Introduction
Financial services teams building banking apps face converging regulatory pressure from three directions at once. If your app serves European users, GDPR enforcement can reach €1.2 billion in fines for data transfer failures. If it touches any health data, HIPAA's Business Associate liability exposes your development team directly. And if you serve Indian users, the RBI's Digital Payment Security Controls can halt customer onboarding entirely—as Paytm learned when regulators imposed an operational ban alongside a ₹5.39 crore penalty for cybersecurity lapses.
This guide breaks down what GDPR, HIPAA, and RBI standards each require of mobile apps, where they overlap, and how security teams can implement controls that satisfy all three without building three separate compliance programs. It's written for CTOs, compliance officers, and product security leads at banking, FinTech, insurance, and NBFC organizations operating across multiple regulatory jurisdictions.
TLDR:
- GDPR fines reach €1.2B, HIPAA exposes developers directly, and RBI can freeze new customer onboarding
- All three frameworks require encryption, MFA, audit logging, and vendor risk management—but diverge on data retention and consent
- Runtime Application Self-Protection (RASP) satisfies anti-tampering requirements across all three frameworks
- Automated compliance reduces audit preparation by 90% versus manual processes
Why mobile app compliance failures are costly—and increasingly likely
Regulators have shifted from financial penalties to operational paralysis. In March 2022, the RBI barred Paytm Payments Bank from onboarding new customers due to material supervisory concerns, followed by a ₹5.39 crore fine for KYC lapses and delayed cybersecurity incident reporting. Under GDPR Article 58, supervisory authorities can order processing restrictions that effectively force app store delistings.
The financial penalties compound that operational risk. Meta received a €1.2 billion fine from Ireland's Data Protection Commission for unlawful data transfers to the US. The Dutch DPA imposed €290 million on Uber for transferring European drivers' data without adequate protection. In the mobile app sector specifically, Norway's DPA fined Grindr NOK 65 million for unlawfully sharing user behavioral data with third-party advertising SDKs without valid consent.
Multi-jurisdiction exposure makes this harder to contain. A single Indian FinTech app may simultaneously need to satisfy RBI's DPSC, GDPR for European users, and HIPAA for wellness or insurance data. Most teams treat these as separate workstreams—creating compliance gaps and redundant effort in the process.
Legal liability extends beyond the organization itself:
- Individual developers and officers face direct liability under HIPAA's Omnibus Rule
- The HHS OCR settlement with MMG Fusion ($10,000 penalty plus a 3-year Corrective Action Plan) confirms tech vendors cannot shelter behind Covered Entities
- Under 42 U.S.C. 1320d-6, directors and employees face criminal penalties for knowingly obtaining or disclosing individually identifiable health information
Understanding each regulation: what GDPR, HIPAA, and RBI actually require of mobile apps
GDPR and mobile apps
GDPR Article 3 applies to any app that collects or processes personal data of EU/EEA residents, regardless of where the company is headquartered. This includes login data, device identifiers (Apple's IDFA, Google's AAID), behavioral analytics, and location data. The EDPB Guidelines 3/2018 confirm this applies to mobile apps intentionally targeting EU individuals.
Core GDPR obligations for mobile apps:
- Lawful basis for data collection with explicit, granular consent flows
- No pre-checked boxes — EDPB Guidelines 05/2020 explicitly invalidate silence, inactivity, or bundled consent
- Right to erasure ("right to be forgotten") under Article 17
- Data minimization — collect only what's necessary for specified purposes
- Breach notification within 72 hours of discovery under Article 33
Standard mobile app consent flows are frequently non-compliant. Consent must be granular for each purpose — bundling consent for core functionality with behavioral advertising or GPS tracking renders it invalid.
Device identifiers and behavioral analytics constitute personal data under GDPR and require explicit opt-in before any processing begins.
HIPAA and mobile apps
HIPAA applies when the app creates, receives, transmits, or maintains electronic Protected Health Information (ePHI) on behalf of a covered entity: hospitals, insurers, or health plans. The app developer then becomes a Business Associate and must sign a Business Associate Agreement (BAA).
Three HIPAA rules relevant to mobile apps:
- Privacy Rule — Controls how PHI may be used, shared, or disclosed by covered entities and their associates
- Security Rule — Mandates administrative, physical, and technical safeguards for ePHI (45 CFR 164.312)
- Breach Notification Rule — Requires notifying affected individuals and HHS within 60 days of a breach affecting 500+ individuals
The HITECH Act and 2013 Omnibus Final Rule extended direct liability for Security Rule compliance to Business Associates. BAs face civil monetary penalties ranging from $100 to $50,000+ per violation, up to $1.5 million annually.
RBI digital payment security controls and mobile apps
RBI's DPSC framework (Master Direction RBI/2020-21/74) applies to Scheduled Commercial Banks, Small Finance Banks, Payments Banks, and Credit card issuing NBFCs in India. It's sector-specific (payments/banking) rather than data-category-specific like GDPR/HIPAA.
