
Introduction
The FBI IC3 recorded 982 SIM swap complaints in 2024, totaling nearly $26 million in losses. The UK reported a 1,055% surge in unauthorized SIM swaps, with nearly 3,000 cases filed. What makes these attacks so damaging: fraudsters drain accounts without ever knowing the password — just by hijacking a victim's phone number.
Banks have layered on OTPs and 2FA, but SIM swap fraud bypasses both. The vulnerability is structural — OTP-based authentication verifies the phone number, not the device or the person holding it.
Device binding closes that gap by cryptographically locking a banking app to one specific physical device.
This guide covers how device binding works, what happens under the hood during enrollment and verification, and why it's become a non-negotiable layer in modern banking app security.
TL;DR
- Device binding cryptographically locks a banking app to one specific device — stolen credentials or hijacked SIMs can't authenticate from another phone
- SIM swap fraud ports a victim's number to an attacker's SIM, then intercepts OTPs to authorize fraudulent transactions
- Defeating this attack requires the original registered device — not just a phone number — to authenticate every session
- Asymmetric cryptography powers it: a private key in tamper-proof hardware on-device, a public key on the backend server
- Even with passwords, phone numbers, and OTPs all compromised, device binding blocks account takeover
What is device binding?
Device binding is a security mechanism that cryptographically links a specific app installation to one physical device—meaning the app will only function on that registered device. Unlike MDM enrollment or simple device registration, which rely on software-level identifiers that can be spoofed, device binding anchors authentication to hardware itself.
Traditional authentication verifies who you are but not where you're authenticating from. Device binding closes that gap by adding device identity as a mandatory factor—one that credentials alone cannot replace.
As mobile-first banking expanded, account takeover attacks built around stolen or transferred credentials followed. Device binding makes the physical device a non-transferable key: stolen passwords become useless without the original phone.
Types of device binding methods
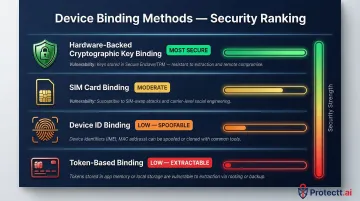
Banking apps can implement device binding through several approaches, but not all provide equal security:
Hardware-backed cryptographic key binding (most secure):
- Uses Android Keystore or iOS Secure Enclave to generate and store private keys
- Private keys remain physically locked in tamper-proof hardware and cannot be extracted
- Meets NIST SP 800-63B AAL3 requirements for non-exportable hardware authenticators
- Provides cryptographic proof of hardware provenance through attestation
SIM card binding:
- Ties authentication to mobile number presence on the device
- Vulnerable when used alone, as SIM swap attacks specifically target this factor
- Most effective when combined with hardware-backed device binding
Device ID binding:
- Uses identifiers like Android ID or IDFV (iOS)
- Easily spoofed through hooking frameworks or device cloning
- Vulnerable to hooking frameworks that modify app behavior at runtime
Token-based binding:
- Relies on software-generated tokens stored on the device
- Tokens can be extracted and replayed on different devices
For banking apps, hardware-backed cryptographic binding is the most defensible option. Identifiers and tokens can be spoofed; hardware-held private keys physically cannot be extracted—even on rooted or jailbroken devices.
How SIM swap fraud targets banking apps
SIM swap attacks exploit a core weakness in mobile carrier processes. Here's how the attack unfolds:
The fraudster contacts a mobile carrier, impersonates the victim using social engineering or stolen personal data (name, date of birth, address), and convinces the carrier to transfer the victim's phone number to a new SIM the attacker controls. A 2020 Princeton University study found that 80% of first SIM swap attempts succeeded — a direct result of weak authentication at carrier call centers.
The attack chain against banking apps:
- Attacker successfully ports the victim's number to their own SIM
- Victim's phone simultaneously loses network service (often the first warning sign)
- Attacker opens the banking app and triggers a password reset
- Password reset OTP arrives on the attacker's SIM
- Attacker gains full account access and initiates fraudulent transactions
- Transaction confirmation OTPs also arrive on the attacker's SIM
The deeper problem is structural: the OTP authenticates a phone number, not the device or the person holding it. Whoever controls that number at the moment the OTP fires receives it — legitimate owner or attacker. NIST SP 800-63B classifies SMS/voice OTP delivery as "RESTRICTED" precisely because verifiers cannot reliably detect device swaps, SIM changes, or number porting events.
