abuse refund and chargeback mechanisms. Global card-not-present (CNP) fraud losses are estimated to reach $28.1 billion by 2026—a 40% increase from 2023.
Unlike external attacks, these schemes are initiated from within trusted merchant relationships, making them harder to flag through standard fraud rules and placing the detection burden on behavioral pattern analysis.
Key strategies for managing financial crime risk
Shift from check-the-box to outcomes-based compliance
Rule-based, periodic compliance reviews are insufficient in real-time payment environments. The FATF explicitly expects institutions to implement AML/CFT measures through a risk-based approach, enabling appropriate services for low-risk scenarios and enhanced measures for high-risk situations.
Outcomes-based compliance prioritizes data-driven, continuous monitoring where detected crimes, false positive rates, and risk coverage drive program priorities—not just satisfying regulatory checklists. This approach focuses resources where risks are highest while maintaining financial inclusion for low-risk customers.
Implement Perpetual KYC (P-KYC)
Traditional periodic customer due diligence reviews are being replaced by continuous, real-time customer risk profiling. P-KYC maintains accurate client data through updates based on behavioral changes and circumstances in near real-time, rather than cycles of periodic remediation.
Benefits of P-KYC:
- Instant flagging of risk profile changes (sudden transaction behavior shifts, new device usage, geographic anomalies)
- Improved data quality through automated validation processes
- Reduced operational costs by eliminating manual periodic reviews
- Real-time detection of account takeover and synthetic identity bust-outs
With continuous profiling in place, the next layer of defense shifts to controlling how customers authenticate—where friction is applied and when it can be safely skipped.
Strong Customer Authentication (SCA) and risk-based exemptions
Multi-factor authentication combining something the user knows (password), has (device/token), and is (biometrics) is a proven baseline against unauthorized transactions. The EBA and ECB reported that EEA payment fraud stabilized at 0.002% of transaction value in 2024, largely due to successful SCA enforcement under PSD2.
Risk-based SCA exemptions preserve customer experience by applying friction only to high-risk transactions. Low-risk interactions proceed seamlessly while security effort concentrates where it matters most. Notably, card payment fraud was 17 times higher when recipients were outside the EEA where SCA isn't required—a clear signal that authentication controls work.
India's RBI has mandated two-factor authentication for all digital payment transactions by April 2026, requiring at least one dynamic factor for non-card-present transactions. This reflects a broader regulatory consensus that authentication remains the most effective fraud prevention control available.
Invest in next-generation financial crime detection
Rather than scaling human review teams to manage alert volumes (many false positives), organizations should invest in AI/ML models that identify high-confidence fraud signals, adapt to new attack patterns, and operate at transaction speed.
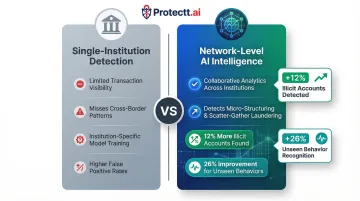
BIS Project Hertha demonstrated that collaborative payment system analytics helped banks and PSPs find 12% more illicit accounts than they would otherwise have found, with a 26% improvement for spotting previously unseen behaviors.
Network-level intelligence surpasses institution-specific models precisely because it can detect complex cross-border micro-structuring and scatter-gather laundering schemes that no single institution sees in full.
Cross-institutional intelligence sharing
Financial crime patterns detected by one institution benefit the entire ecosystem when shared via network intelligence frameworks. In the UK, the Joint Money Laundering Intelligence Taskforce (JMLIT+) supported investigations that generated over 1,430 new accounts associated with criminality and over £41.7 million restrained, seized, or filed for civil recovery in 2023/24.
In the US, FinCEN Exchange serves as a voluntary public-private information sharing partnership to enhance coordination and feedback in fighting financial crimes. These frameworks deliver measurable benefits across the ecosystem:
- Earlier detection of emerging threat patterns before they scale
- Lower compliance costs distributed across member organizations
- Broader regulatory visibility into systemic risks
The role of technology in financial crime prevention
AI and machine learning for real-time detection
ML models trained on behavioral data, transaction metadata, and network patterns detect anomalous activity in milliseconds—far beyond static rule capabilities. 58% of finance functions are using AI in 2024, a rise of 21 percentage points from 2023, reflecting rapid adoption.