RBI's prescriptive mobile security mandates include:
- Mandatory app security assessments before launch, with VA half-yearly and PT yearly
- Controls against reverse engineering — code obfuscation, application sandboxing
- Secure communication protocols — TLS with certificate validation
- Transaction anomaly detection and real-time fraud monitoring
- Device binding requirements using hardware, software, and service information
- Jailbreak/root detection — apps must check device integrity and disallow installation on compromised devices
- Version deactivation — older app versions must be deactivated within six months of new release
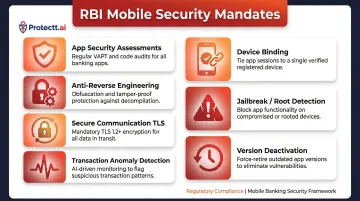
RBI's emphasis on runtime controls distinguishes it from GDPR/HIPAA. Requirements for jailbreak/root detection, anti-hooking protections, and SIM binding prevent account takeover — areas where many apps remain exposed even when they pass static code reviews.
Where GDPR, HIPAA, and RBI standards overlap—and where they diverge
Shared foundation across all three frameworks:
- Encryption of sensitive data in transit (TLS 1.3) and at rest (AES-256)
- Access controls with strong authentication
- Audit logging of data access events
- Incident response and breach notification procedures
- Third-party/vendor risk management (BAAs under HIPAA, processor agreements under GDPR, vendor security assessments under RBI)
These shared controls form the compliance baseline. The friction emerges in how each framework handles retention, consent, and jurisdictional reach—often in ways that directly contradict each other.
Where erasure rights collide with retention mandates: GDPR's Article 17 right to erasure conflicts with HIPAA's requirement to retain ePHI audit logs for 6 years (45 CFR 164.316) and RBI's transaction record-keeping obligations (5–10 years). EDPB Guidelines 01/2025 recommend pseudonymization as the practical resolution—delete direct identifiers to satisfy erasure requests while retaining the underlying pseudonymized transaction data for financial or healthcare audits.
How each framework structures authority over data: GDPR is consent and rights-driven. HIPAA is entity-relationship-driven (covered entity + business associate model). RBI is control-checklist-driven with specific technical mandates. Which framework governs a given data type depends on who the user is, where they're located, and what the transaction involves—and getting that mapping wrong creates simultaneous violations across jurisdictions.
Jurisdictional scope varies sharply: GDPR has the broadest extraterritorial reach—it applies to any app processing EU resident data, regardless of where the company is based. HIPAA applies only when PHI is involved in a covered entity relationship. RBI applies to all entities offering digital payment services in India, regardless of incorporation location.
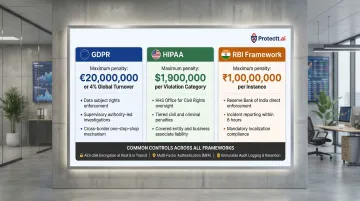
| Framework | Maximum Penalty | Enforcement Model |
|---|---|---|
| GDPR | €20M or 4% of global annual turnover | DPAs issue administrative fines, processing bans, corrective orders |
| HIPAA | Up to $1.5M annually per violation category | HHS OCR uses Resolution Agreements, Corrective Action Plans, CMPs |
| RBI | No uniform penalty table; case-by-case | Statutory powers under Banking Regulation Act: fines and operational bans |
Technical controls that satisfy all three frameworks simultaneously
Encryption as the common baseline
AES-256 for data at rest and TLS 1.3 for data in transit satisfy encryption requirements across all three frameworks. For HIPAA-aligned deployments, NIST SP 800-52 Rev. 2 mandates TLS 1.2 with FIPS-based cipher suites as a minimum and required TLS 1.3 support by January 1, 2024.
RBI goes further with two certificate-specific requirements:
- Certificate validation — web content must not load if SSL/TLS errors are detected
- Certificate pinning (recommended) — ensures the app only trusts specific certificates, blocking man-in-the-middle attacks even when a trusted CA is compromised
Authentication and identity controls
Multi-factor authentication is explicitly or effectively required by all three frameworks:
- HIPAA requires "unique user identification" (45 CFR 164.312(a)(2)(i)); HHS OCR strongly recommends MFA based on risk analysis
- GDPR requires appropriate security measures under Article 32, which includes strong authentication
- RBI explicitly mandates multi-factor authentication for all electronic payments, requiring at least one dynamic or non-replicable factor (OTP, device binding, biometric)
Meeting the letter of MFA requirements is the baseline. More resilient implementations go further with phishing-resistant, passive controls:
- Device binding — RBI mandates hardware, software, and service information combinations to anchor identity to a specific device, preventing credential reuse across sessions
- SIM-based verification — Protectt.ai's Silent Mobile Verification eliminates OTPs entirely by confirming identity directly via carrier networks using proprietary LSAP/3-Way Hairpin technology, with no user action required