The FBI reported $26 million in SIM swap losses in 2024 alone — but high-profile cases illustrate the ceiling far more starkly:
- Three individuals were indicted for a November 2022 attack that drained over $400 million from FTX via SIM swapping
- Nicholas Truglia was sentenced to 18 months for stealing over $20 million through the same method
Password managers protect credentials. Antivirus blocks malware. But neither addresses the core gap: once an attacker has ported a victim's number, nothing in an OTP-centric authentication chain stops a full account takeover. The system sees the same phone number either way — it has no mechanism to tell the legitimate owner's SIM from the attacker's.

How device binding works in a banking app
Device binding operates through a defined sequence—registration, per-session validation, and transaction signing. The security guarantee comes from cryptographic keys generated and stored in hardware that cannot leave the device.
Registration (the initial handshake)
When a user first installs and logs into a banking app, the app generates an asymmetric key pair (public + private) using the device's Trusted Execution Environment—Android Keystore or iOS Secure Enclave. The app sends only the public key to the bank's backend server, which stores it linked to that user's account. The private key never leaves the device.
Advanced implementations combine this with SIM binding. Protectt.ai's Zero Trust Device & SIM Binding, for example, adds silent mobile network verification using proprietary LSAP/3-Way Hairpin technology. Both the physical device and the carrier-verified mobile number must match during registration—providing dual-factor verification without a separate OTP.
Hardware isolation ensures the keys stay protected at rest:
- Android Keystore keeps key material out of the Android system entirely, preventing leaks even during a Linux kernel compromise
- iOS Secure Enclave never handles plain-text keys, making them impossible to export or compromise
Per-session and transaction validation
After registration, every time the user opens the app or initiates a transaction, the app signs the request payload with the private key stored on the device. The backend validates this signature using the stored public key.
If the signature fails—because the request originates from a different device without the private key—access is denied before any transaction proceeds. Even a correctly intercepted session token is useless on a different device; replaying it without the private key signature fails server-side validation.
The backend treats every device as untrusted by default, granting access only when the cryptographic signature matches. NIST AAL3 requires exactly this: authentication via proof of possession of a cryptographic key, enforced through a protocol challenge — not a password or OTP.
What this achieves
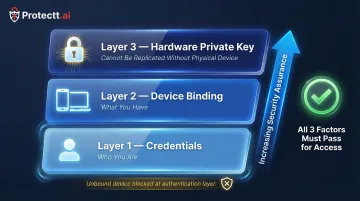
The backend server now trusts device identity as a mandatory factor in every transaction, not just user credentials or phone number possession. Any access attempt from an unbound device is blocked at the authentication layer, before any transaction can be processed.
This creates a security architecture where:
- Credentials verify identity (who you are)
- Device binding verifies possession (what you have)
- The combination cannot be replicated without physical access to the original device
How device binding prevents SIM swap fraud
Device binding directly defeats the SIM swap attack chain. Even if an attacker successfully ports the victim's phone number and intercepts every OTP, they are still operating from an unbound device. The banking app's backend will reject every request because it cannot produce a valid signature from the victim's private key, which physically resides in the hardware of the victim's original device.
The zero-trust principle at work
The server treats every device as untrusted by default and only grants access when the cryptographic signature matches. Phone number, credentials, and OTPs provide no elevated trust on an unregistered device. Traditional authentication assumes that possession of the correct OTP implies legitimate access. Device binding does not.
Combined device + SIM binding
Solutions like Protectt.ai's platform—trusted by banks including RBL Bank, Yes Bank, and Bajaj Finserv—verify both the cryptographic device identity and the carrier-network SIM identity in a single silent handshake. Even a sophisticated attack that bypasses device binding alone must still defeat a carrier-level network verification step that authenticates the physical SIM's unique cryptographic key.
