
This isn't just frustrating—it's a security vulnerability. Every second waiting for an OTP is an opportunity for fraud, a moment where customers abandon transactions, and a crack in your authentication armor that attackers actively exploit.
This article explains what Silent Mobile Verification (SMV) is, how it works at the network level, and why modern banking apps are rapidly adopting it—not as a nice-to-have feature, but as a foundational security layer that eliminates OTP friction while dramatically reducing fraud risk.
TLDR
- Authentication happens through a cryptographic handshake between the SIM and Mobile Network Operator—no user action, no visible prompt
- Unlike SMS OTPs, SMV cannot be phished, intercepted via SS7 exploits, or stolen through SIM swap attacks
- Banking apps use SMV across login, transaction authorization, and account recovery—keeping security invisible to users
- SMV meets Strong Customer Authentication (SCA) possession factor requirements without relying on user-delivered codes
What is silent mobile verification?
Silent Mobile Verification (SMV) is a passwordless, OTP-less authentication protocol that verifies a user's possession of a registered mobile number by operating through the secure, encrypted infrastructure of the Mobile Network Operator (MNO). No user action required.
Understanding the terminology
SMV goes by several names in the industry, all referring to the same underlying mechanism:
- Silent Network Authentication (SNA)
- Phone Number Verification (PNV)
- Header Authentication
- Number Verify (GSMA CAMARA API standard)
All of these terms describe carrier-level identity verification that happens silently in the background.
How SMV differs from other silent authentication methods
While behavioral biometrics, device fingerprinting, and geolocation are all forms of "silent authentication," SMV is fundamentally different: it operates at the telecom network level, making it uniquely authoritative and tamper-resistant.
The distinction matters in practice:
| Method | How It Works |
|---|---|
| Behavioral biometrics | Analyzes typing patterns, swipe gestures, and device interaction |
| Device fingerprinting | Identifies devices through hardware and software characteristics |
| Silent Mobile Verification | Performs cryptographic verification through the carrier's authentication infrastructure |
The GSMA CAMARA "Number Verification" API defines SMV as a service that "validates user identity by confirming that the provided phone number matches the number associated with the user's device connection to the mobile network operator"—a definition that highlights its network-operator foundation.
The user experience
From the user's perspective, SMV is invisible. They initiate an action—login, payment confirmation, or account recovery—and are verified within 2-4 seconds, with no prompts, no code entry, and no app-switching required.
Compare this to SMS OTP: delivery fails 15-20% of the time, and users must switch apps, read a code, switch back, and type six digits manually. That friction has a cost—up to 15% of users abandon transactions at this exact step.
How does silent mobile verification work?
SMV builds on the same standardized cryptographic system that mobile carriers use to authenticate calls and data sessions: the GSM (Global System for Mobile Communications) authentication framework. The same infrastructure secures billions of mobile calls and data sessions daily.
The SIM authentication handshake
Here's how the cryptographic verification works step-by-step:
1. SIM Provisioning (One-Time Setup)
When your carrier activates your SIM, they provision it with a unique 128-bit authentication key called Ki (Individual Subscriber Authentication Key). This key is stored permanently on your SIM card and in the carrier's Authentication Centre (AuC) database. The Ki is never transmitted after initial provisioning. It exists only in these two secure locations.
2. Authentication Challenge
When an SMV event occurs (you attempt to log in to your banking app), the Mobile Network Operator generates a 128-bit random challenge called RAND and sends it to your device over the mobile data network.
3. Cryptographic Response
Both your SIM card and the carrier's network independently compute a Signed Response (SRES) using:
- The secret Ki
- The random RAND
- A one-way cryptographic function (algorithm A3)
Your SIM performs this calculation internally—you never see it happen, and the Ki never leaves the SIM.
4. Verification
Your SIM returns its computed SRES to the carrier. If the carrier's independently computed SRES matches your SIM's response, authentication succeeds. You're verified—without typing anything.

SIM binding: anchoring identity to hardware
SMV ties verified identity to unique SIM identifiers:
- IMSI (International Mobile Subscriber Identity): Up to 15 digits identifying the subscriber
- ICCID (Integrated Circuit Card Identifier): A unique 10-byte number identifying the physical SIM card
This binding makes it extremely difficult for fraudsters to authenticate using stolen credentials alone—they would need physical possession of the legitimate SIM card, which contains the cryptographic Ki.
The mobile data requirement
That SIM-bound identity only holds if the network can confirm which device is making the request. This is why SMV strictly requires a cellular data connection, not Wi-Fi. The verification relies on IP address correlation: the mobile operator identifies which SIM card is assigned to the IP address making the authentication request.
When your device connects over Wi-Fi, the operator sees your ISP's IP address instead of your mobile IP, breaking the verification chain. Modern implementations solve this through SDK-level controls that route the verification request over the mobile network even when the device is connected to Wi-Fi.