Adaptive models continuously retrain as new fraud typologies emerge, minimizing false positives that degrade customer experience. Speed is the core advantage here: real-time scoring enables intervention before funds leave the institution, rather than discovering fraud during post-transaction reconciliation.
Mobile app security as the critical defense layer
Since the majority of digital payment fraud originates at or exploits the mobile layer—through compromised apps, malicious overlays, rooted/jailbroken devices, or SIM swapping—securing the mobile application itself is non-negotiable.
Runtime Application Self-Protection (RASP) detects and neutralizes threats in real time from within the app, making it resilient even on compromised devices. RASP operates at the application layer, providing continuous protection against:
- Malicious overlays and screen mirroring that capture credentials and OTPs
- Runtime hooking and code manipulation attempts
- Debugging and reverse engineering attacks
- Man-in-the-Middle (MITM) interception
- App spoofing and repackaging
Protectt.ai is built specifically for banking, FinTech, and payments environments, combining RASP with 100+ security features across device, network, and application layers. The platform maintains compliance with RBI Digital Payment Security Control Guidelines and PCI DSS standards, with zero-friction SDK integration for iOS and Android.

Device binding, behavioral biometrics, and zero-trust identity verification
Binding a user's identity to a specific trusted device using SIM binding and device fingerprinting creates persistent authentication that survives credential compromise. When combined with behavioral biometrics—typing patterns, navigation behavior, session anomalies—the system creates continuous authentication that catches fraudsters who have bypassed initial login.
Traditional authentication validates identity at login; behavioral biometrics validate identity throughout the session. This catches account takeover attacks where criminals use stolen credentials but exhibit behavioral patterns inconsistent with the legitimate user.
Zero-trust architecture assumes no device or user is inherently trustworthy, requiring continuous verification regardless of network location or previous authentication. For mobile payments—where users operate across unmanaged networks and potentially compromised devices—this is the only viable posture.
Automated compliance reporting and audit readiness
Automation reduces the manual burden of regulatory compliance, converting weeks of audit preparation into near-instant report generation. Regulated firms could save up to $183 billion annually in compliance costs through AI-driven systems, while global economies could recover more than $3.3 trillion each year by reducing illicit flows.
Automated compliance ensures controls are consistently applied—without relying on manual oversight—through executive dashboards, automated audit trails, and customizable reporting. The result is real-time regulatory visibility that keeps pace with examiner expectations, not just annual audit cycles.
Frequently asked questions
What is fraud in digital payments and what are some examples?
Digital payment fraud refers to any unauthorized or deceptive use of digital payment systems to obtain money or assets illegally. Common examples include identity theft-driven fund transfers, account takeover via phishing where criminals drain accounts after stealing credentials, and Authorized Push Payment fraud where victims are manipulated into authorizing payments to criminal-controlled accounts.
What are common types of fraud in digital payments?
The most prevalent types include account takeover (ATO) where criminals hijack legitimate accounts, synthetic identity fraud using fabricated personas, Authorized Push Payment (APP) fraud through social engineering, money mule schemes that layer illicit funds across accounts, micro-structuring to evade AML thresholds, and merchant/refund abuse exploiting chargeback mechanisms.
What is the difference between fraud and money laundering in digital payments?
Fraud involves obtaining money through deception or theft, generating illicit proceeds. Money laundering then disguises those origins through placement, layering, and integration, making stolen funds appear legitimate. In digital payments, criminals use fraud to steal funds and money laundering to clean them afterward through mule networks and micro-structuring.
How does AI help in detecting financial crime in digital payments?
AI/ML analyzes high-velocity transaction data in real time to identify anomalous patterns indicating fraud or money laundering, operating far faster than rule-based systems. Machine learning models continuously adapt to new criminal tactics, reducing false positives while improving detection rates for emerging fraud and laundering schemes.
What is Perpetual KYC (P-KYC) and why does it matter?
P-KYC replaces periodic customer reviews with continuous, real-time monitoring of customer behavior and risk profiles. Financial institutions can detect risk changes, such as sudden transaction spikes or new device usage, the moment they occur rather than months later during scheduled reviews, significantly narrowing exposure windows.
How can financial institutions balance strong security with frictionless user experience in digital payments?
Risk-based authentication applies stronger verification only to high-risk transactions while granting seamless access to low-risk ones. Technologies like behavioral biometrics, silent mobile verification, and device binding deliver strong security without visible friction, concentrating protection precisely where threats are highest.