Securing the re-binding process
Legitimate device changes — such as upgrading a phone — require a secure re-binding process with strong multi-factor authentication. Fraudulent re-binding attempts fail because attackers cannot pass the re-authentication requirements. Banks should enforce strict re-binding controls:
- Out-of-band identity verification (not SMS-based)
- Automatic revocation of the old device binding
- Mandatory cooling period before allowing transactions on the new device
- Real-time alerts to users whenever binding changes occur
RBI Digital Payment Security Controls mandate a minimum 12-hour cooling period whenever there is a change in registered mobile number or email ID before allowing any payment transaction—precisely to prevent attackers from exploiting the re-binding process as an alternative attack path.
Device binding best practices for banking apps
Hardware-backed key storage
Banking apps should implement binding using hardware-backed key storage—Android StrongBox/Keystore or iOS Secure Enclave—rather than software tokens or device identifiers. Hardware keys cannot be extracted or cloned even on rooted or jailbroken devices.
Hardware binding alone, however, doesn't protect against compromised runtime environments. Pairing it with RASP (Runtime Application Self-Protection) ensures the environment is clean before the binding check even runs. Key RASP capabilities include:
- Enhanced root and jailbreak detection
- Detailed identification of rooting and hooking apps
- Advanced code injection detection
- Device integrity monitoring and behavioral analysis
- Intelligent device fingerprinting to detect tampering, virtual environments, and OS anomalies
Re-binding governance
Banks must define a clear policy for how users re-bind after a device change. This should require:
- Out-of-band identity verification (not dependent on SMS)
- Automatic revocation of the old binding
- Mandatory cooling period (12–24 hours) before allowing high-risk transactions
- Real-time notification to all registered contact methods
- Fraud detection review for re-binding requests that match suspicious patterns
Compliance alignment
Device binding also supports compliance with multiple regulatory frameworks:
- RBI Digital Payment Security Controls (India): Mandates device binding/fingerprinting of mobile applications with the device and SIM
- PCI DSS: Requires strong authentication for digital payment transactions and secure management of cryptographic keys
- GDPR/DPDP Act: Device identifiers constitute personal data and must be processed lawfully with appropriate security measures
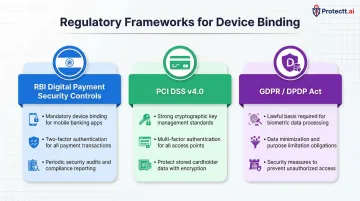
Each framework carries specific technical requirements — knowing which applies to your institution determines how binding must be implemented and audited.
Frequently asked questions
What does device binding mean?
Device binding is the process of cryptographically linking a specific app installation to one physical device, so that app can only function and authenticate from that registered device. This makes stolen credentials useless without the original phone.
What is the device binding process?
On first login, the app generates a private-public key pair in the device's secure hardware, sends the public key to the server, and then signs all future requests with the private key. The server verifies every session is coming from the original registered device by validating the cryptographic signature.
How can security teams monitor and manage device binding in banking apps?
Security and IT teams monitor device binding through backend event logs, which capture every binding registration, change, and revocation in real-time. Most enterprise mobile security platforms also provide dashboards where teams can view active bound devices per user and revoke suspicious registrations immediately.
What is SIM swap fraud and why is it dangerous for banking apps?
SIM swap fraud involves tricking a mobile carrier into transferring a victim's phone number to the attacker's SIM, allowing the attacker to receive OTPs and bypass SMS-based 2FA to take over banking accounts. It's dangerous because it defeats the most common form of multi-factor authentication without any technical expertise.
Can device binding prevent account takeover even if an OTP is compromised?
Yes. Device binding requires a valid cryptographic signature from the original device's private key on every request, so an attacker who has the correct OTP but is on an unbound device will still be blocked by the backend. The OTP alone is insufficient without device-level cryptographic proof.
Is device binding mandatory for banking apps under current regulations?
While specific mandates vary by jurisdiction, regulators including RBI (India) and standards like PCI DSS increasingly require strong device-level authentication controls for mobile banking. In India, the RBI's digital payment security framework explicitly mandates device binding as a required control for meeting strong customer authentication standards.