Advanced implementation: Protectt.ai's LSAP/3-Way Hairpin technology
Protectt.ai's proprietary LSAP/3-Way Hairpin technology enables the silent, no-OTP network handshake for banking-grade deployments. Key implementation characteristics include:
- Consistent performance across major mobile network operators
- Automatic routing of verification requests over the mobile network, even when Wi-Fi is active
- Designed to handle real-world edge cases without degrading the user experience
Why SMS OTP authentication is failing banking apps
SMS OTP was never designed as a security mechanism—it was built as a best-effort communication channel. This fundamental design flaw creates multiple attack vectors that fraudsters exploit.
Structural vulnerabilities
SIM Swap Attacks
Fraudsters convince carriers to transfer your phone number to a SIM card they control. Once successful, all your SMS OTPs are delivered directly to the attacker. The FBI IC3 reported $25.9 million in U.S. losses from 982 SIM swap complaints in 2024, though the actual global impact is far higher due to underreporting.
SS7 Protocol Exploits
The Signaling System No. 7 (SS7) protocol that routes SMS messages globally lacks authentication and encryption, allowing attackers with access to telecom infrastructure to intercept messages, track locations, and reroute texts used for two-factor authentication.
Smishing (SMS Phishing)
According to Europol's 2024 IOCTA report, smishing was the most common type of phishing used by fraudsters in 2023, heavily utilized to steal OTPs and banking credentials through social engineering.
Business impact beyond fraud
These attack vectors translate directly into operational and revenue losses. The cost of SMS OTP extends well beyond fraud:
- 15-20% of SMS OTPs never reach users due to network congestion, carrier filtering, or device issues
- Up to 15% of users abandon login or checkout when OTPs are delayed or undelivered
- Failed OTP delivery generates significant inbound support volume
- Each authentication failure erodes customer confidence in your platform

Regulatory pressure
Regulators globally recognize that SMS OTP alone no longer meets the bar for Strong Customer Authentication. Three major frameworks have each taken a clear stance:
- EBA (European Banking Authority): SMS OTP qualifies as a possession factor only if measures prevent SIM swap replication — SIM swap protection is a required control, not optional
- RBI (Reserve Bank of India): Has mandated dynamic two-factor authentication and moved away from SMS OTP alone due to phishing and SIM-swap exposure
- NIST SP 800-63B: States that SMS OTP is not phishing-resistant and is vulnerable to social engineering
Key reasons banking apps need silent mobile verification
Reason 1: eliminating the primary attack vector for account takeover
Banking is the highest-value target for Account Takeover (ATO) fraud. In 2024, ATO fraud resulted in nearly $15.6 billion in reported losses in the U.S., affecting 5.1 million consumers. TransUnion reported that 13.5% of all global digital account creation transactions in 2023 were suspected digital fraud.
How SMV prevents ATO:
- Removes the shared secret: No OTP means nothing to phish, intercept, or steal
- Cryptographic proof of possession: Fraudsters must physically possess the legitimate SIM containing the Ki
- Real-time SIM integrity validation: Detects and blocks authentication attempts from recently swapped SIMs
Unlike SMS OTP, which NIST explicitly categorizes as not phishing-resistant, SMV provides cryptographic authentication that attackers cannot socially engineer or technically intercept.
Reason 2: frictionless experience that protects revenue
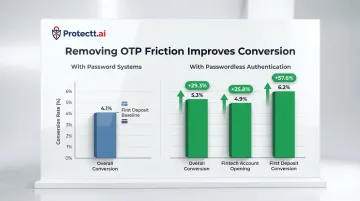
Every authentication step increases drop-off probability. Research shows dramatic conversion improvements when friction is removed:
- Overall conversion rates improved by 29.3% (from 4.1% to 5.3%) when moving from password systems to passwordless authentication
- Fintech account opening conversion improved by 25.8%; first deposit conversion improved by 57.6%
SMV enables critical banking actions—login, re-authentication at transaction time, and high-value transfer confirmation—to happen invisibly, improving both security and engagement metrics at once.
Reason 3: satisfying Strong Customer Authentication (SCA) requirements
Under PSD2 and similar frameworks globally, SCA requires two independent factors from different categories:
- Knowledge (something you know)
- Possession (something you have)
- Inherence (something you are)
The European Banking Authority has clarified that "possession" requires a reliable means to confirm possession through the generation or receipt of a dynamic validation element on the device. SMV satisfies this requirement through:
- Physical SIM card possession (identified by IMSI/ICCID)
- Cryptographic challenge-response authentication
- Protection against replication (the Ki cannot be cloned or extracted)
The GSMA confirms that Number Verify uses the mobile device as a "strong and secure possession factor" underpinned by cryptographic security.
Reason 4: real-time SIM integrity signals
Unlike static credentials, SMV provides dynamic intelligence at the moment of authentication. The GSMA CAMARA SIM Swap API allows banks to query the mobile network in real-time to detect if a SIM card has been recently swapped—the API returns a timestamp of the last MSISDN-to-IMSI pairing change or a boolean yes/no for a defined period (e.g., last 24 hours).
This enables banking apps to:
- Flag suspicious authentication attempts from newly swapped SIMs
- Detect number porting events
- Identify dual SIM anomalies
- Block fraudulent access attempts even when stolen credentials are used
These signals feed directly into fraud decision engines, creating a real-time defense layer that SMS OTP cannot provide.
Reason 5: building the "Invisible Trust" architecture
Banking is moving toward a dual-factor model that combines:
- SMV (What You Have): Cryptographically verified SIM possession
- Biometrics (Who You Are): Face ID or fingerprint
This architecture removes passwords entirely, eliminates the OTP attack surface, and creates seamless authentication flows that complete in seconds. SMV forms the foundational layer of this model: the cryptographic possession factor that, paired with biometric verification, lets users authenticate without ever seeing a prompt.

How Protectt.ai powers silent mobile verification for banking
Protectt.ai delivers Silent Mobile Verification through AppBind, its Zero Trust Device & SIM Binding solution. AppBind sits within Protectt.ai's AI-Native, Full-Stack Mobile App Security Platform — purpose-built for banking, fintech, and financial services environments.
Proprietary technology for banking-grade reliability
Protectt.ai's proprietary LSAP/3-Way Hairpin technology enables the silent, no-OTP network handshake that banking apps require. The Zero Trust Device & SIM Binding feature anchors verified identity to the device-SIM combination, preventing unauthorized access even if credentials are compromised.
Key capabilities:
- Near-instantaneous authentication (2-4 seconds)
- Automatic mobile data routing even on Wi-Fi-connected devices
- Real-time SIM integrity monitoring
- Support for major mobile network operators globally
SDK integration and compliance certifications
Protectt.ai's SDK for iOS and Android integrates directly into existing authentication workflows — no architectural overhaul required. The platform carries certifications that matter specifically to regulated financial institutions:
- ISO 27001 — information security management
- PCI DSS — payment card data security
- ISO 42001 — AI management systems
- ISO 22301 — business continuity management
Proven track record in banking
Leading financial institutions trust Protectt.ai's mobile security platform:
- RBL Bank
- Yes Bank
- Bajaj Finserv
- Equitas Bank
- Karur Vysya Bank
- BSE (Bombay Stock Exchange)
- IIFL Securities
- 5paisa
Vivek Dhavale at Equitas Small Finance Bank notes that Protectt.ai provides "quick, hassle-free, and seamless integration of our mobile banking apps" with in-app analysis and cloud-based processing.
That deployment experience — across banks, NBFCs, and securities firms — translates directly to faster integration and fewer surprises for your security team.

Next steps for banking security teams
If you're exploring OTP replacement, fraud reduction, or compliant-by-design authentication flows, reach out to Protectt.ai at consult@protectt.ai to map SMV against your specific authentication architecture and regulatory requirements.
Frequently asked questions
What is silent mobile verification?
Silent Mobile Verification is a passwordless authentication method that verifies a user's mobile identity by performing a cryptographic handshake between their SIM card and the Mobile Network Operator in the background—requiring no user input, no OTP, and no manual action. The verification typically completes within 2-4 seconds.
Is passwordless authentication more secure than two-factor authentication (2FA)?
Yes — SMV eliminates the shared secret (OTP or password) that fraudsters exploit via phishing and social engineering. It satisfies the possession factor of multi-factor authentication at a cryptographic level, and NIST explicitly distinguishes it from vulnerable SMS OTP methods.
Should banking apps enable silent mobile verification for all users?
SMV is well-suited as the primary authentication layer for most mobile banking interactions. Best practice recommends risk-based fallback to OTP for edge cases such as detected SIM swaps, dual SIM anomalies, or scenarios where mobile data is unavailable, ensuring both security and accessibility.
What is the difference between Silent Mobile Verification and SMS OTP?
SMS OTP sends a shared secret over an insecure channel, vulnerable to SIM swap attacks, SS7 exploits, and phishing. SMV performs cryptographic verification entirely within the telecom network, invisible to the user and inaccessible to attackers, using the secret key stored on the SIM card.
Does Silent Mobile Verification work over Wi-Fi?
SMV requires a cellular connection because verification relies on IP address correlation with the mobile network. Modern SDK implementations resolve this by automatically routing the verification request over mobile data even when the device is on Wi-Fi, keeping in-app banking flows uninterrupted.


